The mobile threat landscape just got a significant upgrade, and it’s not good news for Android users. A formidable new banking Trojan, dubbed Perseus, has [...]
The modern workforce, increasingly distributed across various locations and devices, demands seamless and secure communication. Microsoft, a titan in enterprise solutions, has once again stepped [...]
Network defenders and security administrators, take note: A critical zero-day vulnerability in Cisco Secure Firewall Management Center (FMC) is currently under active exploitation by ransomware [...]
Urgent Warning: Critical Jenkins Vulnerabilities Open CI/CD Gates to RCE Attacks The continuous integration and continuous deployment (CI/CD) pipeline is the lifeblood of modern software [...]
The landscape of cyber threats is in constant flux, and one of the most insidious dangers organizations face today is ransomware. While security teams diligently [...]
How to secure switch access with SSH and configure remote access with SSH Secure Shell (SSH) is a protocol that enables secure, encrypted connections between [...]
The digital landscape of software development and release management relies heavily on robust, integrated platforms. Among these, Atlassian Bamboo Data Center stands out for its [...]
In a stark reminder of the persistent threats facing sensitive personal data, Navia, a prominent U.S. consumer-focused benefits administrator, has disclosed a significant data breach. [...]
Unmasking Speagle: How a New Infostealer Hijacks Cobra DocGuard The digital landscape is a constant battlefield, and new threats emerge with alarming frequency. Recently, a [...]
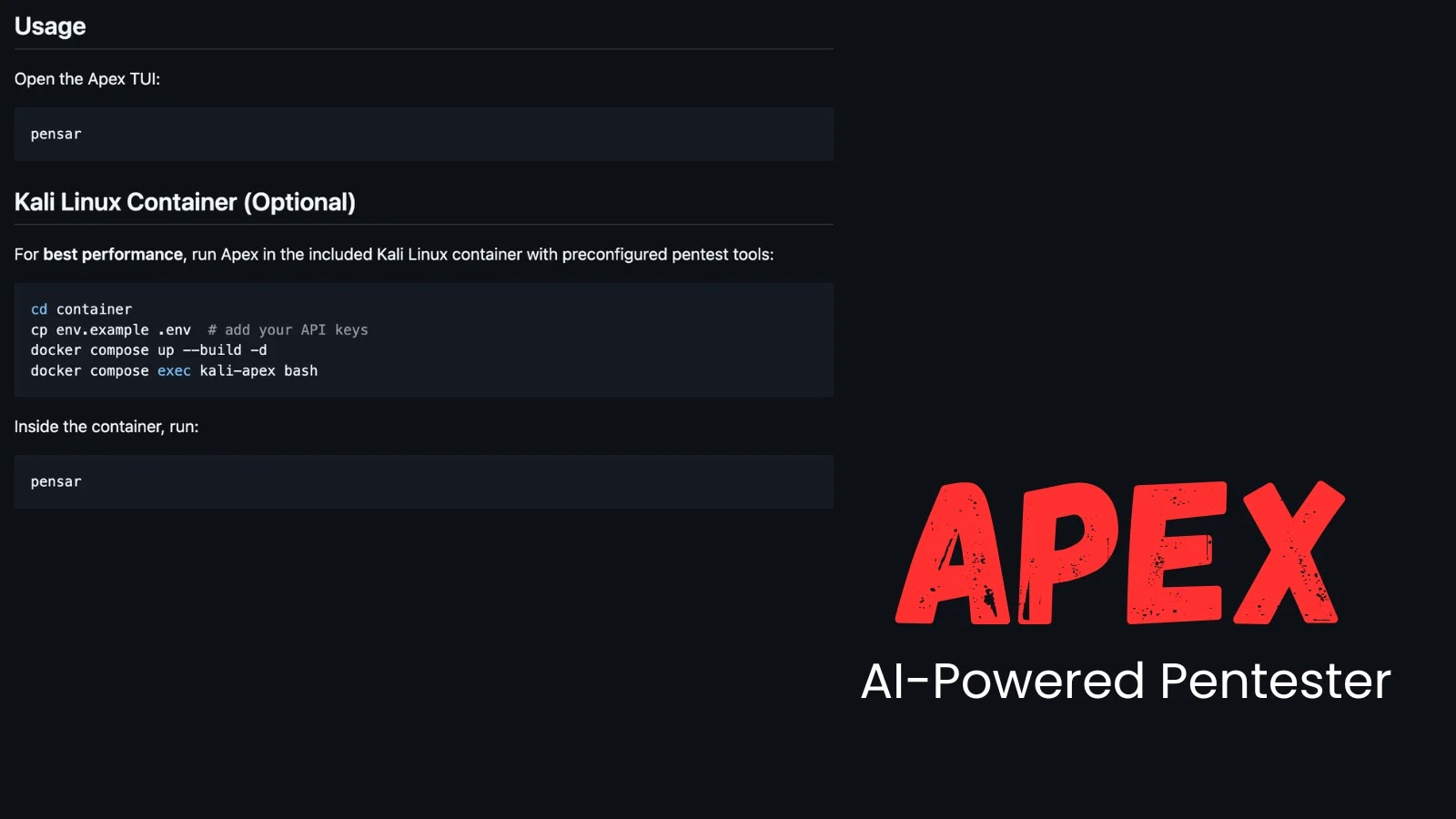
In the relentless pursuit of robust software security, traditional penetration testing often struggles to keep pace with rapid development cycles. Security teams face immense pressure [...]