FBI Warns: Russian Government Hackers Targeting Critical Networking Infrastructure The digital defenses of critical infrastructure are under a sophisticated and sustained assault. The Federal [...]
The digital battlefield continues to evolve, and with it, the sophistication of cyber threats. One persistent and devastating tactic remains the Distributed Denial-of-Service (DDoS) [...]
For cybersecurity professionals, developers, and IT teams, the rapid deployment and consistent configuration of testing environments are paramount. Kali Linux, a cornerstone in this [...]
Unauthenticated RCE: Critical vtenext CRM Vulnerabilities Expose Organizations In the intricate landscape of enterprise resource planning, Customer Relationship Management (CRM) solutions are the bedrock [...]
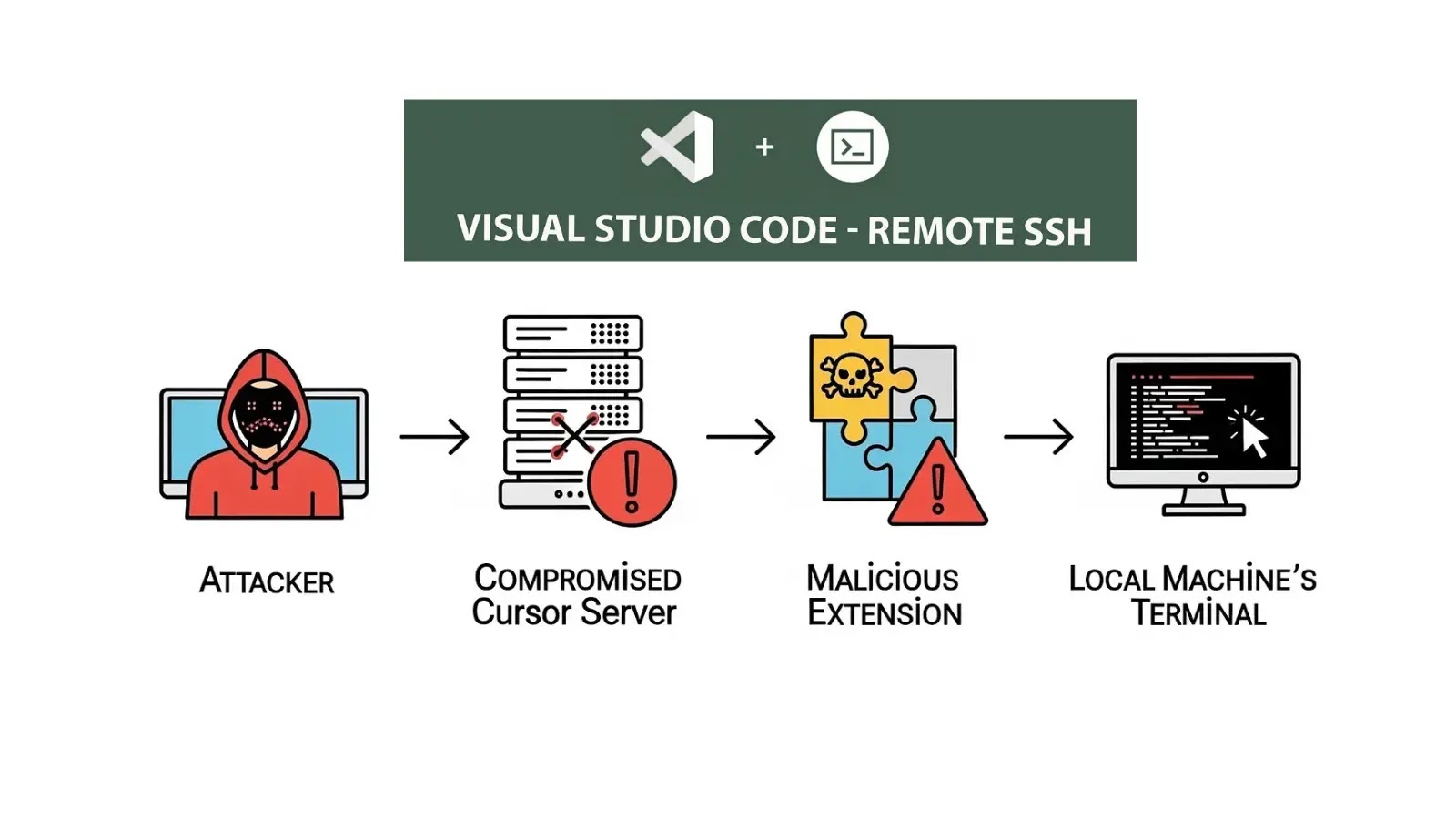
For many developers and IT professionals, the Microsoft VS Code Remote-SSH extension is an indispensable tool, seamlessly bridging the gap between local development environments [...]
