The digital landscape is a constant battleground, and even the most innovative technologies can become weapons in the wrong hands. A recent, sophisticated phishing campaign [...]
Navigating the Windows 11 Shift: Essential Forensic Artifacts for Investigators As Microsoft officially sunsets Windows 10 support today, October 14, 2025, organizations worldwide are confronted [...]
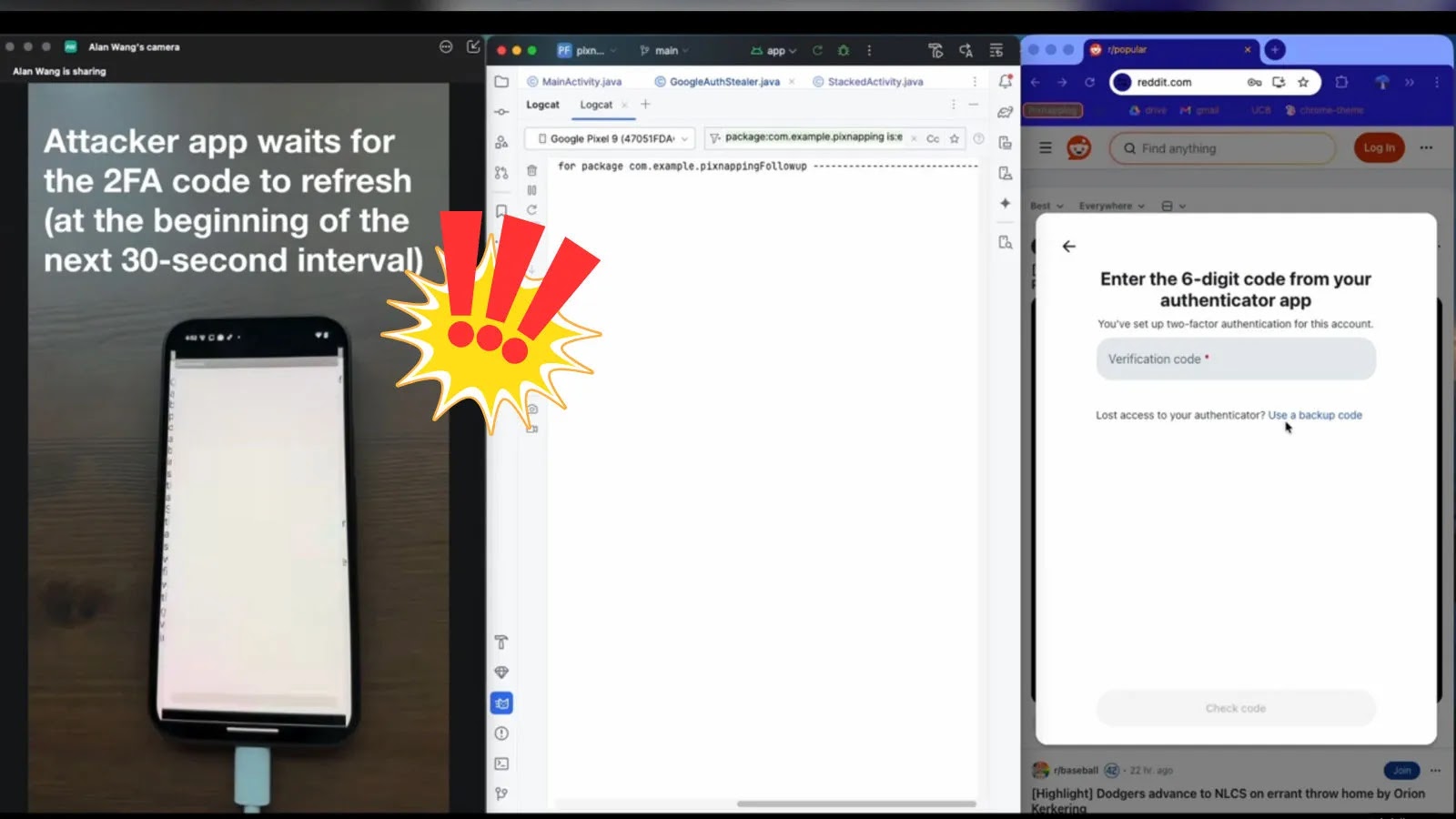
Unmasking Pixnapping: A Critical Threat to Your 2FA Security In a landscape where multi-factor authentication (MFA) stands as a cornerstone of digital security, a newly [...]
The Digital Deception: North Korean IT Workers Bypassing Security with VPNs and ‘Laptop Farms’ The digital landscape is a battleground where anonymity can be both [...]
