How does Privileged Process Automation Work?
Privileged Process Automation (PPA) refers to the automation of privileged tasks and processes within an organization’s IT infrastructure. It involves using specialized software or tools to streamline and secure the execution of privileged operations, such as system administration tasks, application configuration changes, or security-related actions. Here’s a general overview of how privileged process automation works:
- Identification of Privileged Processes: The first step in PPA is identifying the processes or tasks that require privileged access or elevated privileges to be executed. This includes activities like server provisioning, user management, software installations, or system configuration changes.
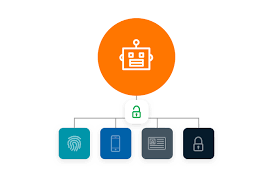
- Access Control and Authentication: PPA solutions typically have robust access control mechanisms to ensure that only authorized individuals or systems can initiate and perform privileged processes. This involves authentication mechanisms such as multi-factor authentication, integration with identity and access management systems, and role-based access control to enforce the principle of least privilege.
- Workflow Design: PPA solutions allow organizations to define and configure workflows that specify the steps, conditions, and approvals required to execute privileged processes. These workflows can be customized to match the organization’s specific requirements and security policies.
- Automated Execution: Once the workflow is defined, PPA solutions automate the execution of privileged processes. The automation may involve executing predefined scripts, commands, or actions on target systems or applications. The PPA solution ensures that the necessary credentials or access tokens are securely retrieved and used during the process execution.
- Auditing and Logging: PPA solutions include robust auditing and logging capabilities to provide visibility and accountability. They capture detailed logs of privileged process executions, including information such as the user or system initiating the process, the actions performed, and the outcome. These logs are critical for compliance purposes, forensic investigations, and identifying potential security issues.
- Monitoring and Alerting: PPA solutions often include real-time monitoring and alerting features. They can detect anomalies, unusual activities, or unauthorized access attempts during privileged process automation. Alerts can be sent to administrators or security teams, enabling them to respond promptly to any potential security incidents.
- Reporting and Analytics: PPA solutions provide reporting and analytics capabilities to gain insights into privileged process automation activities. Reports can include information on process execution times, success rates, resource utilization, and compliance status. This data can help organizations identify areas for improvement, optimize workflows, and demonstrate compliance with relevant regulations.
- Integration and Orchestration: PPA solutions often integrate with existing IT infrastructure, including identity and access management systems, ticketing systems, configuration management databases (CMDB), or security information and event management (SIEM) platforms. Integration allows for seamless data exchange, centralized management, and coordination of privileged processes with other IT processes.
Overall, privileged process automation streamlines and secures the execution of privileged tasks by automating workflows, enforcing access controls, and providing comprehensive auditing and monitoring capabilities. It reduces the risk of human error, ensures consistency, enhances security, and improves operational efficiency in managing and executing privileged operations within an organization’s IT environment.