A critical security update for Google Chrome is sounding the alarm across the digital landscape, demanding immediate attention from users and IT professionals alike. [...]
VLANs for Network Segmentation and Data Security Best Practices for VLAN Segmentation In today’s dynamic network landscape, ensuring robust data security and efficient network management [...]
How to Detect MAC Flooding Attack: Understanding the Network of MAC Flood Attack In the realm of network security, understanding the intricacies of various attacks [...]
Microsoft is making a significant move to bolster the security of Windows authentication. The tech giant has announced an accelerated phased roadmap to reduce, restrict, [...]
In the evolving landscape of cyber threats, a new sophisticated phishing campaign has emerged, specifically targeting macOS users. This campaign leverages meticulously crafted fake [...]
Unpacking the Latest PDFly Variant: A Deep Dive into Custom PyInstaller Obfuscation The cybersecurity landscape is a relentless battleground, and threat actors are continuously [...]
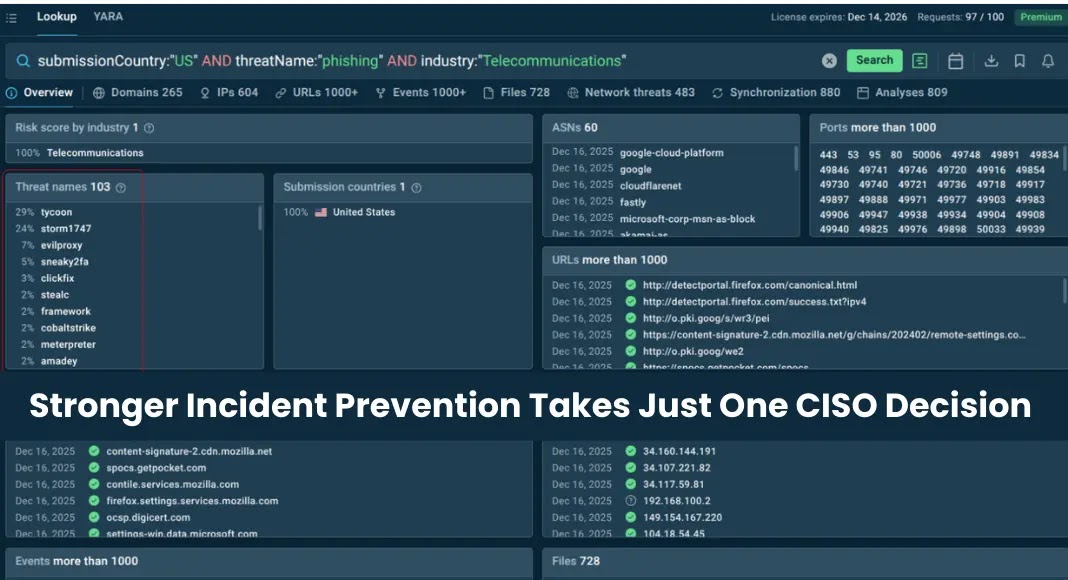
In the complex theater of cybersecurity, a persistent and often misleading narrative suggests that when the digital battleground gets noisy, the immediate solution is [...]
A disturbing trend has emerged in the cybersecurity landscape: threat actors are actively leveraging a critical remote code execution (RCE) vulnerability within React Native’s Metro [...]
The ubiquity of PDF documents in professional and personal workflows makes the tools we use to interact with them critical components of our digital security [...]
Mac Under Threat: Infostealers Leverage Python and Trusted Platforms The digital threat landscape is in constant flux, and a concerning trend has emerged: infostealer [...]