The digital landscape continually presents new cybersecurity challenges, and even the most trusted applications aren’t immune. A recent, sophisticated state-sponsored attack targeting the update [...]
Unmasking CRESCENTHARVEST: A New Cyberespionage Campaign Exploiting Iranian Unrest The geopolitical landscape often serves as fertile ground for cyberattacks, and a sophisticated new threat actor [...]
Ransomware Strikes Washington Hotel in Japan: An In-Depth Analysis In an increasingly interconnected world, the hospitality industry, a cornerstone of global travel and tourism, [...]
The dark web’s shadowy corners often brew unsettling narratives, but occasionally, they present us with curious cases that challenge our perceptions of cybercriminal efficiency. [...]
The Critical Flaw: Insecure Super Admin APIs in Dava India A significant cybersecurity incident has brought to light the precarious state of data security [...]
The digital landscape is a minefield of data privacy concerns. When a major technology firm like Lenovo faces accusations of compromising user data, it sends [...]
The Silent Threat: How QR Codes Are Becoming Phishing and Malware Launchpads QR codes have seamlessly integrated into our daily lives, transforming how we [...]
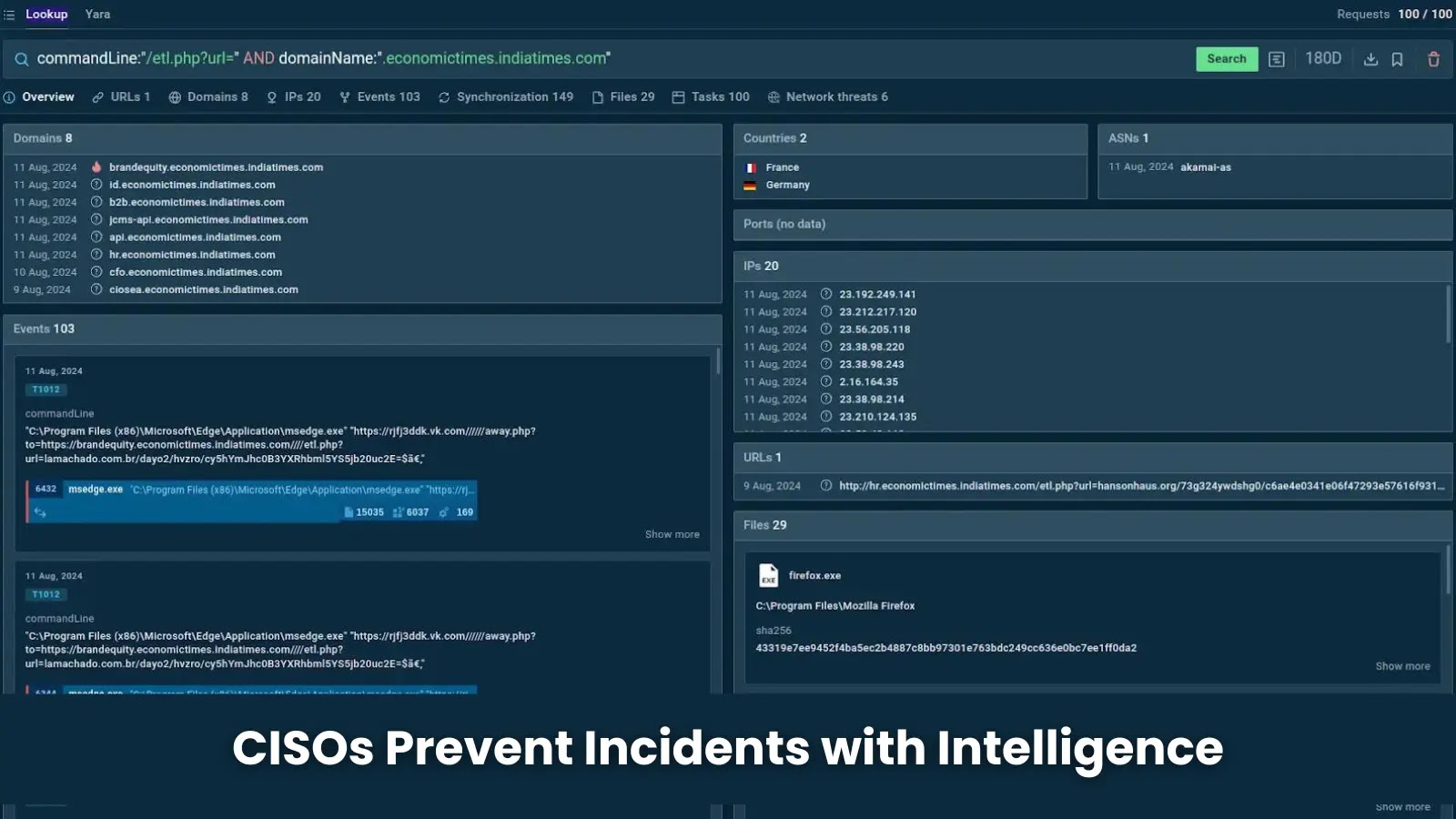
Somewhere, right now, a sophisticated threat actor is meticulously probing the defenses of an organization that believes itself impenetrable. This company has invested heavily in [...]
The open-source ecosystem, a cornerstone of modern software development, often operates on a foundation of trust. However, this trust can be a double-edged sword, as [...]
DigitStealer: macOS Infostealer Exposes Critical Infrastructure Gaps The cyber landscape is continually reshaped by new threats, and the recent surge in activity from DigitStealer [...]