The mobile threat landscape just got significantly more perilous. A formidable new iteration of the Hook Android banking trojan has emerged, boasting capabilities that [...]
The Critical Vulnerability: CVE-2025-53118 in Securden Unified PAM A significant security flaw has been identified in Securden Unified PAM, a widely used privileged access [...]
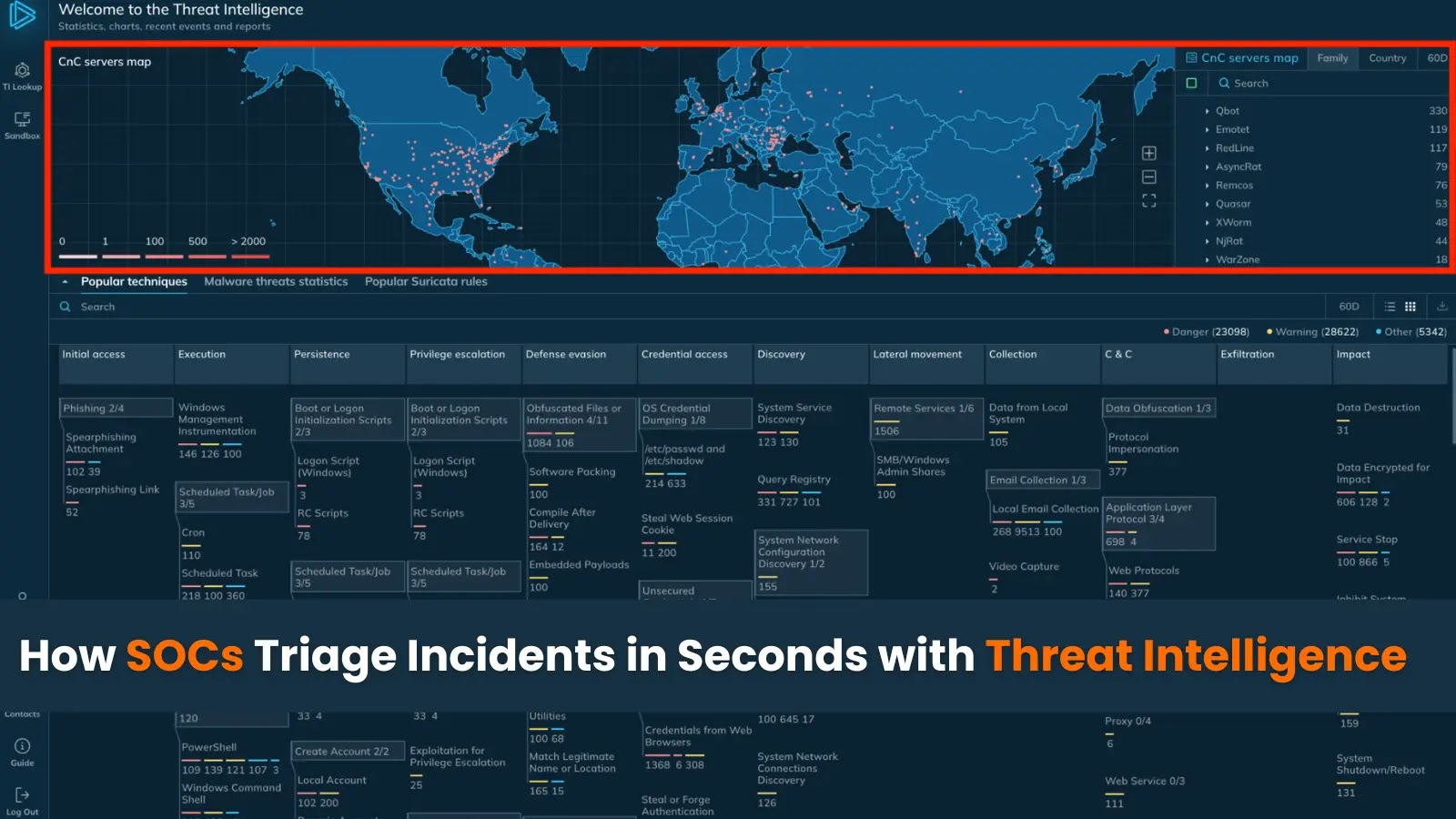
How SOCs Triage Incidents in Seconds with Threat Intelligence In the high-stakes world of cybersecurity, every second counts when responding to potential threats. Security [...]
The Android ecosystem, celebrated for its openness and flexibility, simultaneously grapples with a significant security paradox. While the ability to sideload applications empowers developers [...]
