DragonForce Ransomware Group: A Cartel-Like Expansion Threatening Businesses Globally The digital threat landscape is in a constant state of flux, with new and increasingly sophisticated [...]
A disturbing alert has just been issued by the Cybersecurity and Infrastructure Security Agency (CISA), adding a critical code execution vulnerability in Notepad++ to [...]
The digital landscape often feels like a minefield, with threats lurking where we least expect them. A recent discovery has shed light on a [...]
In the constant cat-and-mouse game of cybersecurity, threat actors continuously innovate to evade detection. A particularly concerning development is the rise of Operational Relay Box [...]
ARP Spoofing Attack and ARP Poisoning: Dynamic ARP Inspection (DAI) Defense In today’s interconnected digital landscape, network security is of paramount importance. One of the [...]
In the high-stakes world of blockchain and cryptocurrency development, trust is paramount. Yet, even the most vigilant developers can fall prey to sophisticated social engineering [...]
For years, a Virtual Private Network (VPN) has been touted as the go-to solution for online privacy, a digital cloak of invisibility shielding users [...]
The Trojan in Your Inbox: Malicious Outlook Add-in Steals Credentials and Credit Card Data In a significant and concerning development for email security, a [...]
The digital landscape is a constant battleground, and even the most vigilant defenders can be caught off guard by evolving threats. Following a significant law [...]
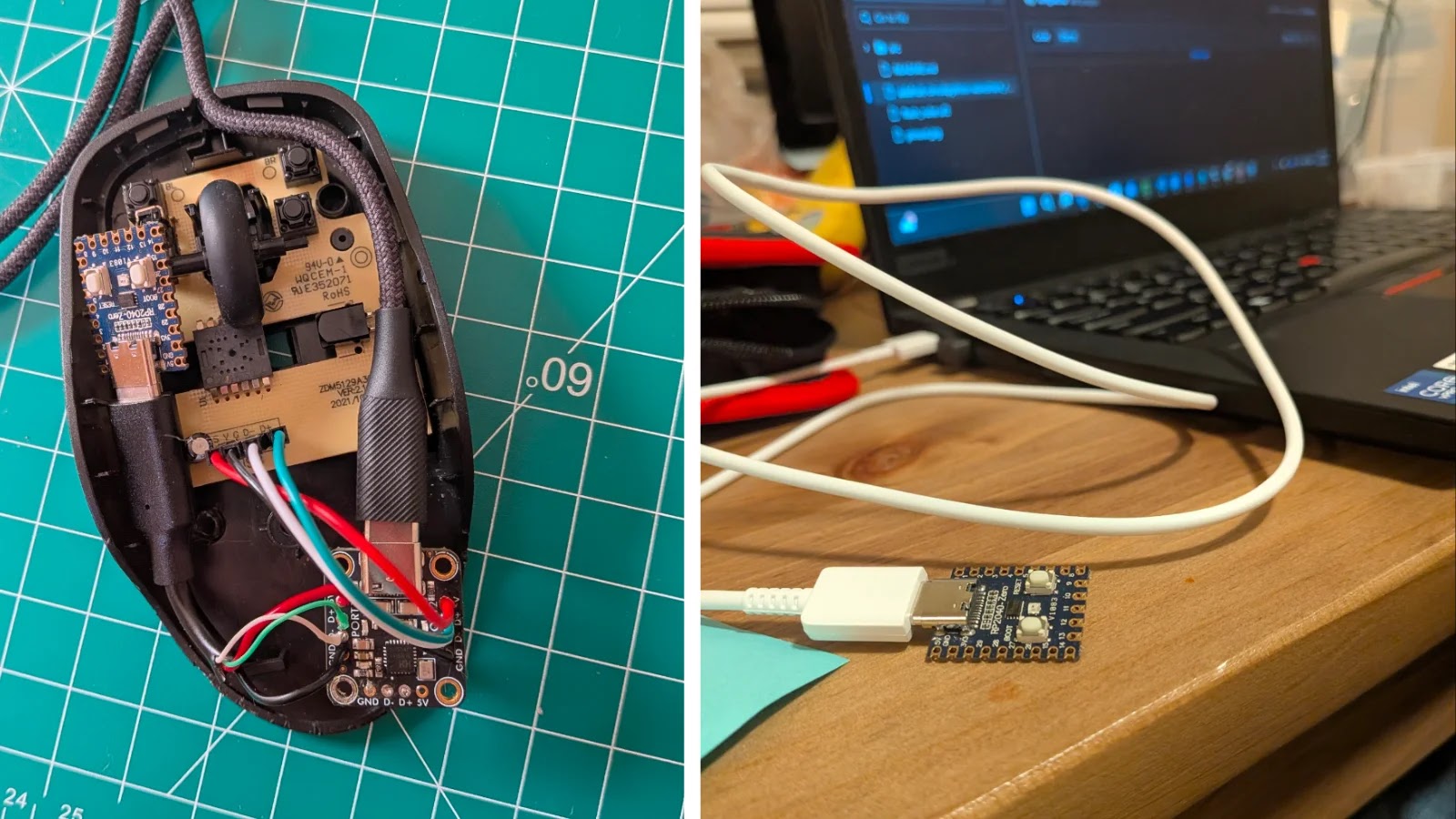
Imagine plugging in a seemingly innocuous computer mouse, only for it to autonomously execute malicious commands on your system, deliver reverse shells, or worse. This [...]