TP-Link NVR Vulnerabilities: A Critical Threat to Surveillance Infrastructure The security of our physical spaces increasingly relies on robust surveillance systems. However, recent discoveries [...]
Unveiling Fire Ant: A Persistent Threat to VMware ESXi and vCenter Environments The digital perimeter of many organizations rests significantly on their virtualization infrastructure. [...]
A significant security flaw has been identified in Mitel’s MiVoice MX-ONE communication platform, posing a serious risk to organizations utilizing this system. This critical vulnerability, [...]
SharePoint Under Siege: Unpacking the “ToolShell” 0-Day Exploits Microsoft SharePoint, a cornerstone collaboration platform for countless organizations worldwide, has recently been at the epicenter [...]
In an increasingly interconnected digital landscape, new malware strains emerge with disturbing regularity, evolving tactics to bypass traditional defenses. One such recent discovery demanding [...]
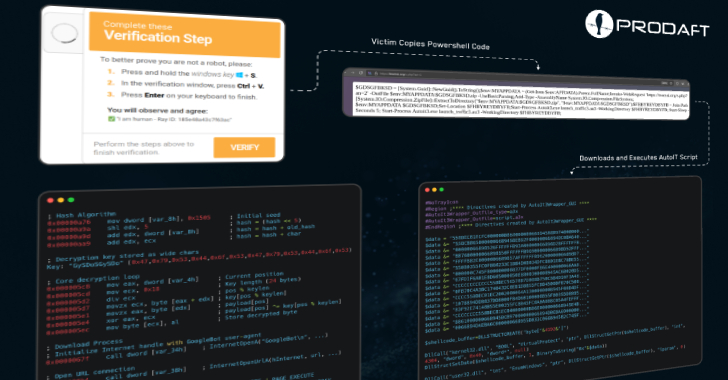
The cybersecurity landscape currently faces a pressing threat: highly sophisticated campaigns leveraging unconventional methods to deliver potent malware. A recent, significant development reveals threat actors [...]
Unmasking ACRStealer: The New Threat Exploiting Google Docs and Steam for Covert C2 The landscape of cyber threats is perpetually shifting, with adversaries continually [...]
For organizations relying on robust network security, urgent news demands immediate attention: both Sophos and SonicWall have issued critical patches addressing severe remote code execution [...]
Unprecedented DDoS Barrage: NoName057(16) Strikes 3,700 Unique Devices The digital battleground is constant, and understanding the tactics of formidable adversaries is crucial for robust [...]
Unmasking Operation GhostRAT & PhantomNet: A Targeted Espionage Campaign The digital landscape is a battleground, and sophisticated cyber espionage operations are a constant threat. [...]