The digital landscape is a constant battleground, with new threats emerging and evolving at a relentless pace. Staying informed about novel attack vectors and [...]
Navigating the Fallout: Cornwell Quality Tools Data Breach Exposes 100,000 Users In an increasingly interconnected digital landscape, the security of sensitive personal information remains [...]
The Double-Edged Sword: When Legitimate Tools Turn Malicious with AdaptixC2 The cybersecurity landscape is constantly evolving, presenting new challenges as threat actors refine their [...]
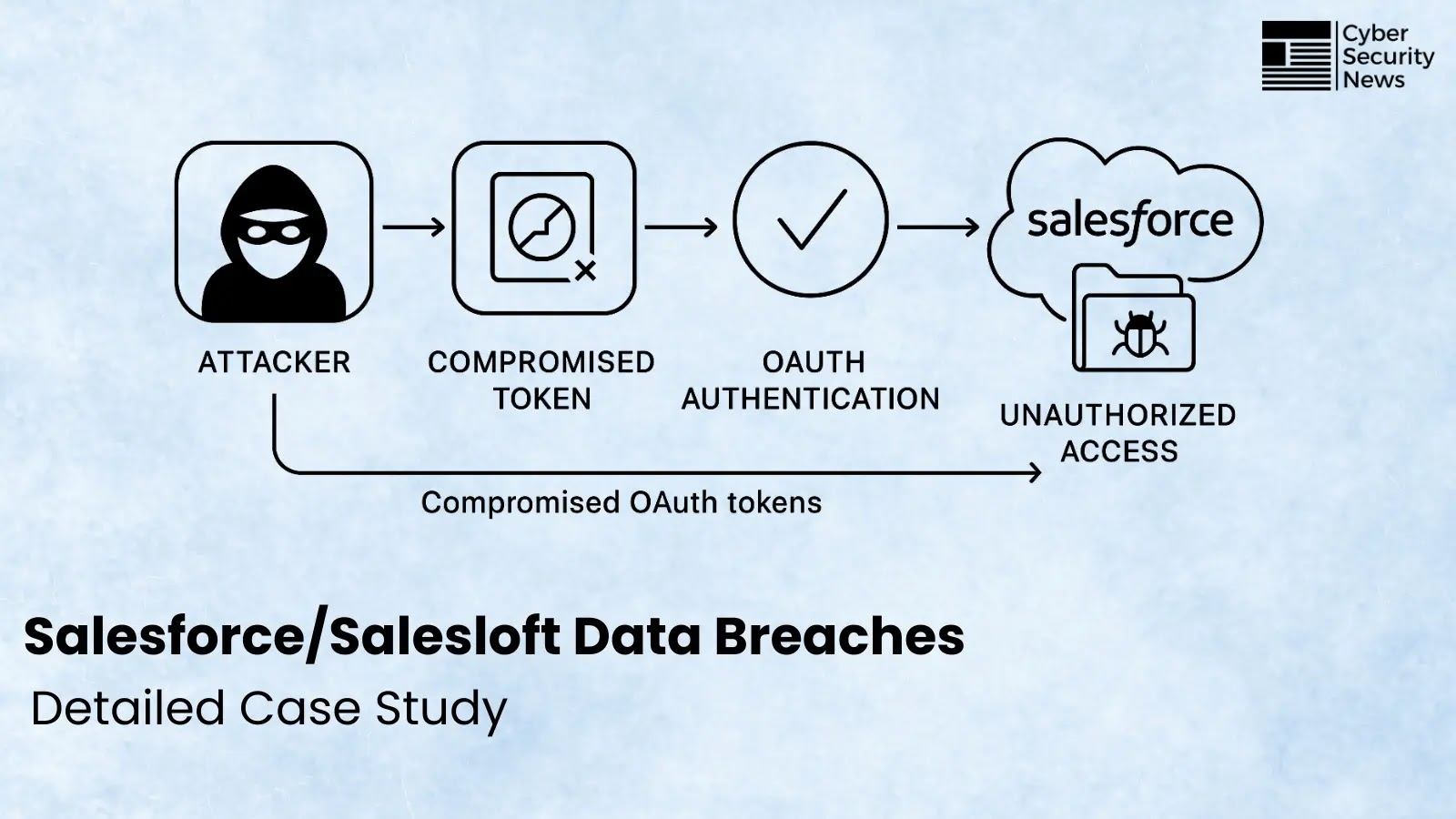
Unpacking the Salesloft/Salesforce Drift Data Breaches: A Supply Chain Security Reckoning The cybersecurity landscape continuously shifts, presenting new challenges and exposing vulnerabilities in even [...]
