Unmasking DesckVB RAT: A Sophisticated Takedown of an Evolving Threat The digital landscape is a constant battlefield, where new and more complex threats emerge [...]
A disturbing trend has emerged in the cybersecurity landscape: advanced persistent threat (APT) actors are increasingly camouflaging sophisticated malware within seemingly innocuous application installers. [...]
A Disturbing Compromise: Notepad++ Update Infrastructure Abused in Targeted Supply Chain Attack The ubiquity of software updates, designed to enhance features and patch vulnerabilities, [...]
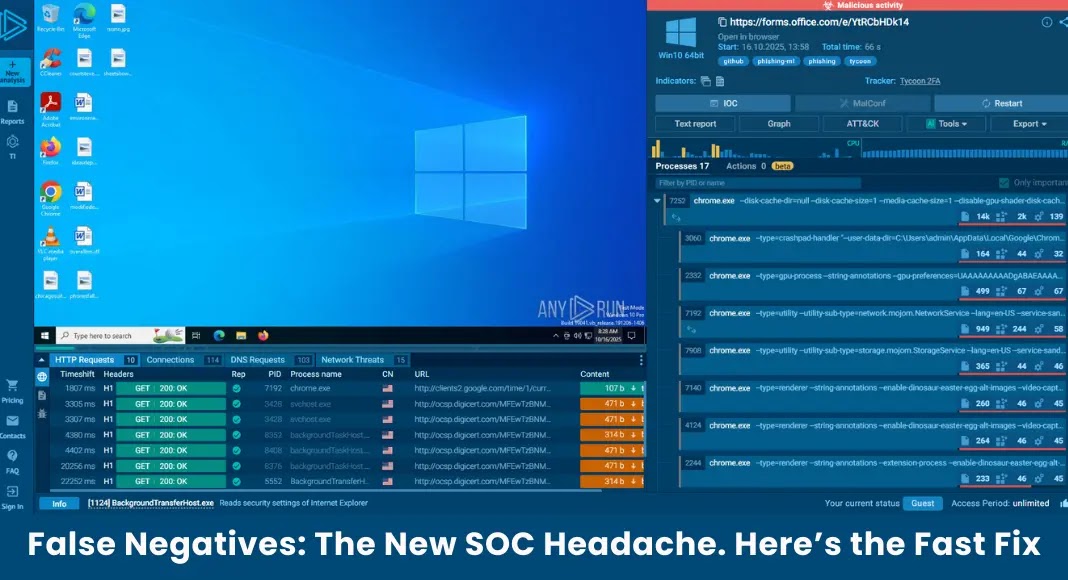
The Silent Killer: How False Negatives Are Costing Your SOC Dearly The cybersecurity landscape is a relentless battlefield, and while much attention focuses on [...]
The silent infiltrator. It’s a phrase that haunts the cybersecurity landscape, especially when discussing sophisticated malware loaders. Recently, a new and particularly cunning custom loader, [...]
Interlock Ransomware Actors New Tool Exploiting Gaming Anti-Cheat Driver 0-Day to Disable EDR and AV
In a concerning development for enterprise security, the Interlock ransomware group has unveiled a new, potent tool capable of disabling endpoint detection and response [...]
The digital threat landscape is perpetually shifting, and among the most insidious and persistent dangers are botnets. These networks of compromised devices, often operating undetected, [...]
Unmasking ClickFix: A Deep Dive into KongTuke’s DNS TXT-Based PowerShell Execution The cybersecurity landscape has darkened with the sophisticated evolution of the KongTuke campaign. [...]
Unmasking the Amaranth-Dragon: Exploiting WinRAR to Compromise Southeast Asian Governments In the high-stakes arena of cyber espionage, a sophisticated actor known as Amaranth-Dragon has [...]
A chilling alert has echoed through the cybersecurity community: the U.S. Cybersecurity and Infrastructure Security Agency (CISA) has confirmed active exploitation of a critical VMware [...]