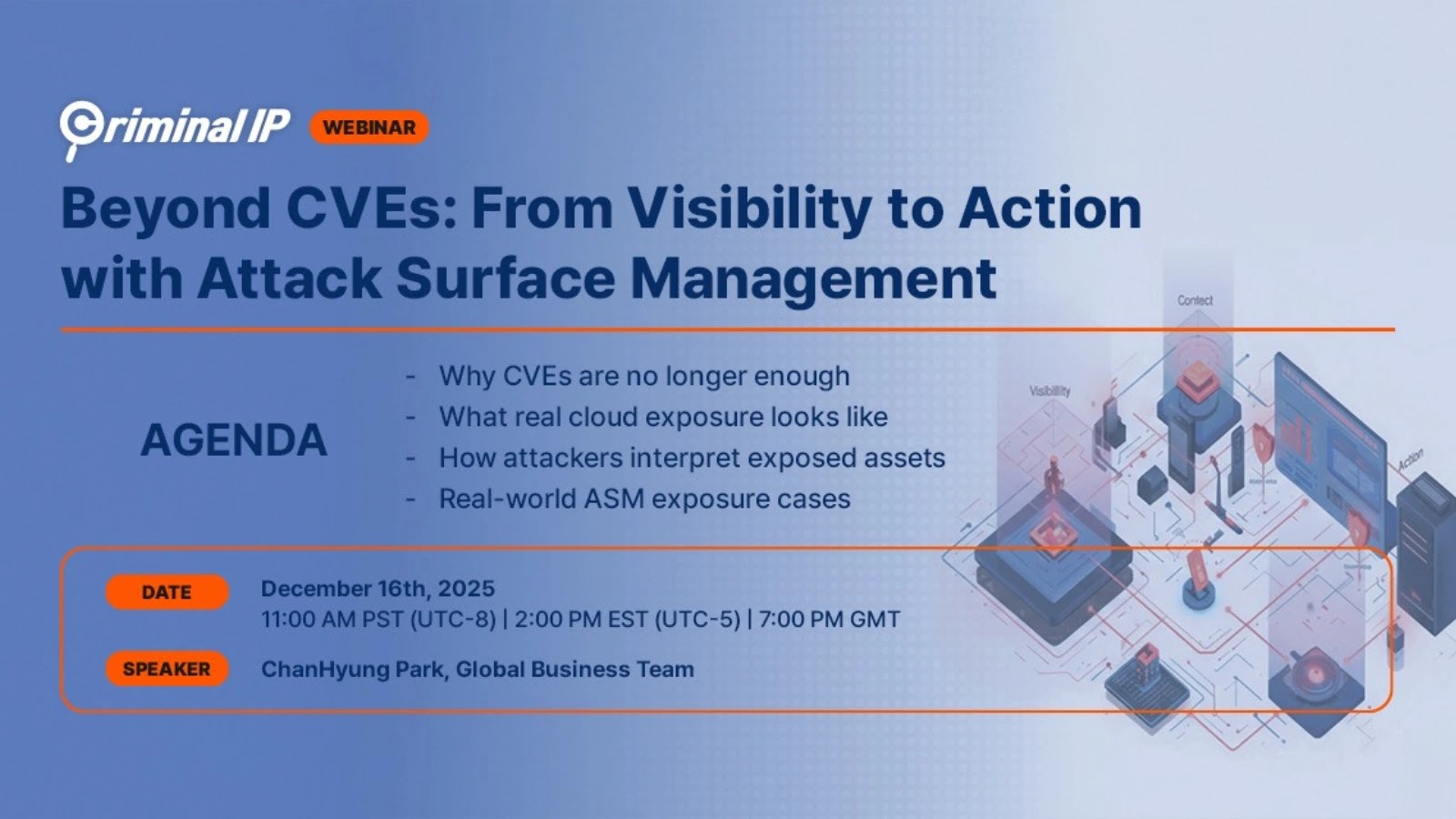
In the rapidly changing landscape of cybersecurity, relying solely on traditional vulnerability management strategies can leave organizations exposed. While Common Vulnerabilities and Exposures (CVEs) remain [...]
The entertainment landscape just experienced an earthquake. Netflix, long a dominant force in streaming, has announced a monumental acquisition that reshapes the industry: a staggering [...]
Avast Antivirus Sandbox Vulnerabilities Expose Users to Privilege Escalation The security landscape demands constant vigilance, especially when it comes to fundamental protection software. Recent [...]