Unmasking TA585: A New Era of Web Injection and MonsterV2 Malware Attacks The cybersecurity landscape is constantly shifting, with threat actors continuously refining their methods [...]
A disturbing revelation has sent ripples through the digital invoicing ecosystem: the unearthing of a publicly accessible database managed by Invoicely, a prominent invoicing and [...]
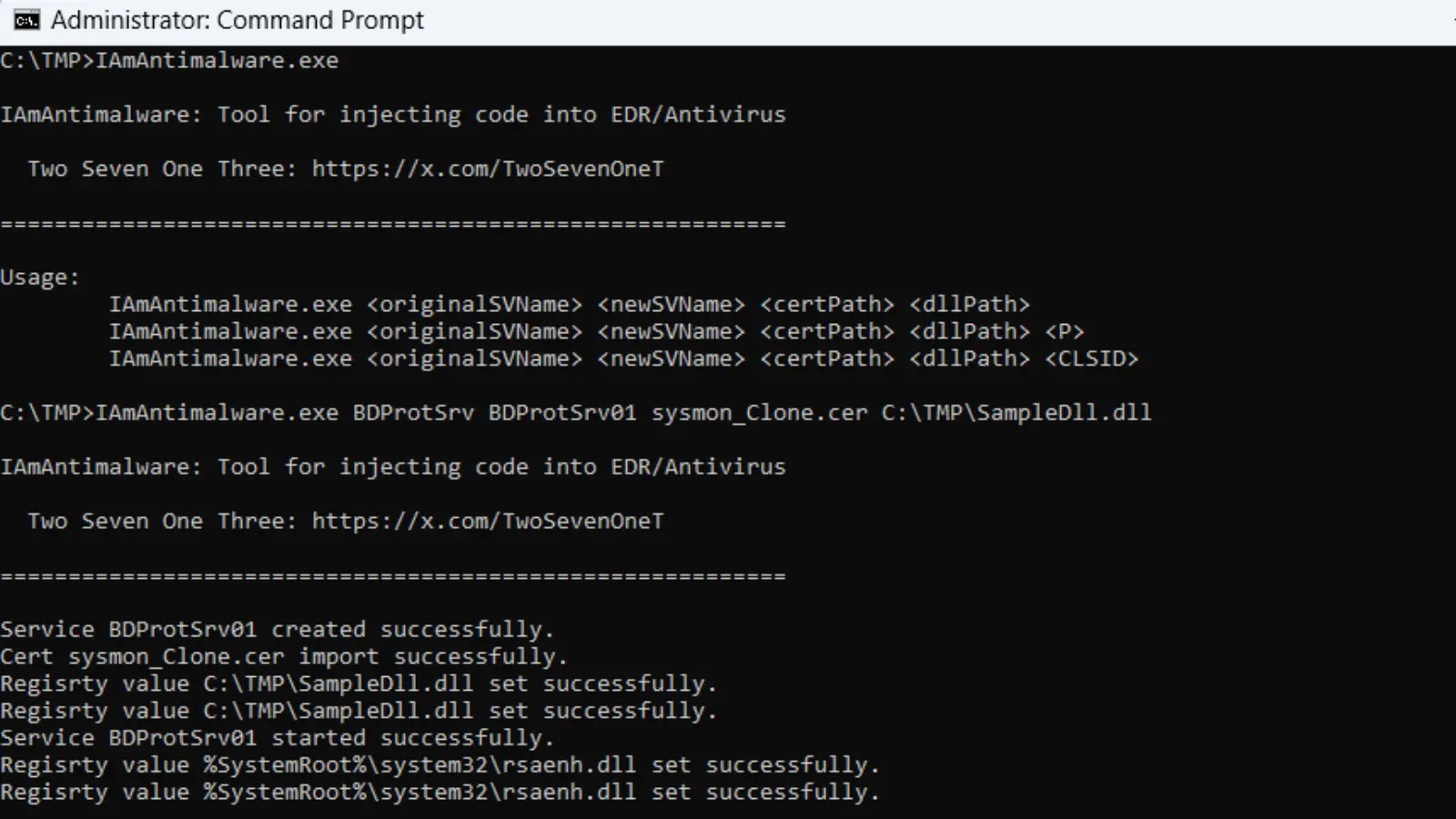
Recent developments in the cybersecurity landscape have unveiled a concerning new threat: the IAmAntimalware tool. This sophisticated utility, designed to subvert the very software intended [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Multiple vulnerabilities in SAP Products Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: High Software Affected SAP NetWeaver [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Multiple Cross-Site Scripting Vulnerabilities in Junos Space Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: CRITICAL Software Affected [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Remote code execution Vulnerabilities in Ivanti Endpoint Manager Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: HIGH Software [...]