Organizations worldwide rely on VMware Aria Operations to manage their cloud infrastructure efficiently. However, a recent disclosure from Broadcom has cast a critical spotlight [...]
In the relentless landscape of cyber threats, attackers continuously hone their deceptive tactics. A prime example of this evolution is the recently identified “ClickFix” infostealer [...]
Musk Accuses Anthropic of Massive Data Theft: A Cybersecurity Wake-Up Call The artificial intelligence landscape, already fraught with ethical and legal complexities, has been [...]
The digital landscape is a constant battleground, and alarming news has emerged that underscores this reality. The notorious cybercriminal syndicate ShinyHunters has reportedly claimed responsibility [...]
The landscape of cyber threats is undergoing a dramatic shift. What was once the exclusive domain of human ingenuity, complex attack methodologies are now being [...]
OpenClaw’s Latest Leap: 2026.2.23 — Enhanced Security Meets Cutting-Edge AI In the dynamic landscape of personal AI assistants, security and innovation often walk a tightrope. [...]
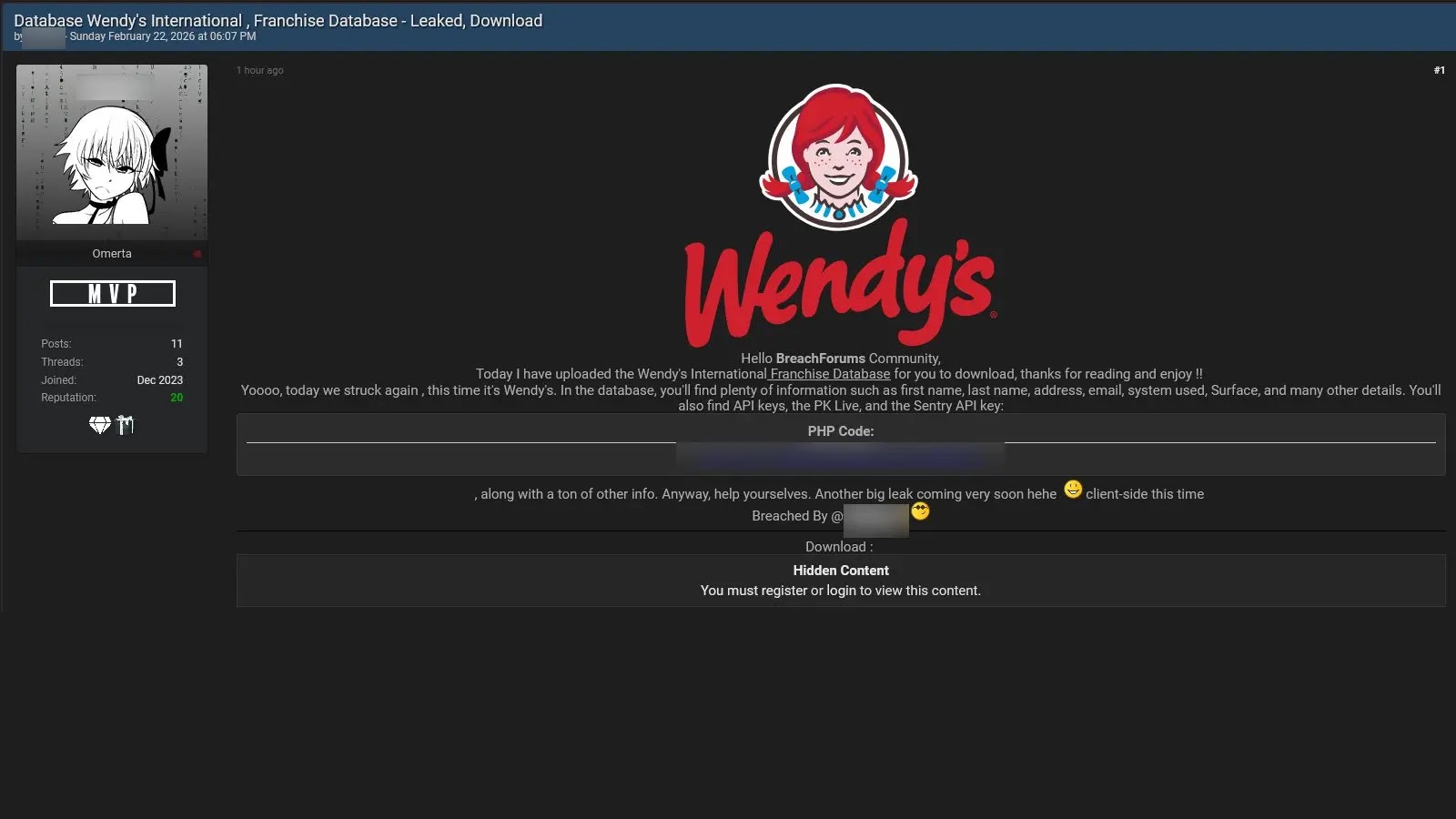
A disturbing claim has surfaced in the cybersecurity landscape, sending ripples through the financial and operational structures of a global fast-food giant. On February [...]
Urgent Alert: PoC Exploit Released for Grandstream GXP1600 VoIP Phones RCE Vulnerability The cybersecurity landscape has once again shifted with the emergence of a [...]
In the intricate landscape of telecommunications infrastructure, even seemingly minor vulnerabilities can have significant repercussions. A recent security bulletin from Hewlett Packard Enterprise (HPE) [...]
jsPDF Vulnerability Exposes Millions to Object Injection Attacks: A Deep Dive The digital landscape consistently presents new challenges for developers, and a recent discovery [...]