The Relentless Ascent of Qilin Ransomware: Dominating the Attack Landscape in July The digital battleground is in constant flux, and July 2025 painted a [...]
The cybersecurity landscape currently faces a pressing threat: highly personalized phishing attacks. Gone are the days of simplistic, easily detectable bulk emails. Threat actors [...]
A sinister new threat has emerged on the cybersecurity landscape, directly impacting organizations reliant on Fortinet’s FortiSIEM solution for their security operations. Cybersecurity researchers at [...]
Unveiling Top-Tier API Protection in 2025: Safeguarding Your Digital Backbone In our interconnected digital landscape, Application Programming Interfaces (APIs) serve as the fundamental communication [...]
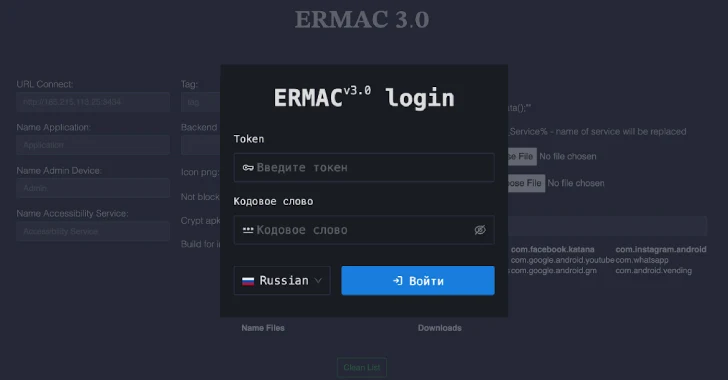
The ERMAC V3.0 Banking Trojan: A Deeper Dive into Exposed Infrastructure The digital landscape is a constant battleground, and the recent exposure of the [...]
Corporate networks face a persistent and evolving threat landscape. Organizations widely adopt collaboration platforms like Microsoft Teams for seamless communication and productivity. However, this [...]
In a stark reminder of fundamental cybersecurity principles, the complete source code for ERMAC v3.0, an advanced Android banking trojan, has been exposed. This significant [...]
The digital landscape is a constant battleground, and for network defenders, anticipating the next attack vector is paramount. A critical new vulnerability, recently disclosed [...]
Unpacking the ImageMagick Vulnerabilities: A Deep Dive into Memory Corruption and Integer Overflows ImageMagick, a cornerstone in the world of open-source image processing, underpins [...]
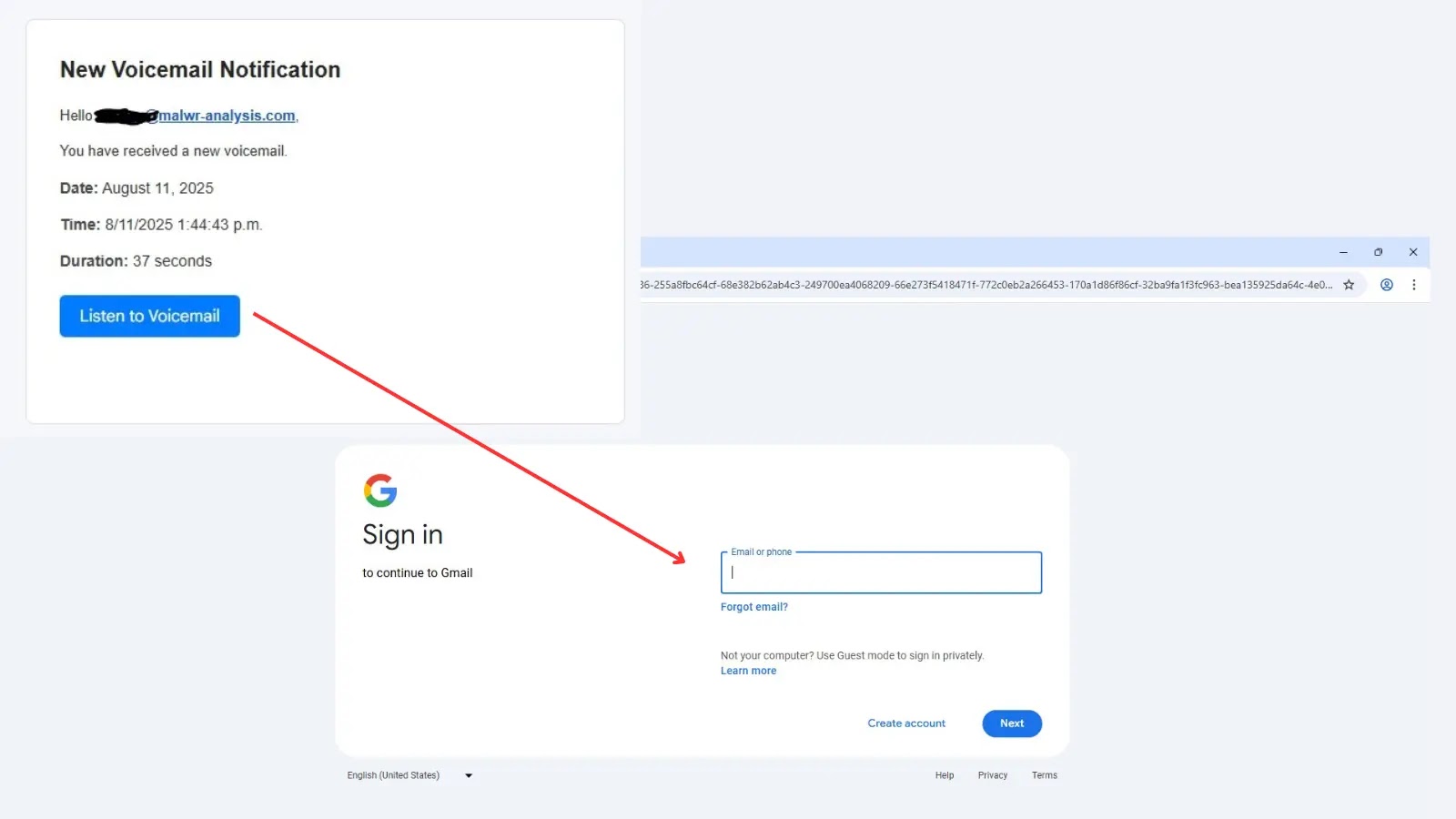
Unmasking the Imposter: A New Gmail Phishing Attack Exploits Legitimate Infrastructure In the evolving landscape of cyber threats, attackers constantly refine their tactics. A [...]