A critical security flaw has been identified in Plesk for Linux, empowering malicious actors to achieve root-level access on affected server systems. This vulnerability, tracked [...]
New ARTEMIS AI Agent Outperformed 9 out of 10 Human Penetration Testers in Detecting Vulnerabilities
The landscape of cybersecurity is under constant pressure from increasingly sophisticated threats. Organizations invest heavily in robust security measures, often relying on the keen [...]
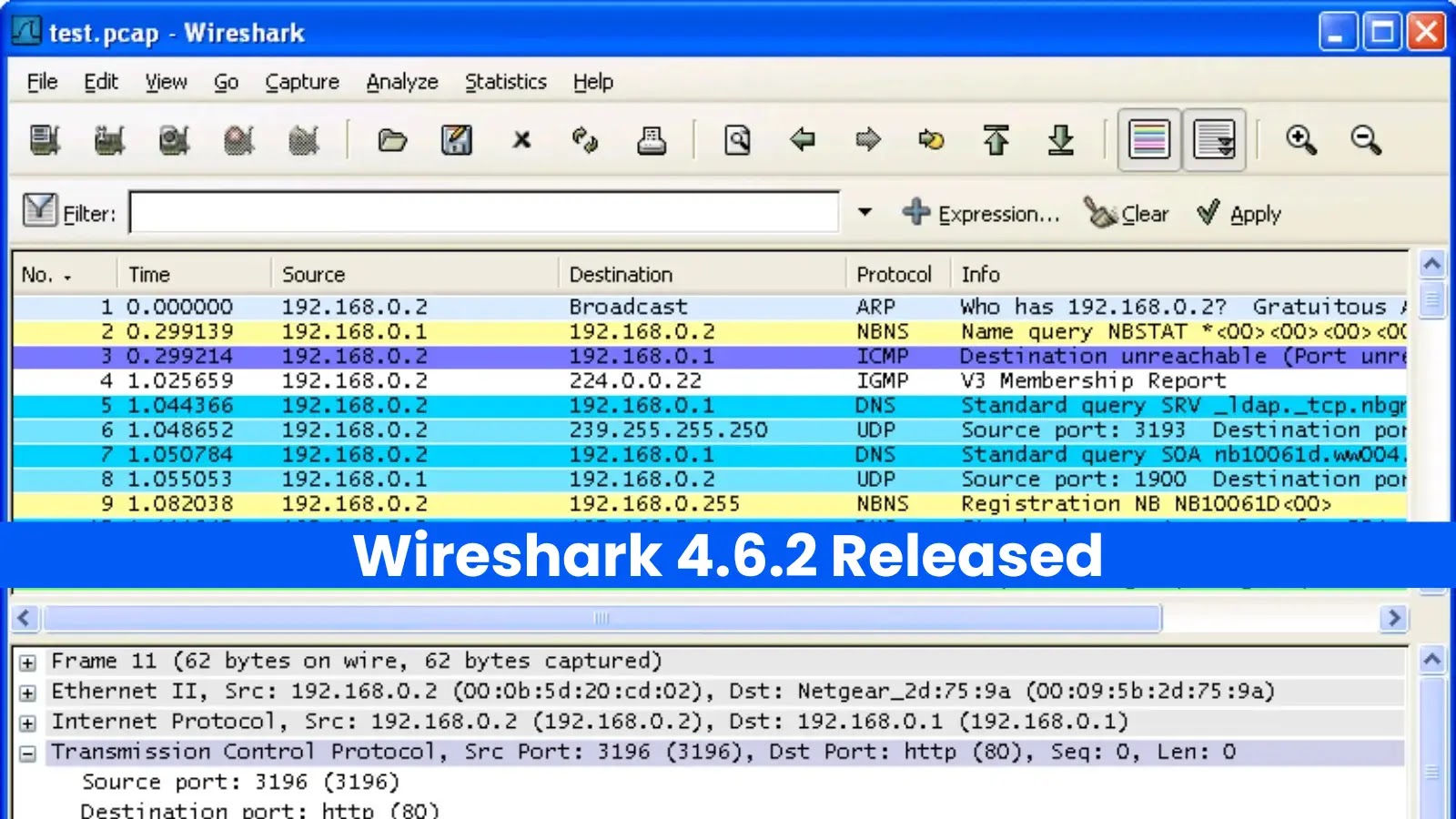
Wireshark 4.6.2: Essential Update for Network Forensics and Troubleshooting In the intricate world of network analysis, stability and accuracy are not just features; they [...]
Microsoft Update Hinders WSL VPS Access: A Deep Dive into KB5067036 Disruptions The intricate dance between operating systems, virtualization layers, and network connectivity is often [...]
Critical pgAdmin Vulnerability Exposes PostgreSQL Servers to Remote Shell Command Execution A significant security flaw has been recently uncovered in pgAdmin 4, the widely used [...]
NVIDIA Merlin Vulnerabilities Expose Systems to Code Execution and DoS Attacks The landscape of enterprise AI and machine learning is constantly evolving, with frameworks like [...]
Unmasking the Apache StreamPark Vulnerability: A Gateway to Sensitive Data Exposure The digital infrastructure underpinning modern data processing often relies on powerful, open-source frameworks. [...]
Unveiling MioLab MacOS: A New Threat to Apple Users A new, sophisticated information stealer named “MioLab MacOS” has surfaced on underground cybercrime forums, posing a [...]
The digital landscape is a constant battleground, and for Android users, a new and particularly insidious threat has emerged: Frogblight. This sophisticated banking Trojan, first [...]
The digital perimeter of even the most established global enterprises is constantly under siege. For Jaguar Land Rover (JLR), the renowned British luxury automaker, that [...]