Organizations leveraging SonicWall products are facing a critical security alert. The Australian Cyber Security Centre (ACSC) has issued an urgent warning regarding a severe [...]
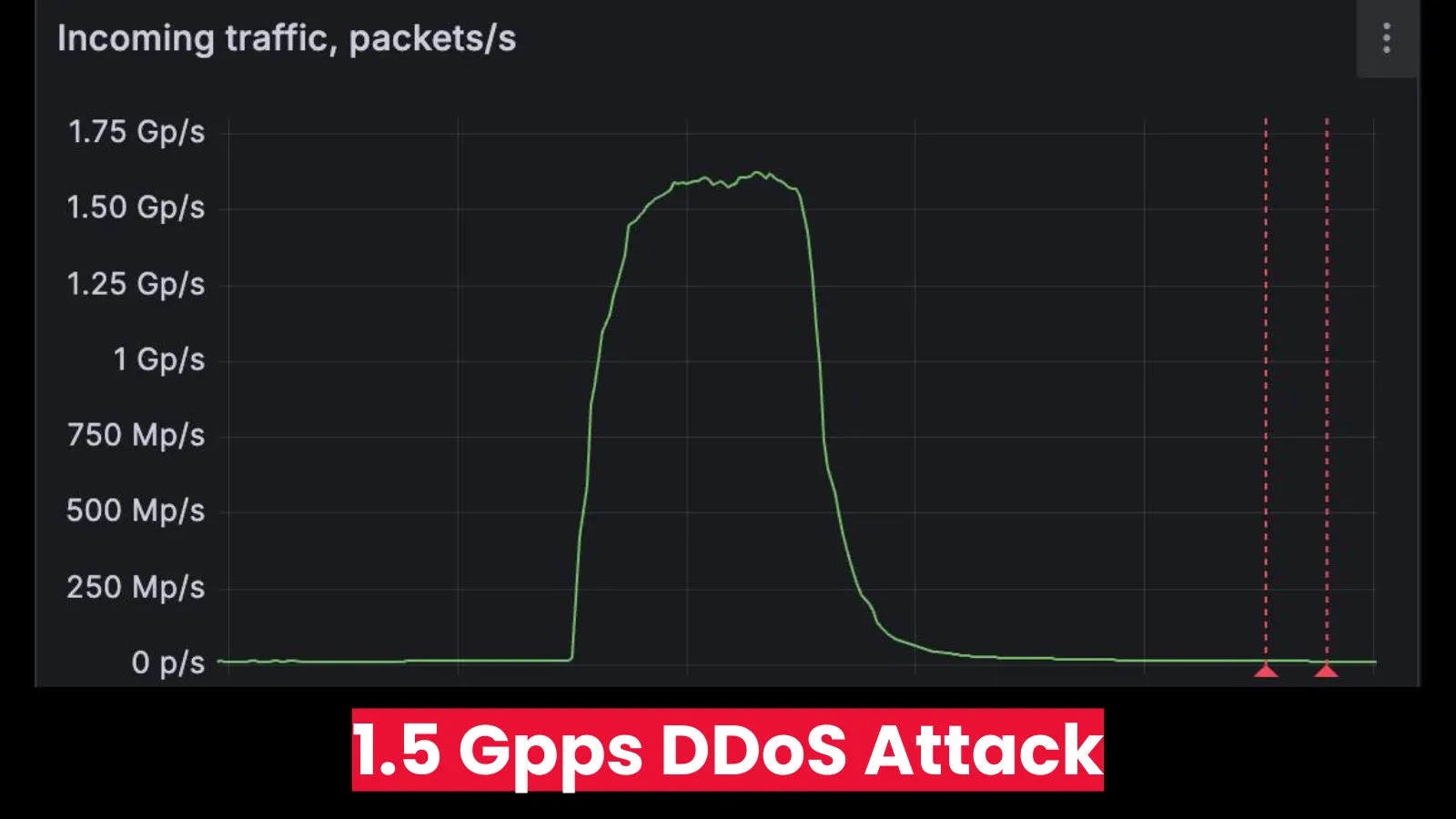
The digital landscape is a constant battleground, and even the most prepared organizations can find themselves under unprecedented assault. This week, the cybersecurity community [...]
The relentless wave of cyber threats has made robust cybersecurity no longer a luxury but a fundamental necessity for businesses of all sizes. Small [...]
New Phishing Attack Mimics Google AppSheet to Steal Login Credentials In the evolving landscape of cyber threats, attackers continually refine their tactics, leveraging legitimate [...]
A Cyber Adversary’s Unforced Error: When EDR Becomes an Insider Threat In a fascinating turn of events, a recent incident unveiled a significant operational [...]
The cybersecurity landscape is a relentless battleground, and sophisticated adversaries constantly devise new attack vectors to breach defenses. Among these, the infamous Lazarus Group, [...]
A sophisticated malvertising campaign is actively exploiting the desire for Meta Verified status, luring unsuspecting Facebook users into installing malicious browser extensions. This insidious [...]
The Silent Threat: AsyncRAT’s Fileless Onslaught and How to Fight Back The digital defense landscape faces a perpetual challenge: malware that learns, adapts, and [...]
Unauthenticated Admin Access: Critical Vulnerability in Amp’ed RF BT-AP 111 Bluetooth Access Point In the evolving landscape of enterprise network infrastructure, Bluetooth access points [...]
Unmasking the Threat: Cursor AI Code Editor’s Critical RCE Vulnerability The convergence of AI and integrated development environments (IDEs) promises unprecedented productivity. However, this [...]