A severe security flaw lurking within HPE OneView Software has sent a clear warning signal across the cybersecurity landscape. This critical vulnerability, capable of allowing [...]
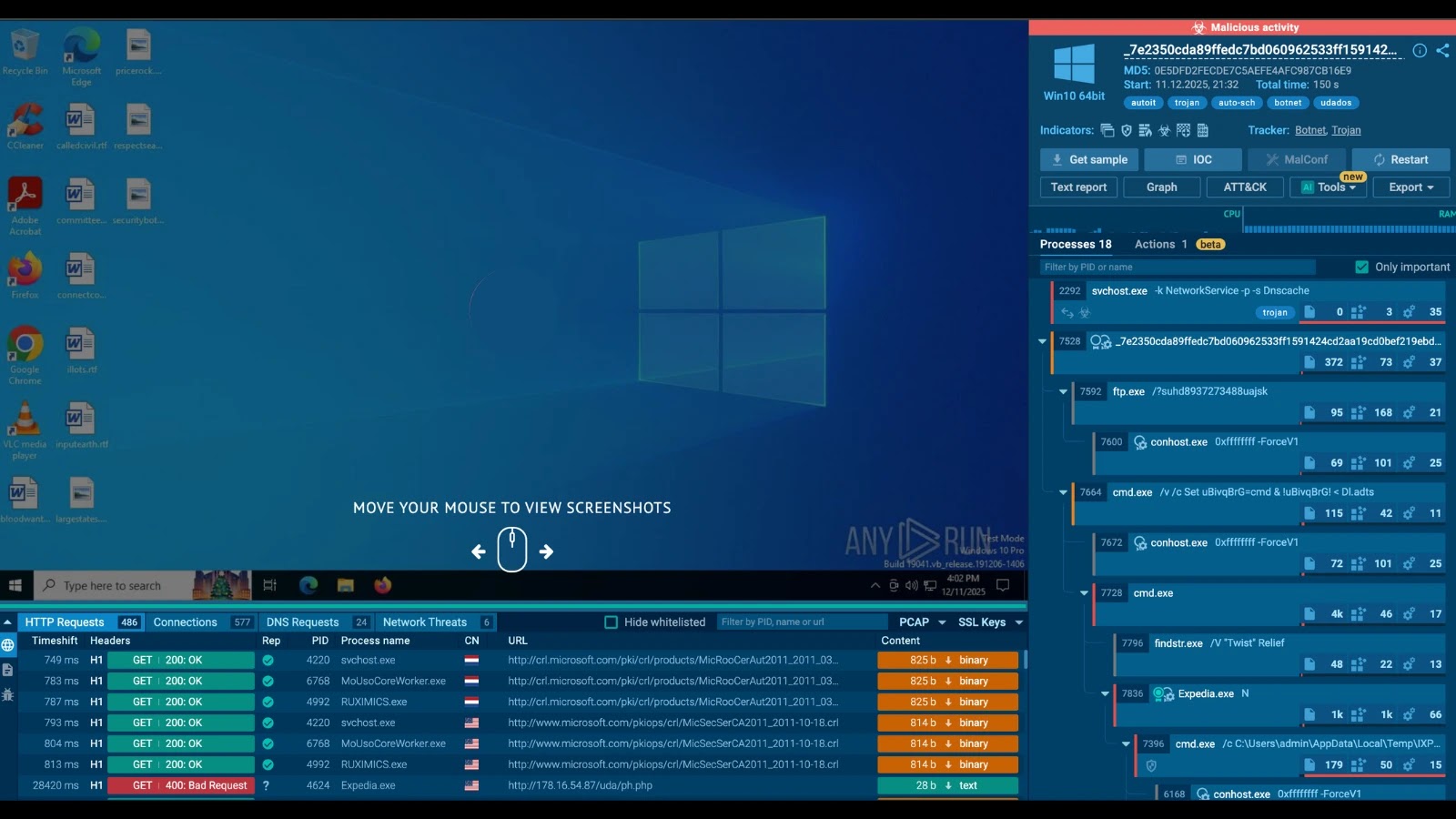
Unmasking Udados: A New Botnet’s Assault on the Tech Sector The digital landscape just got a new, formidable adversary. A newly identified botnet malware [...]
OpenAI GPT-5.2-Codex: Revolutionizing Agentic Coding and Vulnerability Detection The pace of software development and the escalating complexity of cybersecurity threats demand increasingly sophisticated tools. In [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Remote Code Execution Vulnerability in Cisco AsyncOS Software Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: CRITICAL Systems [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Remote Code Execution Vulnerability in Cisco AsyncOS Software Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: CRITICAL Systems [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Security Restriction Bypass Vulnerability in Synology DiskStation Manager Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: HIGH Software [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Multiple Vulnerabilities in Apache HTTP Server Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: MEDIUM Software Affected Apache [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Authentication Bypass Vulnerability in Fortinet Products Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: CRITICAL Software Affected FortiOS [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Multiple vulnerabilities in Microsoft Edge (Chromium-based) Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: HIGH Software Affected Microsoft [...]
The React2Shell Threat: Unpacking CVE-2025-55182 and Escalating Attacks A new and aggressive threat, dubbed React2Shell (officially CVE-2025-55182), has emerged, targeting widely deployed React Server Components [...]