Unmasking the Disappearance: iOS 26 and the Eradication of Spyware Forensics The landscape of mobile device security has been irrevocably altered by the emergence [...]
nsKnox Redefines B2B Payments: Solving the ‘Impossible Triangle’ of Fraud Prevention The digital transformation of business operations has brought unprecedented efficiency, yet it has also [...]
The digital perimeter of our homes and businesses often begins and ends with a small, unassuming device: the Wi-Fi router. Yet, a recent and [...]
Urgent Alert: Apache Tomcat Vulnerabilities Open Door to Remote Code Execution The digital landscape is constantly under siege, and few components are as critical [...]
A chilling development has emerged from the cybersecurity landscape: the notorious Mem3nt0 mori hacker group has been actively exploiting a zero-day vulnerability in Google [...]
Warlock Ransomware Exploits SharePoint ToolShell Zero-Day: A Critical Alert for Organizations The cybersecurity landscape has been rattled by a new and dangerous development. In July [...]
Unmasking the Minecraft Imposter: A Python RAT’s Stealthy Infiltration The digital playground of gaming, often perceived as a realm of innocent entertainment, has once again [...]
The landscape of cyber threats is perpetually shifting, and staying ahead of sophisticated adversaries is paramount for national security and economic stability. Recently, the notorious [...]
MuddyWater Escalates Attacks with New Phoenix Backdoor Malware In an increasingly volatile cyber landscape, the Iran-linked Advanced Persistent Threat (APT) group MuddyWater, also known as [...]
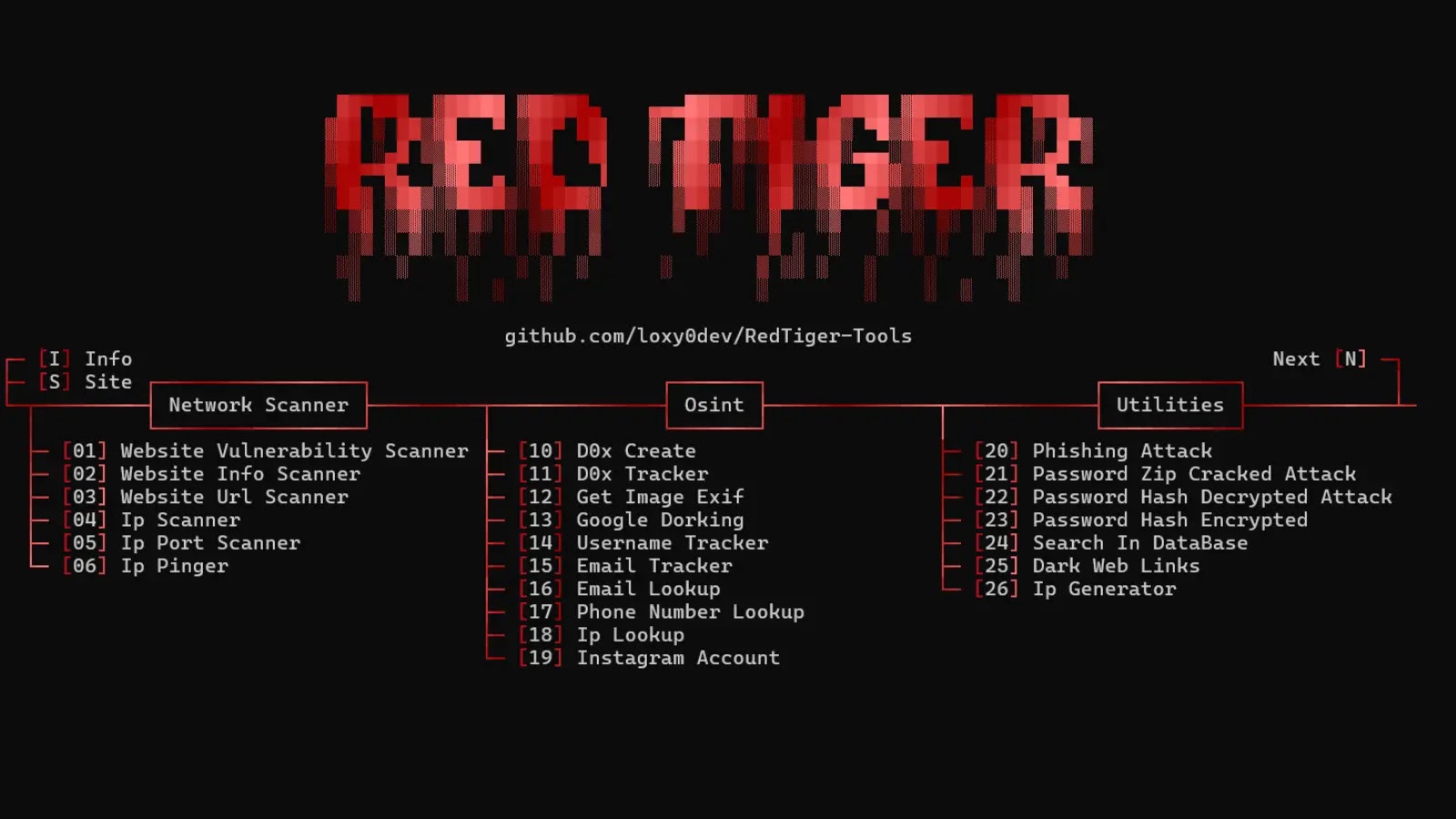
The Trojan Horse in Your Gaming Rig: RedTiger Repurposed for Digital Espionage The lines between legitimate tools and malicious payloads are blurring, and nowhere is [...]