A silent alarm echoes through the digital landscape, impacting millions of web services powered by Next.js. A critical unauthenticated remote code execution (RCE) vulnerability, [...]
The integration of artificial intelligence into development pipelines offers powerful automation capabilities, yet it also introduces novel attack vectors. Recent research has exposed a [...]
Unmasking FvncBot: A New Threat to Android Banking Security The digital landscape is a constant battleground, and a new and particularly insidious adversary has emerged [...]
Urgent Alert: Widespread Attacks Target Palo Alto GlobalProtect VPNs In the evolving landscape of remote work, secure access solutions like Palo Alto Networks’ GlobalProtect VPN [...]
The digital underworld just got a bit more exposed as critical infrastructure linked to the notorious LockBit 5.0 ransomware group has surfaced. This revelation offers [...]
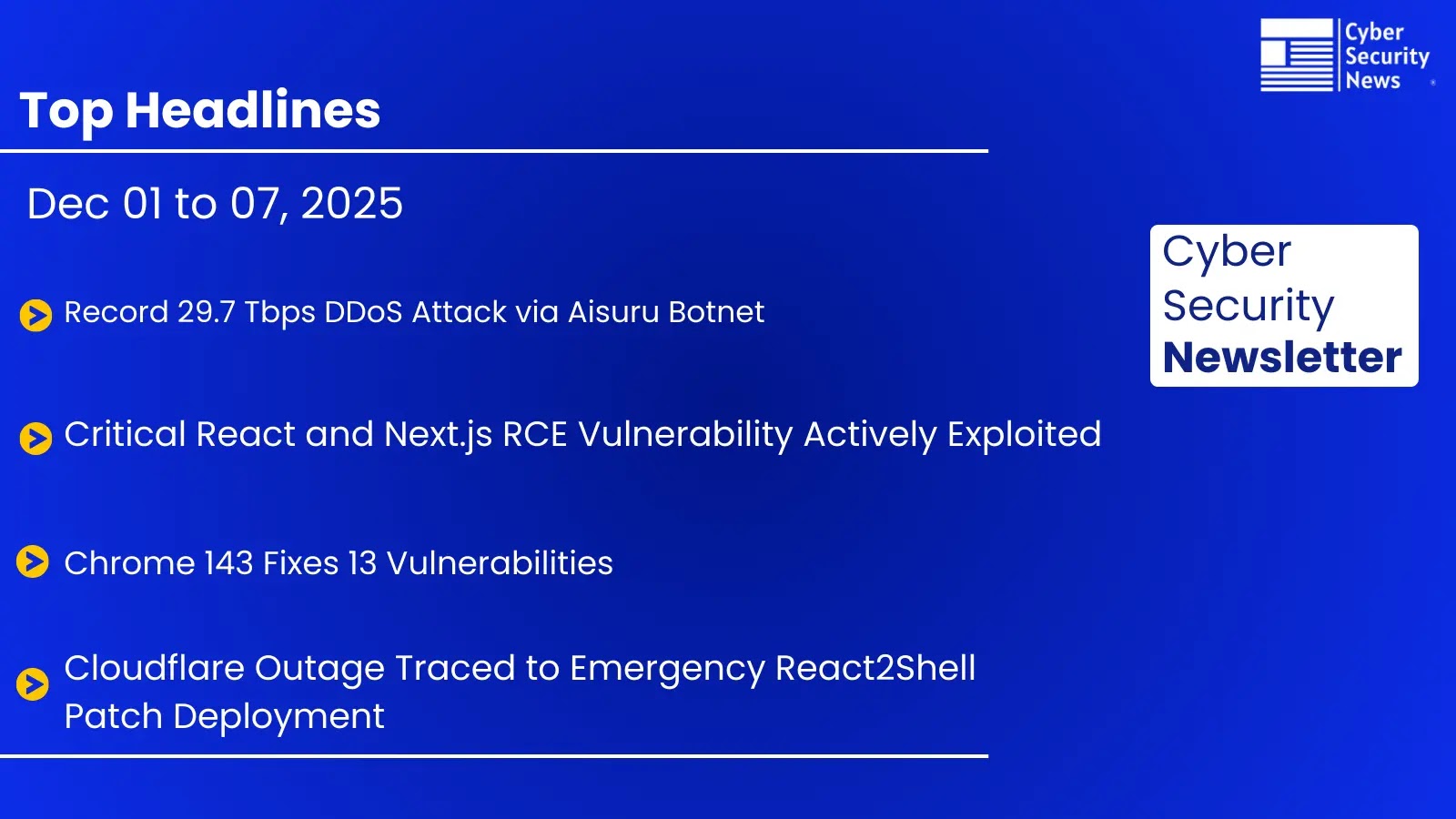
Navigating the Storm: Weekly Cybersecurity Recap Featuring a Record-Breaking DDoS Attack and Critical Chrome Patches The digital landscape consistently presents new challenges, and this past [...]