A new and dangerous player has emerged in the cyber espionage landscape, wielding a sophisticated fileless malware framework dubbed EggStreme. This advanced persistent threat [...]
The digital realm, while connecting us globally, simultaneously presents unprecedented avenues for surveillance and intrusion. A recent unsettling incident involving Kenyan filmmakers and the sophisticated [...]
Unprecedented L7 DDoS Botnet Unleashes Havoc: 5.76 Million Devices Hijacked Distributed Denial of Service (DDoS) attacks are a persistent and evolving threat, capable of [...]
Unveiling VMScape: A Critical New Spectre-BTI Attack Threatening VM Isolation The digital landscape is under constant siege, with sophisticated new threats emerging that challenge [...]
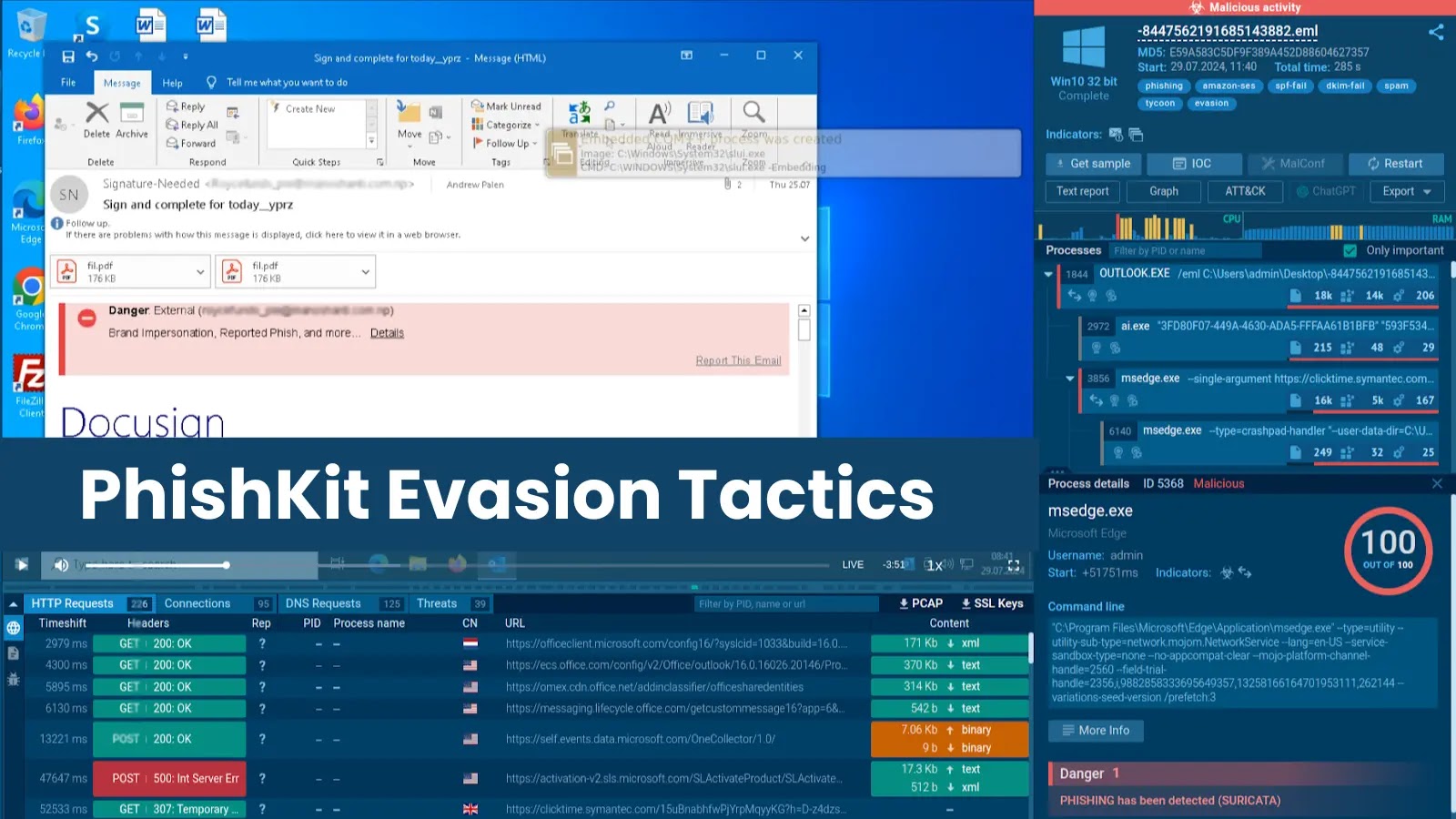
The relentless evolution of cyber threats demands constant vigilance, especially when it comes to sophisticated phishing campaigns. Attackers are not just improving their lures; [...]
