—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Multiple Vulnerabilities in SolarWinds Serv-U Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: CRITICAL Software Affected SolarWinds Serv-U [...]
Urgent Patch Required: Critical FreeBSD Vulnerability Exposes Systems to Full Compromise A severe security vulnerability in FreeBSD, tracked as CVE-2025-15576, demands immediate attention from system [...]
Recent disclosures from Zyxel have sent ripples through the cybersecurity community, revealing a critical array of vulnerabilities within their networking devices. These flaws, spanning across [...]
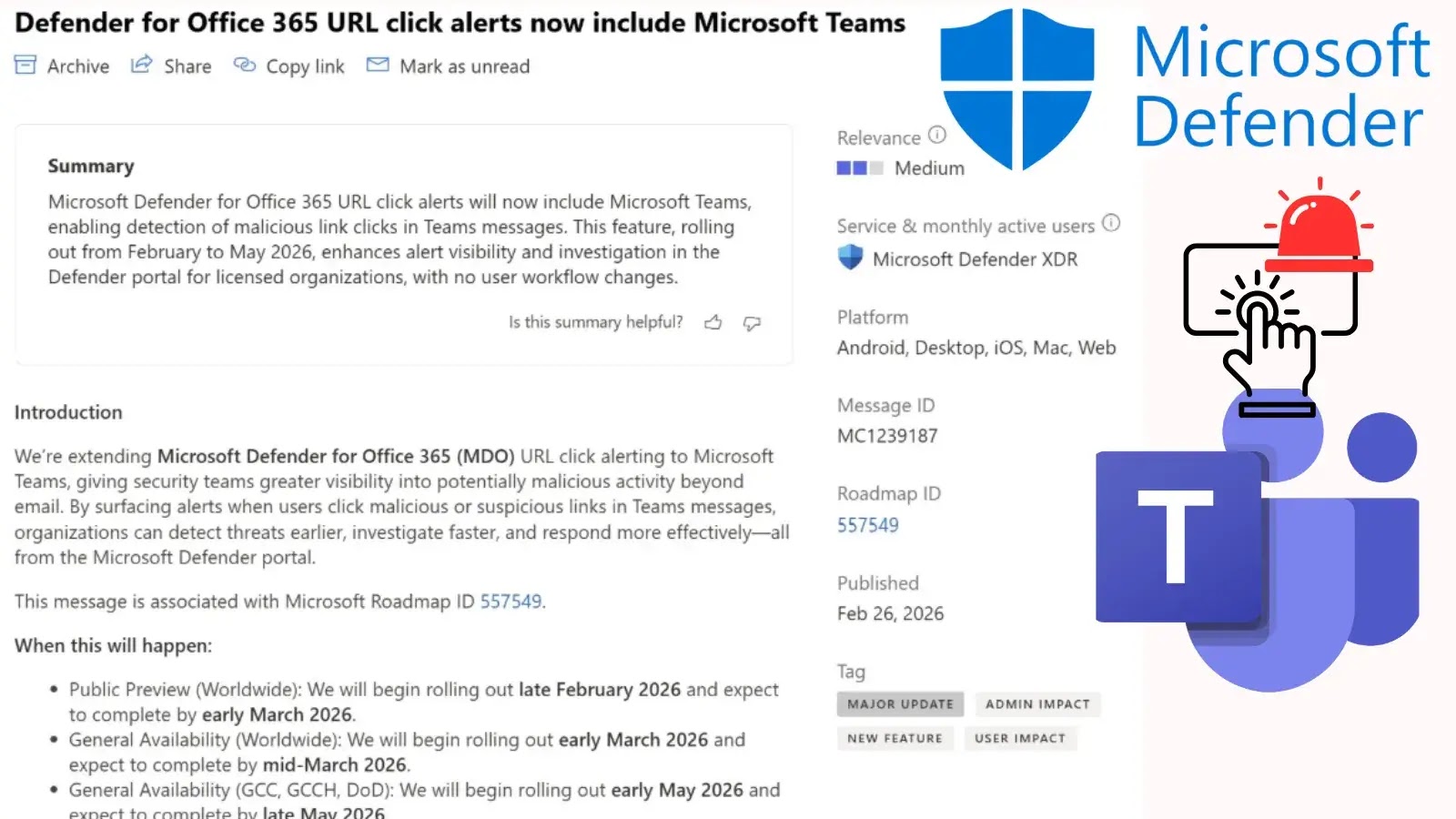
Microsoft Defender Extends URL Click Alerts to Fortify Microsoft Teams Security The landscape of cyber threats is continuously shifting, with attackers increasingly targeting collaborative platforms [...]
Urgent Alert: Juniper Networks PTX Vulnerability Poses Full Router Takeover Threat A critical security vulnerability has sent ripples through the networking industry, specifically impacting high-performance [...]
The Deceptive Lure: Microsoft Defender Uncovers Gaming Utility Campaign Delivering RATs The digital playground, often a source of entertainment and escape, is increasingly becoming a [...]
The cybersecurity landscape has always grappled with the elusive goal of absolute security. For decades, air-gapped systems stood as the gold standard, isolated from the [...]
In a significant cybersecurity development, critical vulnerabilities discovered in Anthropic’s Claude Code, an AI-powered command-line development tool, were found to pose a severe threat, potentially [...]
The Odido Data Breach: A Million Records Exposed After Failed Extortion The digital landscape continues to present formidable challenges for even the most robust organizations. [...]
The silent threat of exposed API keys has taken a significant and concerning turn. For years, Google developers were guided to embed API keys—distinctively formatted [...]