The cybersecurity landscape just became more perilous for organizations relying on Citrix solutions. CISA has issued a critical alert, adding three high-risk Citrix vulnerabilities [...]
In a significant escalation of cyber reconnaissance activities, threat actors have launched a massive, coordinated scanning campaign targeting Microsoft Remote Desktop Protocol (RDP) services. [...]
The digital perimeter of many organizations relies heavily on secure and efficient access management. When critical components like Citrix NetScaler ADC (Application Delivery Controller) [...]
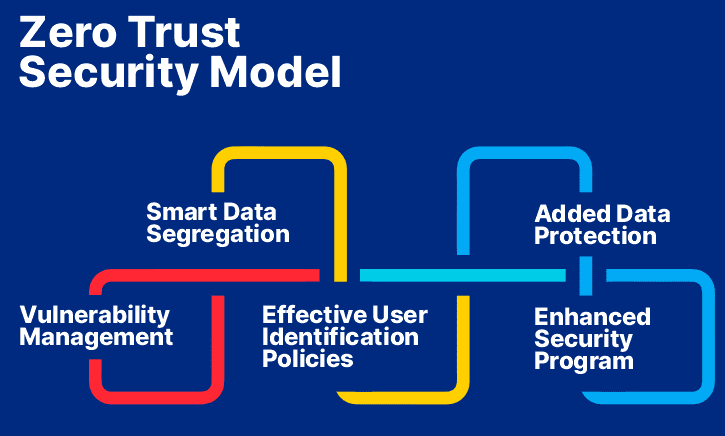
In today’s digital age, where cyber threats are increasingly sophisticated and pervasive, traditional security models that rely on implicit trust are no longer sufficient. [...]
Urgent Warning: New Stealthy Malware Targets Cisco, TP-Link, and Other Routers for Remote Control The digital perimeter of our networks is under constant assault, [...]
Organizations worldwide face an escalated threat from a familiar adversary: the Underground ransomware gang. After a period of relative dormancy, this insidious group has [...]
Unpacking the Threat: New Zip Slip Vulnerability Emerges The seemingly innocuous act of decompressing a ZIP file can, under certain conditions, open a dangerous [...]
In the intricate world of operational technology (OT) and industrial control systems (ICS), security vulnerabilities can have far-reaching implications, extending from production downtime to [...]
The convergence of artificial intelligence and enterprise-grade platforms brings immense power, but it also introduces new attack vectors that skilled threat actors can exploit. [...]
Unmasking CVE-2025-50975: Persistent XSS in IPFire’s Firewall Interface The digital perimeter of any organization relies heavily on robust firewall solutions. When even these critical [...]