The Python Package Index (PyPI), the official third-party software repository for Python, has issued an urgent warning to developers. A sophisticated phishing campaign is [...]
The digital landscape is a constant battleground, where even the most sophisticated tools can harbor hidden dangers. A recent discovery has sent ripples through [...]
For years, the promise was tantalizing: modern JavaScript frameworks like React would relegate Cross-Site Scripting (XSS) to the annals of history. Developers embraced their [...]
The digital landscape is a constant battleground, and a new threat has emerged, specifically targeting Microsoft Internet Information Services (IIS) servers. Cybersecurity researchers have [...]
The digital perimeter of many organizations relies heavily on robust firewall solutions. When critical vulnerabilities emerge in these foundational security tools, the implications can [...]
The cybersecurity landscape is in a constant state of flux, with threat actors continuously refining their strategies to breach defenses. A recent and particularly concerning [...]
In a significant development for the cybersecurity landscape, a new threat actor, dubbed Storm-2603, has been identified deploying a sophisticated backdoor framework, AK47 C2 [...]
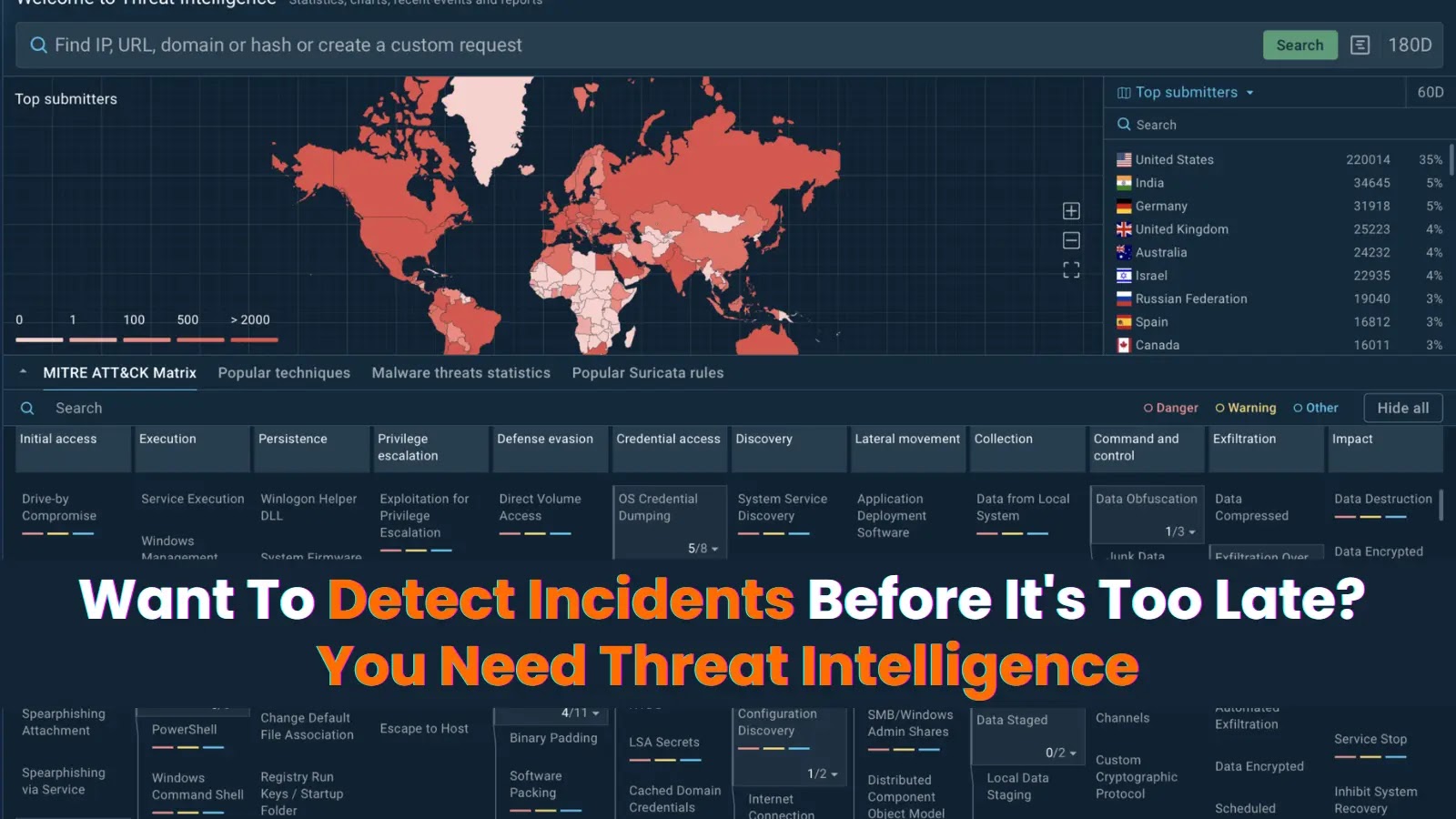
Want To Detect Incidents Before It’s Too Late? You Need Threat Intelligence The difference between a minor security incident and a devastating breach often [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Multiple Vulnerabilities in Sonicwall Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: HIGH Software Affected SonicOS SMA100 series [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Multiple vulnerabilities in Drupal Modules Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: HIGH Software Affected Drupal Real-time [...]