—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Multiple Vulnerabilities in Gitlab Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: HIGH Software Affected Gitlab versions prior [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Multiple Vulnerabilities in SAP Products Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: High Software Affected SAP S/4HANA [...]
Elastic, a prominent name in search, observability, and security solutions, has recently released crucial security updates that demand immediate attention from IT professionals and security [...]
Unmasking CVE-2026-22718: A Critical Command Injection Flaw in the Spring CLI VSCode Extension The landscape of software development continuously presents new security challenges. Even foundational [...]
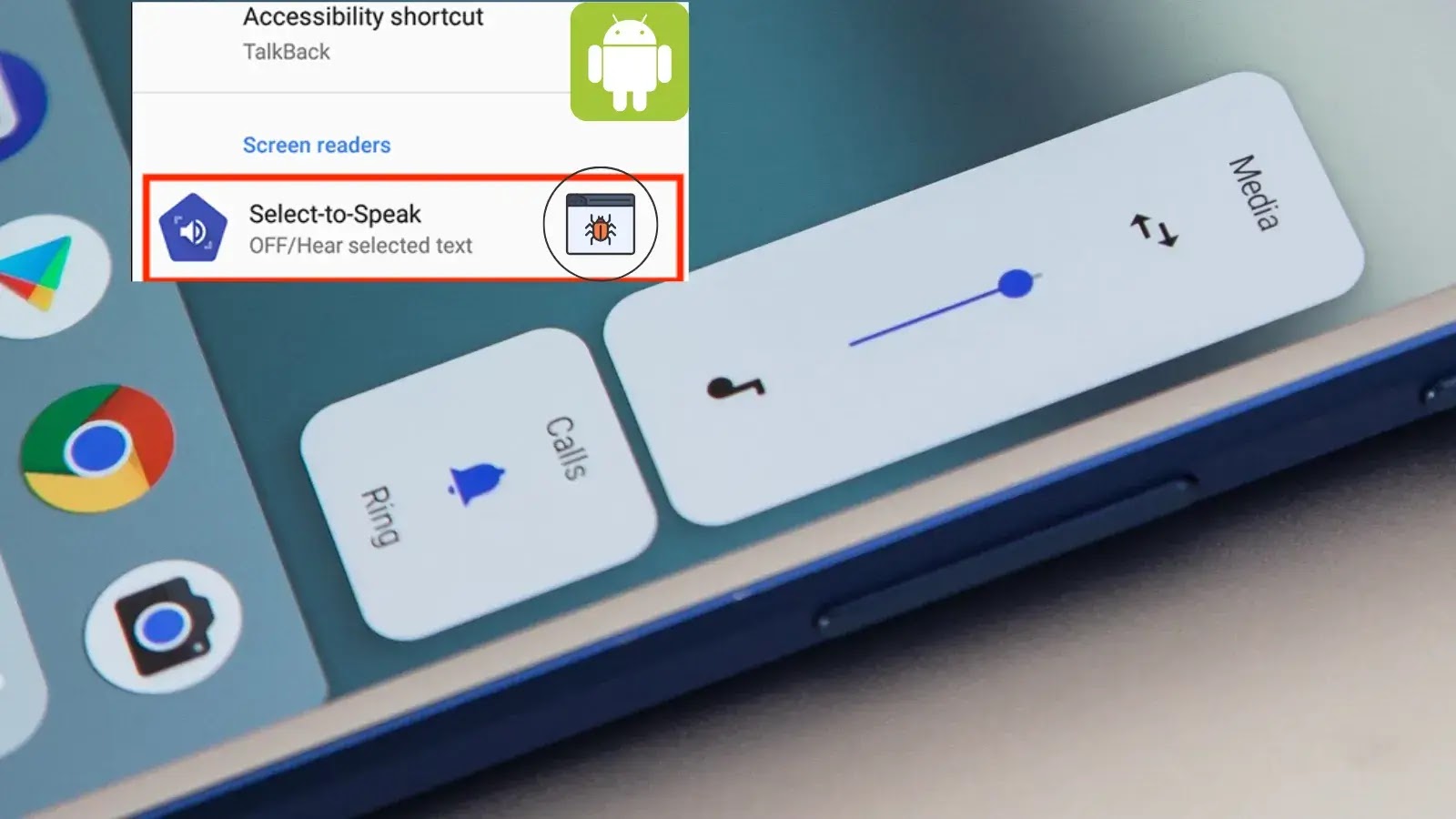
A recently identified critical bug affects Android devices, specifically impacting the functionality of volume buttons when the “Select to Speak” accessibility feature is enabled. This [...]
The digital storefronts we rely on for everything from groceries to gadgets face a persistent and evolving threat: web skimming. A new variant of this [...]
The eCommerce landscape is a digital goldmine, but for every legitimate transaction, there’s a cyber threat lurking. With the sector’s explosive growth, the necessity for [...]
Navigating the Evolving Landscape of Financial Data Security in 2026 The financial services sector operates at the nexus of trust and vulnerability. Handling vast [...]
The insurance industry, by its very nature, is a custodian of some of the most sensitive personal and financial data imaginable. From health records to [...]
Navigating the Cloud Security Landscape for Healthcare in 2026 The healthcare sector faces a unique and escalating challenge: safeguarding incredibly sensitive patient data within increasingly [...]