Unmasking the Agent Tesla Campaign: Process Hollowing and Anti-Analysis Evasion The digital landscape is a constant battleground. While new threats emerge daily, it’s the persistent [...]
Google Ads stands as a cornerstone of online advertising, a platform millions trust daily for sponsored search results. Users click these links, confident in the [...]
In the rapidly evolving landscape of digital communication, trust is paramount. Yet, cybercriminals continually innovate, exploiting even the most trusted platforms. A recent campaign, uncovered [...]
In a chilling revelation that underscores the increasing sophistication of state-sponsored surveillance, a new Android spyware dubbed ResidentBat has been definitively linked to the Belarusian [...]
Unmasking Oblivion: The $300 Android RAT Threatening Mobile Security A new and alarming threat has emerged in the Android malware landscape: Oblivion. This sophisticated Remote [...]
The cyber threat landscape is in a constant state of flux, but one category consistently claims the spotlight: infostealers. These insidious forms of malware have [...]
Wireshark 4.6.4: Critical Update Fortifies Network Analysis Against Security Threats For network professionals, security analysts, and developers, Wireshark isn’t just a tool; it’s an indispensable [...]
The digital frontier of Web3, promising decentralization and unprecedented user control, is simultaneously a fertile ground for highly sophisticated cyber threats. A recent, deeply concerning [...]
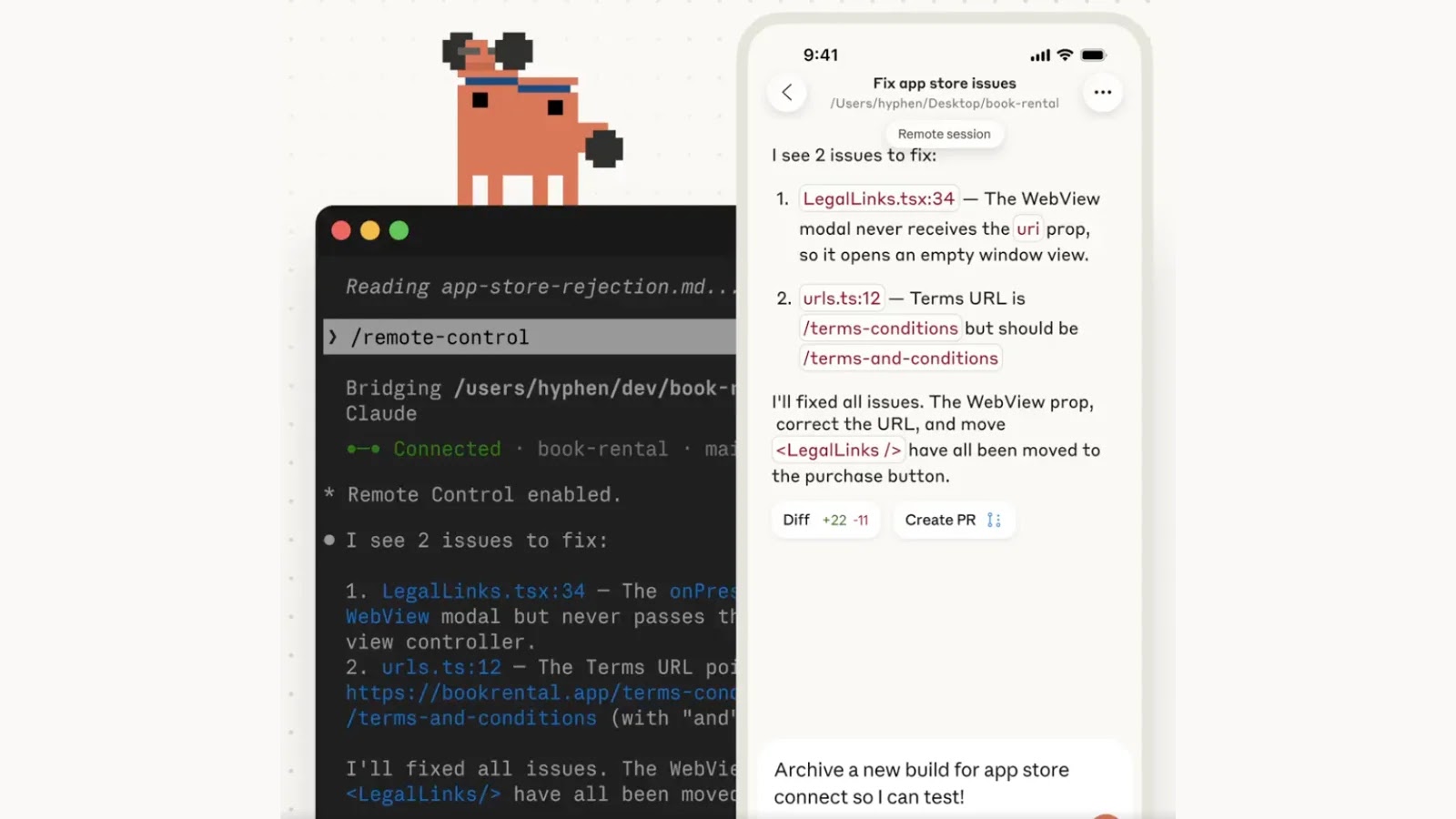
In a significant move poised to reshape how developers interact with their terminal environments, Anthropic has unveiled a new “Remote Control” feature for its agentic [...]
Organizations worldwide rely on enterprise AI platforms to streamline operations, enhance decision-making, and drive innovation. Among these, ServiceNow stands out as a critical component for [...]