Unmasking SURXRAT: A New Android Threat Landscape The mobile threat landscape is undergoing a significant transformation. We’re observing a clear shift towards highly professionalized [...]
The digital landscape is a constant battleground, where cybercriminals relentlessly evolve their tactics to exploit the trust users place in legitimate brands. A particularly sophisticated [...]
The landscape of cybersecurity is a perpetual cat-and-mouse game, and a recent disclosure has unveiled a concerning new tactic that threat actors could exploit. Researchers [...]
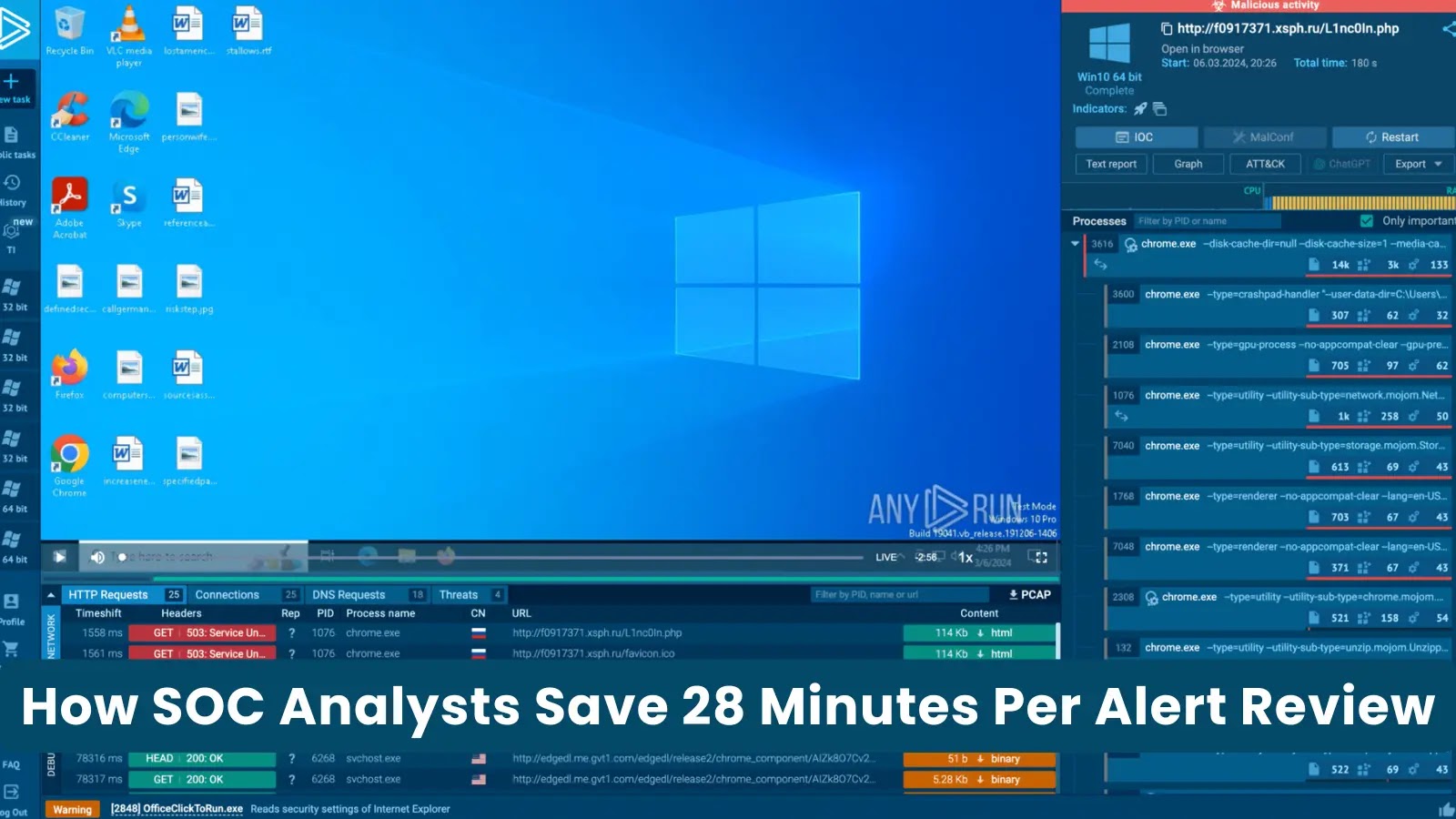
In the high-stakes world of cybersecurity, time is a critical differentiator between proactive defense and reactive damage control. For Security Operations Center (SOC) analysts, the [...]
Hacker Jailbreaks Claude AI: Unprecedented AI Exploitation for Government Data Theft The landscape of cyber warfare just shifted dramatically. A recent report has unveiled [...]
Navigating the Evolving Threat Landscape: OAuth Attacks and Entra ID Compromises In the complex ecosystem of cloud security, threat actors consistently adapt their techniques to [...]
Urgent Alert: Cisco SD-WAN 0-Day Vulnerability Actively Exploited Since 2023 for Root Access A critical zero-day vulnerability in Cisco Catalyst SD-WAN products has been [...]
The cybersecurity landscape just became a little more perilous for organizations leveraging Soliton Systems K.K.’s FileZen. U.S. authorities have confirmed that threat actors are actively [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Information Disclosure Vulnerability in Microsoft Teams Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: HIGH Software Affected Microsoft [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Privilege Escalation Vulnerability in Microsoft Windows Admin Center Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: HIGH Software [...]