Weaponized AI Summaries: A New Horizon for Ransomware Distribution The landscape of cyber threats is in constant flux, with adversaries perpetually refining their tactics. [...]
Urgent Security Alert: 0-Click Zendesk Account Takeover Puts Organizations at Risk A severe vulnerability has been uncovered within Zendesk’s Android SDK implementation, allowing for [...]
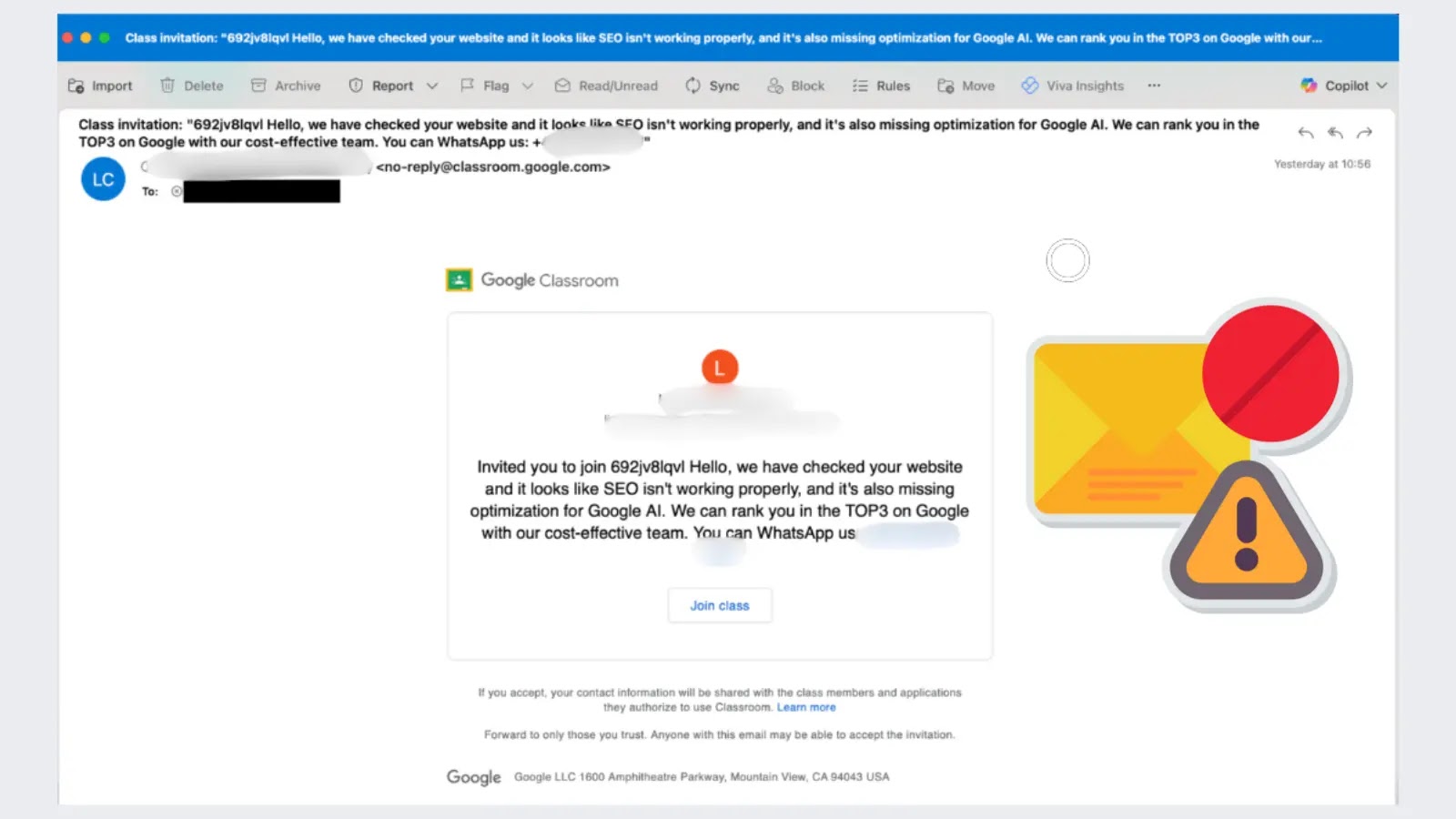
The digital threat landscape is perpetually shifting, with threat actors continuously innovating their tactics to circumvent established security measures. A recent, deeply concerning development underscores [...]
As the academic year commences, students, parents, and educational institutions face a new, insidious threat: Artificial Intelligence (AI)-powered online scams. Cybercriminals are increasingly leveraging [...]
The digital landscape is a battleground where cybercriminals constantly evolve their tactics to compromise unsuspecting users. A particularly insidious and effective method involves mimicking [...]