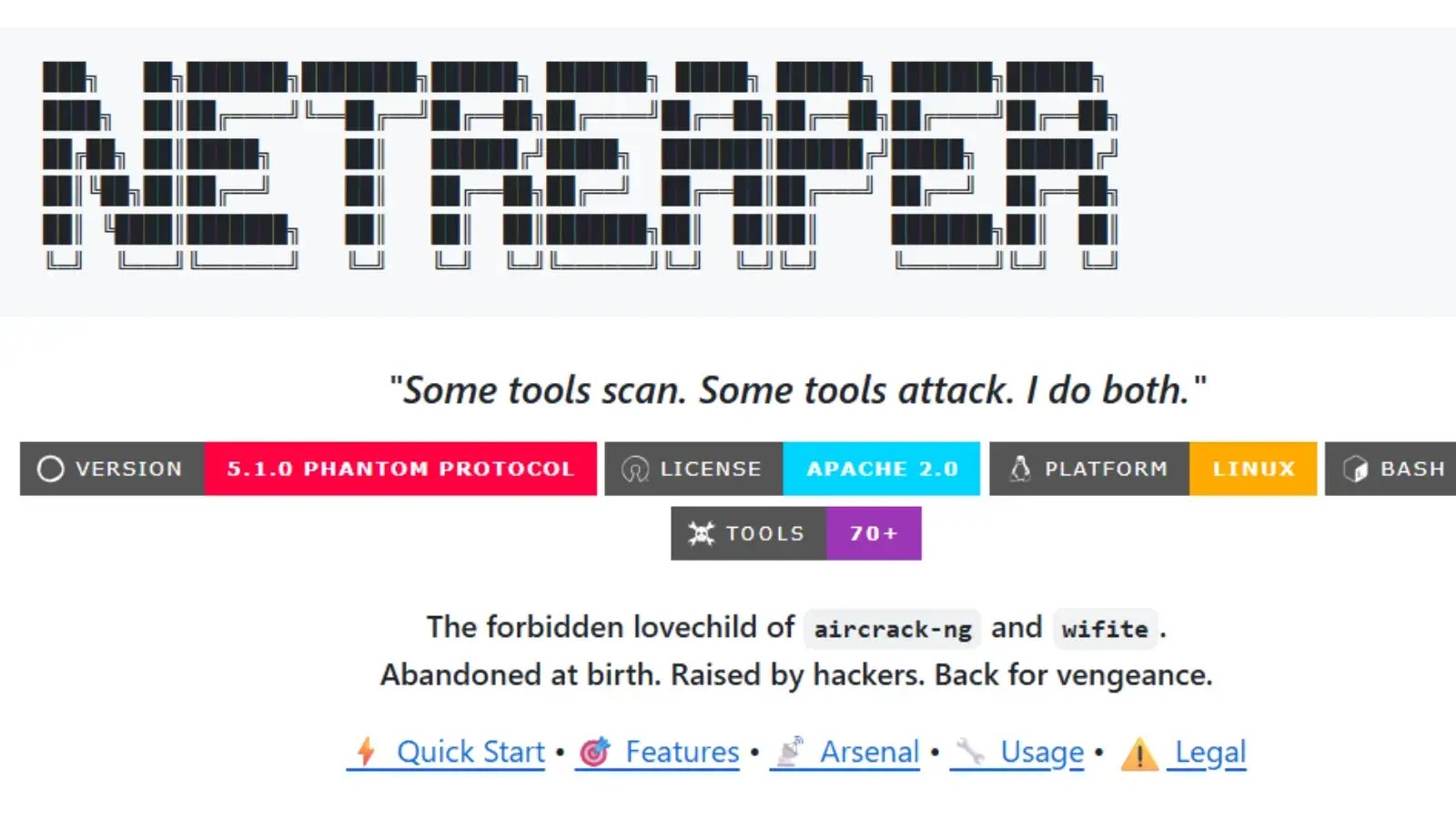
Streamlining Offensive Security: A Deep Dive into the NETREAPER Toolkit Penetration testers constantly face the challenge of managing a diverse array of tools. Juggling multiple [...]