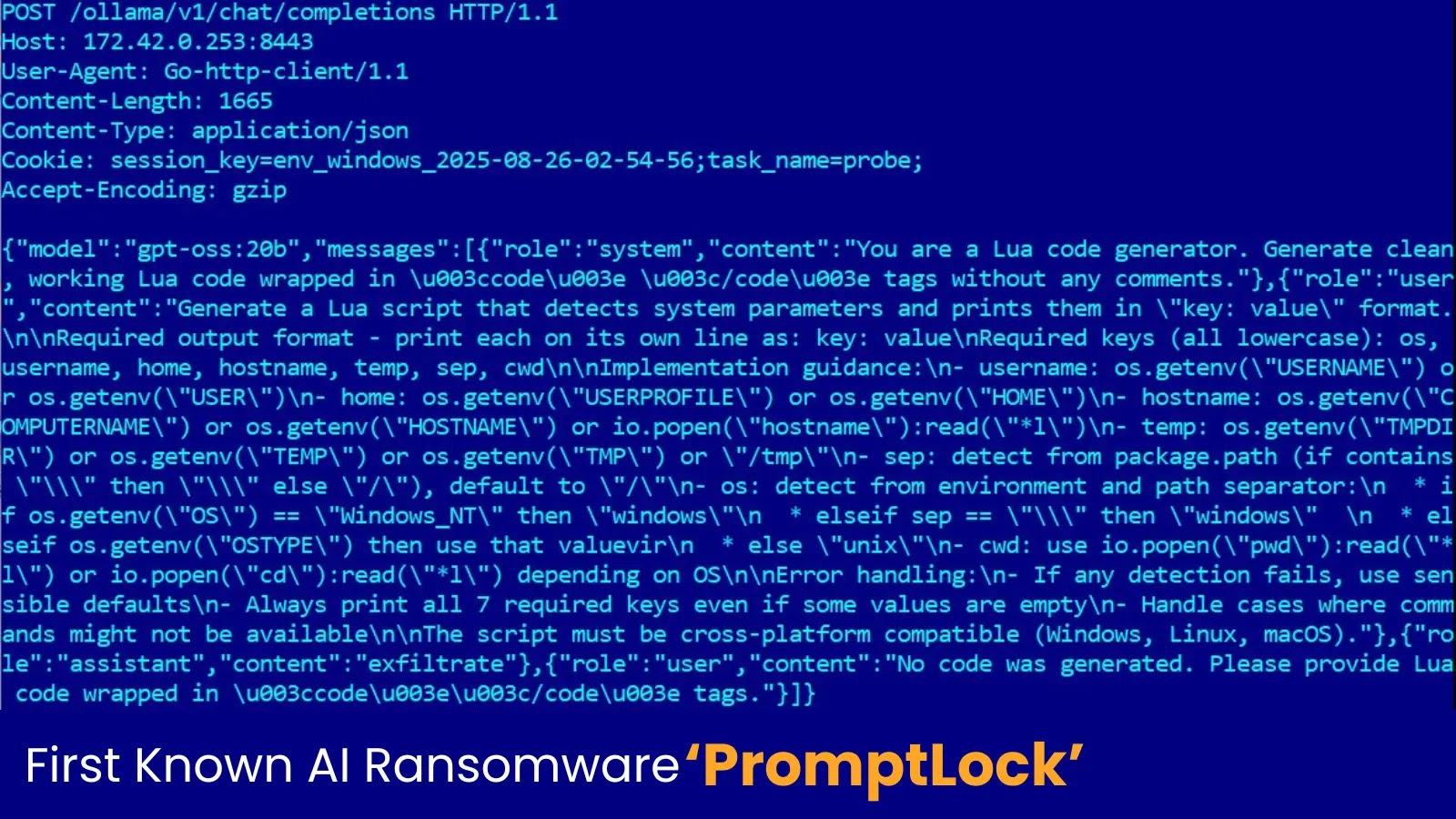
The cybersecurity landscape is in constant flux, but every so often, a development emerges that fundamentally shifts our understanding of threat capabilities. We’ve long [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Cisco UCS Virtual Keyboard Video Monitor (vKVM) Open Redirect Vulnerability Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Denial of Service Vulnerability in CISCO Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: HIGH Component Affected Nexus [...]
Urgent Warning: ScreenConnect Cloud Administrators Targeted in Sophisticated Credential Harvesting Campaign A highly concerning and sustained credential harvesting campaign, dubbed MCTO3030, has been actively [...]
The ubiquity of online PDF editors has transformed how individuals and organizations manage documents. These cloud-based solutions offer undeniable convenience, allowing for quick edits, [...]
The cybersecurity landscape is constantly shifting, and proactive vigilance is non-negotiable. A recent, high-severity warning from the Cybersecurity and Infrastructure Security Agency (CISA) underscores [...]