Ghost Calls: The Covert Web Conferencing Attack You Need To Know About The landscape of cyber threats is in constant flux, with attackers consistently innovating [...]
The digital battlefield against cybercrime continues to intensify, often in unseen skirmishes that protect millions of users. A recent announcement from Meta, WhatsApp’s parent [...]
The year is 2025. The cloud landscape, once a frontier of innovation, has fully matured into the battleground for enterprise security. Attacks aren’t just sophisticated; [...]
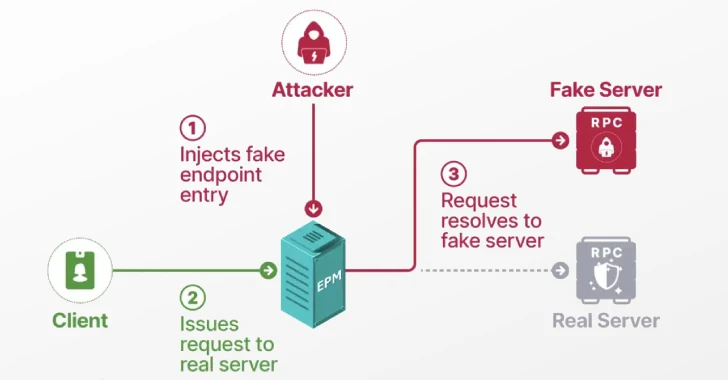
Unmasking the Impersonator: Windows EPM Poisoning and Domain Privilege Escalation In the intricate landscape of enterprise cybersecurity, a single, seemingly minor vulnerability can form [...]
Unveiling the Covert Threat: Lenovo Webcam Flaws Enable BadUSB Attacks The ubiquity of integrated webcams in modern laptops often belies a critical security vulnerability [...]
In the shadowy corners of the internet, where anonymity reigns supreme and traditional financial regulations hold no sway, darknet markets facilitate illicit trade. These [...]
Google Confirms Salesforce Data Breach: What IT Professionals Need to Know The digital landscape is a constant battleground, and even the most formidable tech [...]
Malicious Go and npm Packages: A New Frontier for Cross-Platform Malware and Data Wipes The software supply chain continues to be a prime target [...]
The digital battlefield is expanding, and nation-state actors are continually refining their asymmetric warfare capabilities. Recent events, particularly a 12-day conflict between Israel and [...]
In the cybersecurity landscape, a swift and accurate understanding of emerging threats is paramount. Recently, concerns flared regarding a potential zero-day vulnerability impacting SonicWall’s [...]