In the evolving landscape of enterprise software, critical vulnerabilities can emerge that pose significant threats to organizational security. A recent discovery in Progress OpenEdge’s AdminServer [...]
Windows Defender, often hailed as a cornerstone of endpoint security in Microsoft environments, has long been the unsung hero protecting countless systems from an [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Multiple vulnerabilities in Google Chrome for Desktop Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: HIGH Software Affected [...]
Unmasking the Threat: Atomic Stealer Disguised as Cracked Software Targets macOS Users The allure of “free” software often masks a more sinister reality, especially [...]
Lazarus APT Leverages ClickFix Technique to Compromise Critical Data In the evolving landscape of cyber warfare, sophisticated threat actors continuously refine their tactics. One [...]
In an increasingly interconnected digital landscape, the security of customer data stands paramount. News of a data breach at a significant cybersecurity vendor like [...]
Malicious Email Campaign Targets U.S.-China Trade Talks: A Deep Dive into Cyber Espionage The intricate world of international diplomacy just became a battleground for [...]
Following a cybersecurity incident, the clock starts ticking. Forensic investigators must swiftly piece together the attack chain, identify compromised assets, and understand the extent [...]
The digital landscape is fraught with perils, and few threats are as insidious as remote code execution (RCE) vulnerabilities. When a popular open-source content [...]
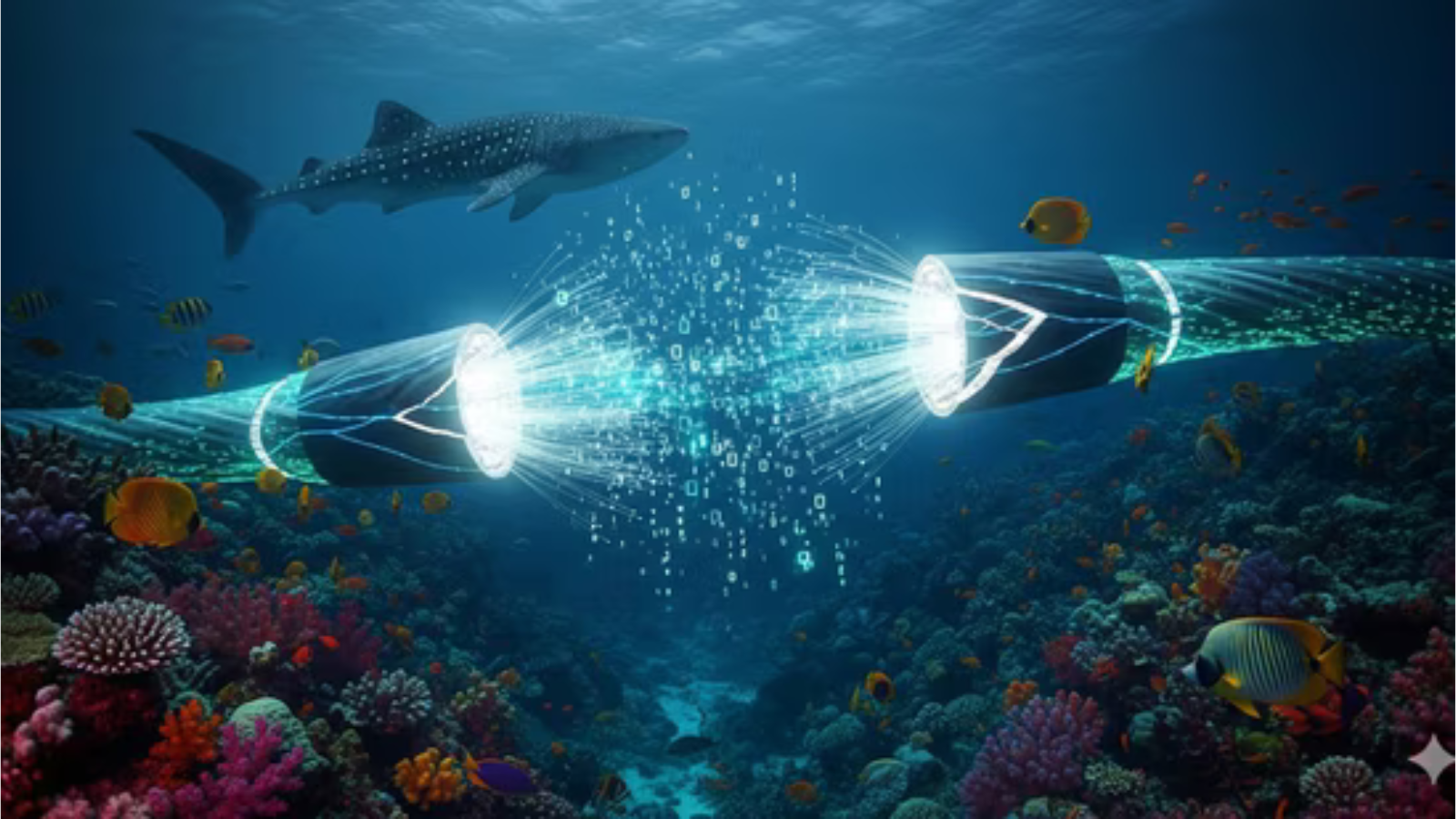
Unraveling the Red Sea Undersea Cable Incident: Impact on Microsoft Azure The intricate web of global connectivity, often taken for granted, is remarkably fragile. [...]