CISA Warns of Critical SimpleHelp Vulnerabilities Actively Exploited in Attacks The digital landscape is a constant battlefield, and organizations rely heavily on remote access tools [...]
A significant architectural flaw, dubbed PhantomRPC, has been uncovered within the Windows Remote Procedure Call (RPC) mechanism. This critical vulnerability allows for local privilege escalation, [...]
A Critical Blow: Litecoin Zero-Day Vulnerability Rocks Mining Pools The cryptocurrency landscape, while built on principles of decentralization and security, is not immune to sophisticated [...]
A Deeper Dive: GlassWorm’s Evolving Threat on Open VSX The digital supply chain is a prime target for threat actors, and the Open VSX marketplace [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Defending Against Frontier AI Driven Cyber Risks Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: High Description Recent [...]
Nessus Agent Vulnerability on Windows: A SYSTEM-Level Threat to Enterprise Security Enterprise security teams are facing a heightened alert following the disclosure of a critical [...]
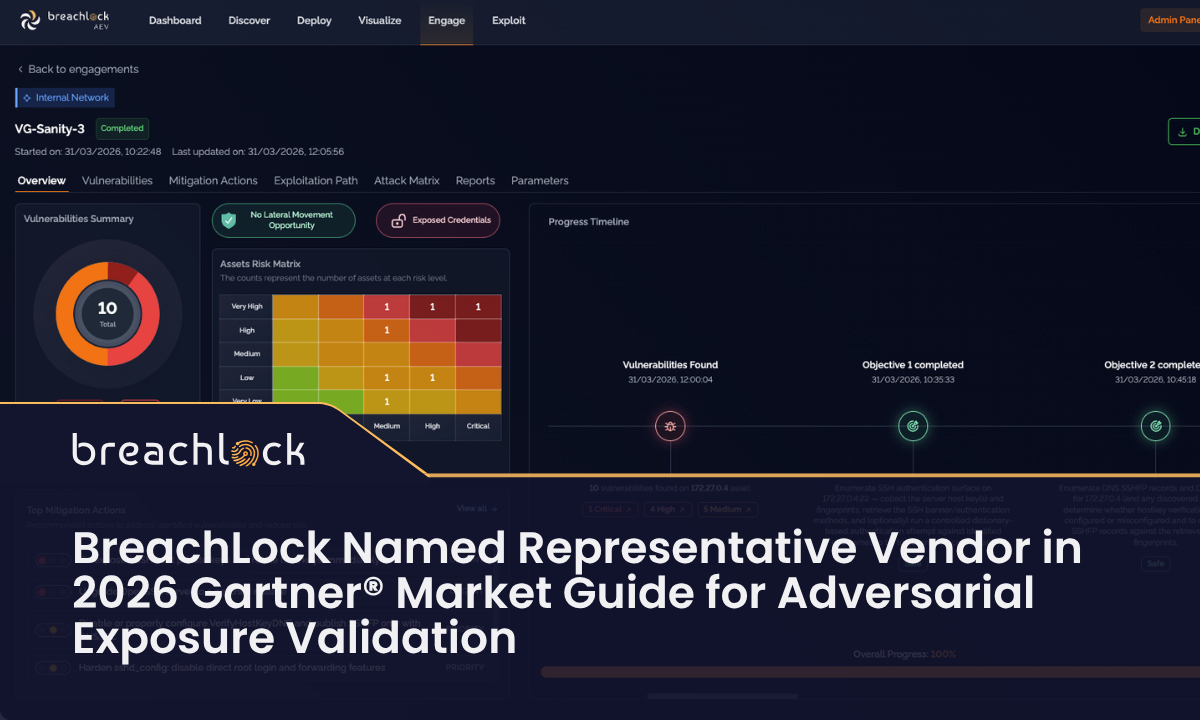
In the dynamic landscape of cybersecurity, accurately assessing an organization’s true security posture is paramount. Traditional vulnerability scanning and penetration testing, while valuable, often provide [...]
The AI Identity Crisis: Why 92% of Enterprises Lack Visibility into Ungoverned AI Workforces The rise of artificial intelligence (AI) in enterprise operations is undisputed, [...]
The Deceptive Lure: Void Dokkaebi’s Fake Job Interviews and Malware Distribution In a cunning new campaign, the North Korea-linked hacking group known as Void Dokkaebi, [...]
Few online experiences are as ubiquitous, or sometimes as frustrating, as encountering a CAPTCHA. These simple “proof-of-human” tests, requiring us to identify traffic lights or [...]