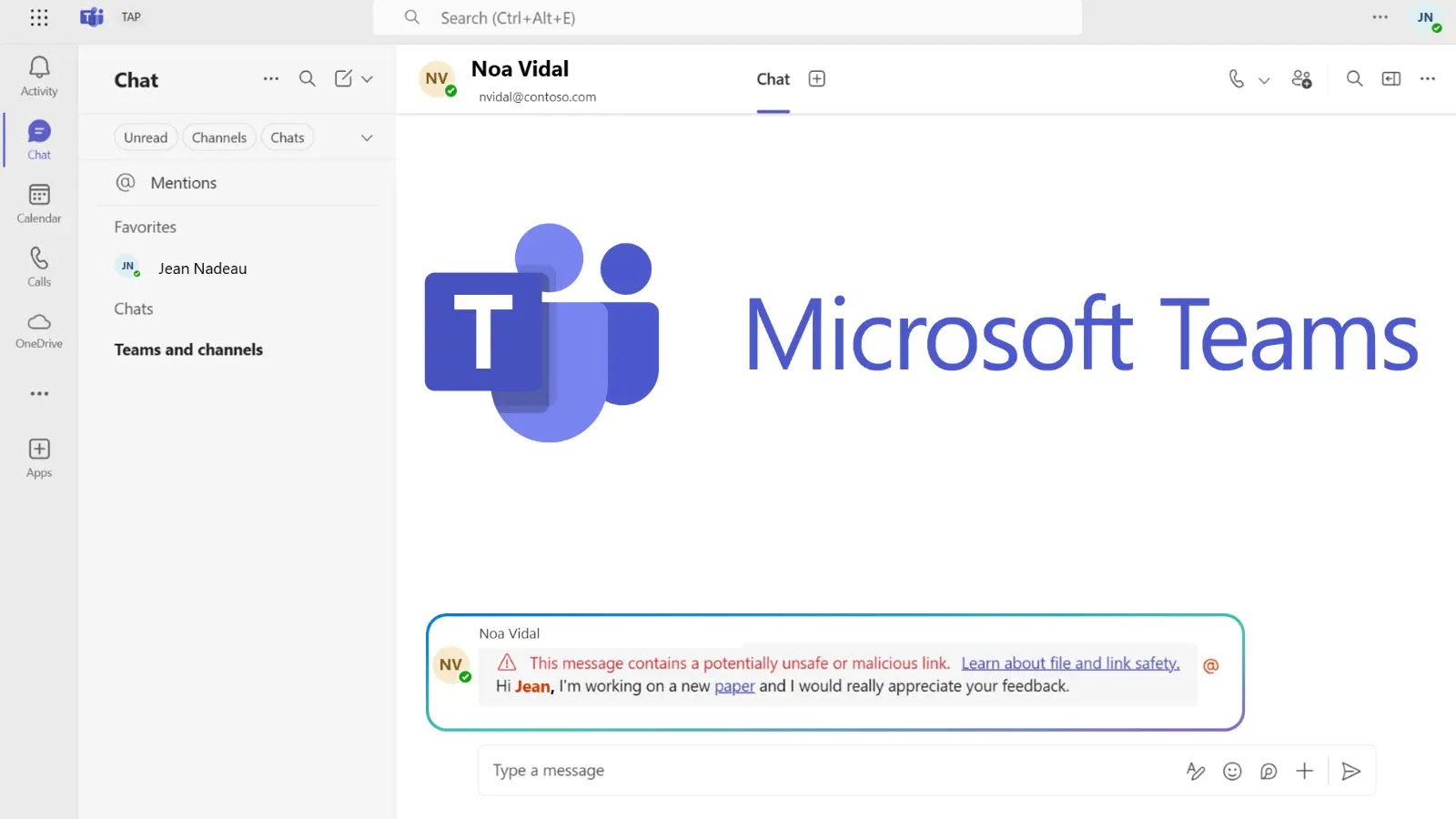
The digital workspace, while a nexus of productivity and collaboration, has become an increasingly attractive target for threat actors. As organizations worldwide lean heavily [...]