What are the Ransomware attacks and preventing ransomware from being devasting
What are Ransomware attacks?
Ransomware attacks are a type of malicious cyber attack where a hacker or a group of hackers encrypts the victim’s files or locks them out of their computer system, holding the data hostage. The attacker then demands a ransom payment, typically in the form of cryptocurrency, in exchange for restoring access to the encrypted files or systems.
Ransomware attacks can be delivered through various methods, including:
- Phishing Emails
- Malvertising
- Exploit Kits
- Remote Desktop Protocol (RDP) Attacks.
- Phishing Emails: The attacker sends fraudulent emails that appear legitimate, tricking the victim into clicking on a malicious link or downloading an infected attachment. Once executed, the ransomware encrypts the victim’s files.
- Malvertising: Malicious advertisements on websites or online platforms contain hidden code that downloads and installs ransomware onto the victim’s system when clicked.
- Exploit Kits: Cybercriminals use software vulnerabilities in outdated or unpatched systems to deploy ransomware. These vulnerabilities can be found in operating systems, web browsers, or other software.
- Remote Desktop Protocol (RDP) Attacks: Attackers exploit weak or compromised RDP credentials to gain unauthorized access to a victim’s system and deploy ransomware.
Once the ransomware is executed, it begins encrypting files on the victim’s device or network, making them inaccessible without the decryption key. The attacker then presents a ransom note, typically displayed on the victim’s screen or delivered through a text file, explaining the situation and providing instructions for making the ransom payment.
Paying the ransom is not recommended, as it does not guarantee that the attacker will provide the decryption key or restore access to the files. Additionally, paying the ransom encourages further criminal activity and funds the development of more sophisticated ransomware.
Ransomware attacks can have severe consequences, resulting in data loss, financial loss, business disruptions, and reputational damage. That’s why it’s crucial to implement preventive measures, such as strong cybersecurity practices and employee awareness training, to minimize the risk of falling victim to a ransomware attack.
Preventing ransomware from being devasting.
Preventing ransomware attacks from being devastating requires a multi-layered approach involving both proactive measures and reactive strategies. Here are some steps you can take to reduce the impact of ransomware:
- Regularly Back up Your Data: Implement a robust backup strategy to ensure critical data is regularly and securely backed up. Keep multiple copies of backups, store them offline or in a separate network, and periodically test their restoration process.
- Keep Software Updated: Frequently update all software, including operating systems, applications, and security solutions, to patch any known vulnerabilities. Enable automatic updates whenever possible to ensure timely protection against emerging threats.
- Use Reliable Security Software: Install reputable antivirus and anti-malware software on all devices. Keep them updated and perform regular system scans to detect and remove any potential threats.
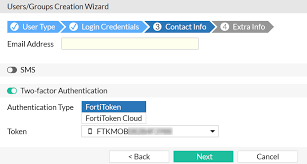
- Employ Strong Passwords and Multifactor Authentication (MFA): Use unique, complex passwords for all accounts and avoid using the same password across multiple platforms. Enable MFA whenever available to add an extra layer of security.
- Be Cautious of Suspicious Emails and Links: Train yourself and your employees to recognize phishing emails and malicious links. Be wary of unsolicited emails, especially those containing attachments or requesting sensitive information. Use email filters to block or flag suspicious emails.
- Educate Employees: Conduct regular cybersecurity awareness training sessions to educate employees about the risks of ransomware and other cyber threats. Teach them how to identify potential threats and what actions to take to mitigate the risks.
