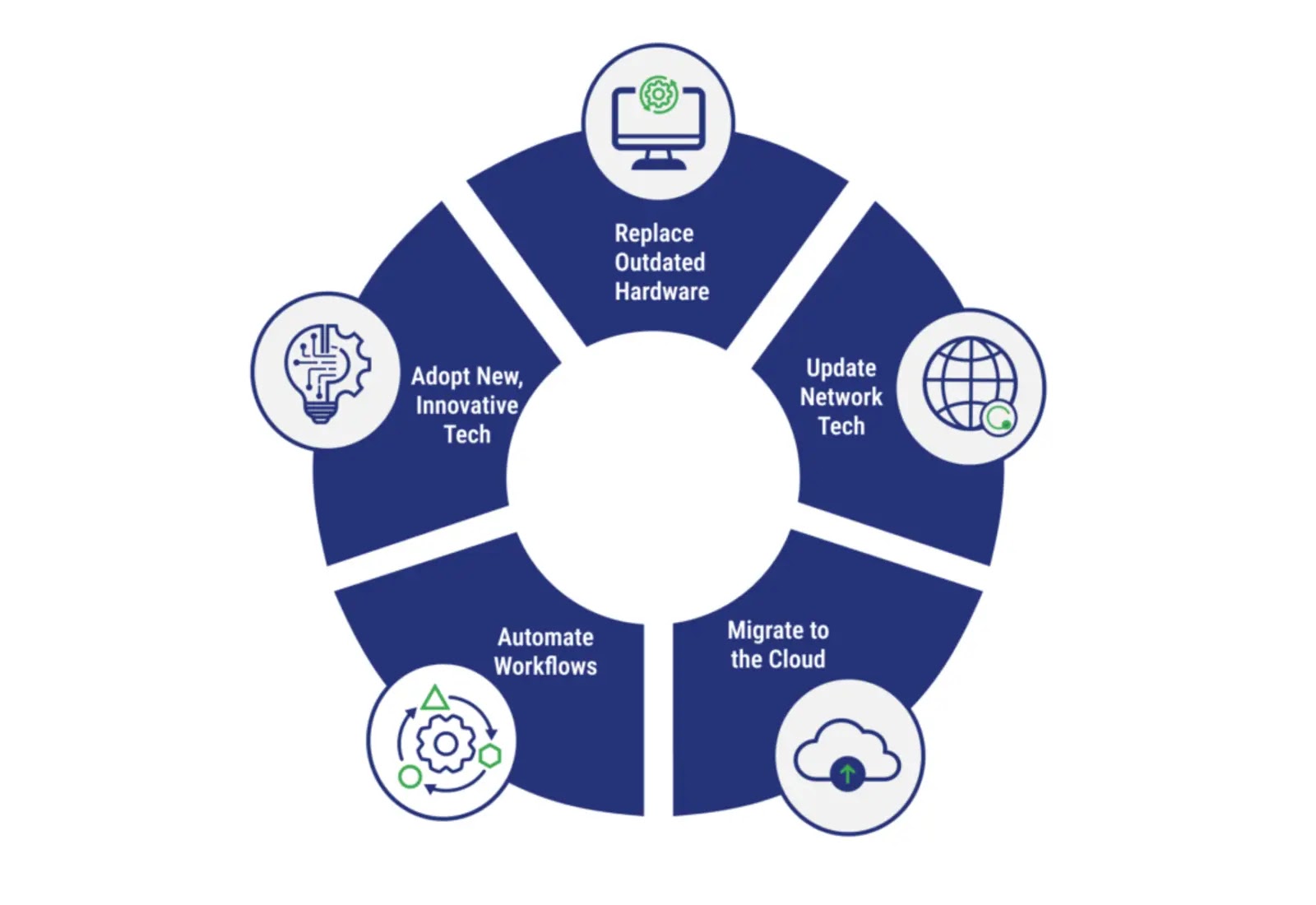
Navigating the Evolving IT Landscape: Why Modernization is Non-Negotiable in 2025 The pace of technological change shows no signs of slowing. For organizations in [...]
The digital landscape is a constant battleground, relentlessly challenging even the most sophisticated defense mechanisms. A stark reminder of this perpetual arms race comes from [...]
In the relentless battle against sophisticated cyber threats, speed and precision are paramount. Every second counts when dissecting malicious code and understanding its impact. [...]
The geopolitical landscape of cyber espionage continues to evolve, with nation-state actors pushing the boundaries of attack sophistication. Recent reports detail a chilling new [...]
North Korean APT Hackers Poison CI/CD Pipelines: A New Frontier in Cyber Espionage The digital landscape is a constant battleground, and state-sponsored threat actors continually [...]
The digital threat landscape is in constant flux, but some attack methodologies stand out for their increasing sophistication and elusive nature. A recent, highly [...]
The Cryptocurrency Ransomware Bonanza: How TrickBot Fuels a $724 Million Extortion Engine The relentless threat of ransomware continues to redefine the contours of cybersecurity. [...]
The cyber threat landscape constantly evolves, but few developments are as concerning as a sophisticated campaign masquerading as a benign educational tool. A new [...]
In the high-stakes world of cybersecurity, understanding the capabilities and strategies of state-sponsored threat actors is paramount. Recent revelations concerning the Chinese state-sponsored hacking [...]
Unmasking DoubleTrouble: The Emerging Threat to Mobile Banking Security In the relentless landscape of cyber threats, a sophisticated new banking trojan, aptly named DoubleTrouble, [...]