converge your vision and values
🔐 Network Security Assessment by Teamwin Global
Identify Vulnerabilities. Mitigate Risks. Secure Your Business.
Stay ahead of cyber threats with Teamwin Global’s expert-led network security assessments. We uncover hidden risks, perform in-depth vulnerability scans, and deliver a clear, actionable risk mitigation strategy—tailored to your business.
✅ Vulnerability Scanning & Threat Detection
✅ Penetration Testing & Risk Profiling
✅ One Time Dark Web scaning, Impersination scan, threat inteligence and website vulnarbility scan reports
✅ Compliance-Ready Reports & Remediation Plans
Expertise and Experience:
Highly Skilled Team: Our team consists of certified professionals with extensive experience in various IT domains.
Comprehensive Solutions:
End-to-End Services: We offer a wide range of services, including network management, cybersecurity, cloud solutions, and IT consulting.
why choose us

Our Cyber Security & Secure networking Services
1. What is Data Center Networking? 🖧 🖧 Connects servers, storage, and devices within a data center ⚡ Enables high-speed data transfer, redundancy, and scalability [...]
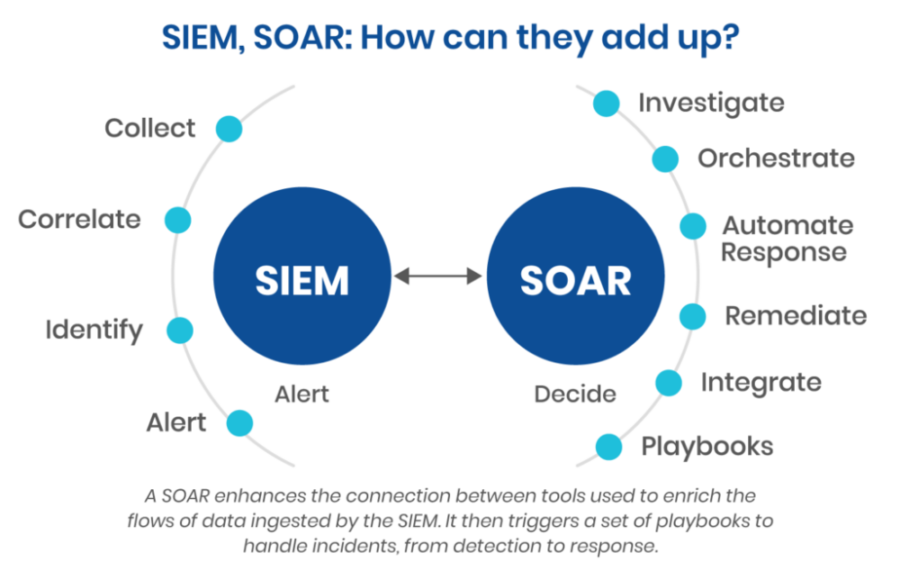
🧠 SIEM & SOAR Solutions | Real-Time Threat Detection & Automated Response – Teamwin Global 📌 Overview Centralize your security data and automate incident response [...]
At Teamwin Global, we provide end-to-end cybersecurity solutions built for today’s digital threats. Backed by industry leaders like Seqrite, CrowdStrike, and Microsoft, we help secure [...]
Articles from the latest news
Latest Tech Articles news
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Multiple Vulnerabilities in GitLab Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: HIGH Software Affected GitLab Community Edition [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Multiple Vulnerabilities in Mozilla Products Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: HIGH Software Affected Mozilla Firefox [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Multiple Vulnerabilities in PostgreSQL Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: HIGH Software Affected PostgreSQL 14 versions [...]