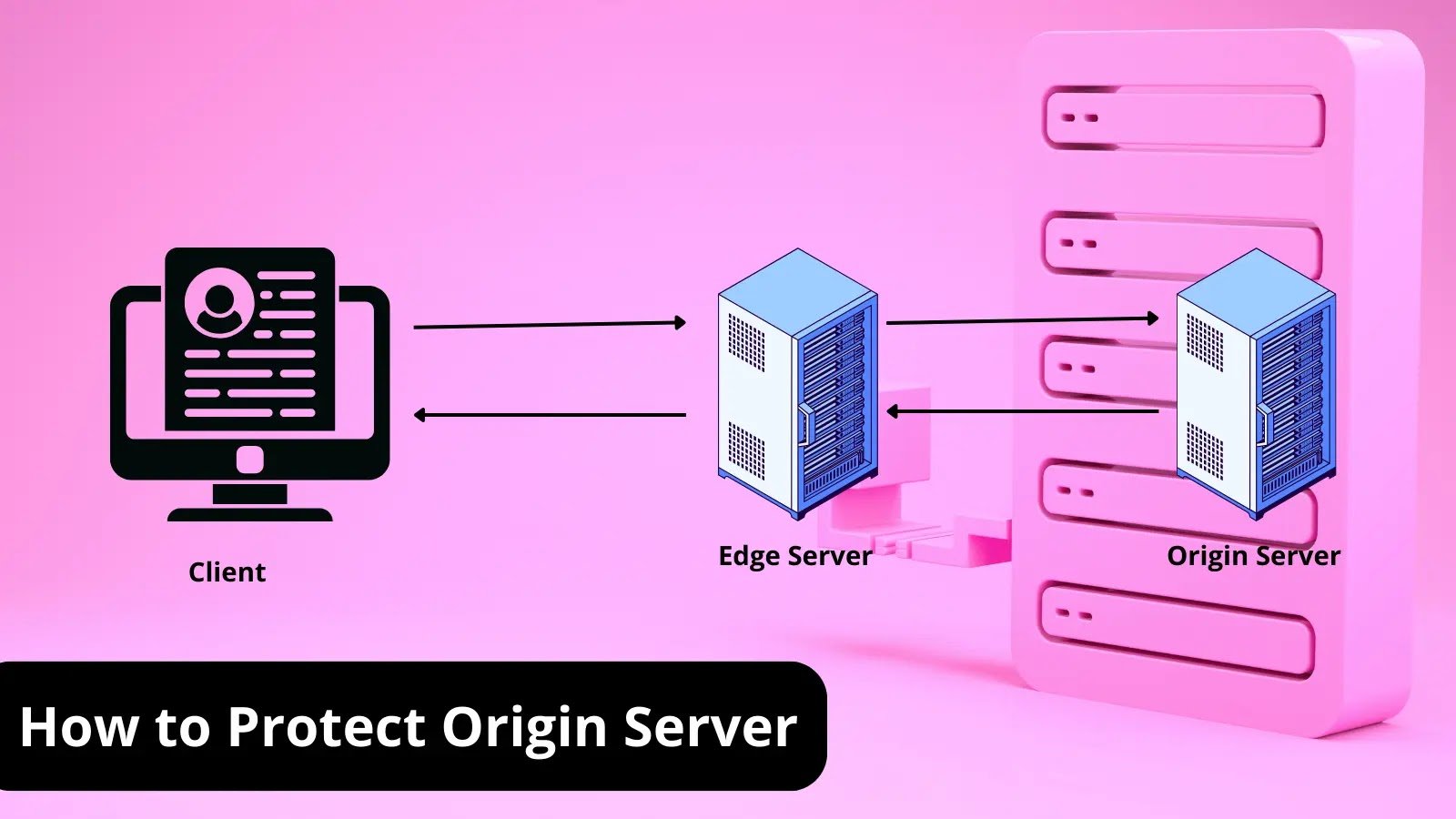
- Implement Network Segmentation: Divide your network into segments or zones, separating critical systems from less sensitive ones. This can limit the lateral movement of ransomware within your network and reduce the potential damage.
- Restrict User Privileges: Assign user privileges based on the principle of least privilege (PoLP). Users should only have the access rights necessary for their specific roles. Limiting privileges can help prevent ransomware from spreading across the network.
- Implement Application Whitelisting: Use application whitelisting to allow only approved and trusted applications to run on your systems. This prevents unauthorized software, including ransomware, from executing.
- Regularly Test Incident Response and Disaster Recovery Plans: Develop and test your incident response and disaster recovery plans to ensure you can effectively respond to and recover from a ransomware attack. Regular testing helps identify weaknesses and allows for improvements.
- Monitor Network Activity: Implement robust network monitoring tools to detect any suspicious activities or anomalies. Intrusion detection systems (IDS) and security information and event management (SIEM) solutions can help identify potential ransomware attacks in real-time.
- Establish Incident Response Procedures: Have a well-defined incident response plan in place, outlining the steps to be taken in case of a ransomware attack. This plan should include procedures for isolating affected systems, notifying appropriate personnel, and engaging with law enforcement if necessary.
Remember, while these measures significantly reduce the risk of a ransomware attack, it’s important to stay vigilant and continuously adapt your security practices as new threats emerge.