Weaponized AI: OpenAI Confirms ChatGPT Used by Chinese State-Linked Hackers The digital battleground just got a lot more complex. In a sobering revelation, OpenAI has [...]
The web is a dynamic landscape, constantly evolving to deliver richer user experiences. This evolution, however, often introduces new security challenges. Among the most pervasive [...]
Leadership changes at key cybersecurity firms often signal strategic shifts and amplify a company’s capacity to address evolving threats. When a trusted leader in identity [...]
Critical Windows Vulnerability Uncovered: PoC Released for Unrecoverable BSODs A significant cybersecurity threat has emerged for Windows users, with a publicly released proof-of-concept (PoC) [...]
The landscape of software development is undergoing a profound transformation, with artificial intelligence increasingly woven into every stage of the software supply chain. While AI [...]
In a stark reminder that even the oldest digital skeletons can rattle the foundations of modern security, a newly confirmed vulnerability in the Telnet daemon [...]
Unmasking Decade-Long Espionage: Google Dismantles Chinese Hacking Infrastructure The digital shadows have once again been illuminated, revealing a highly sophisticated and disturbingly pervasive cyber [...]
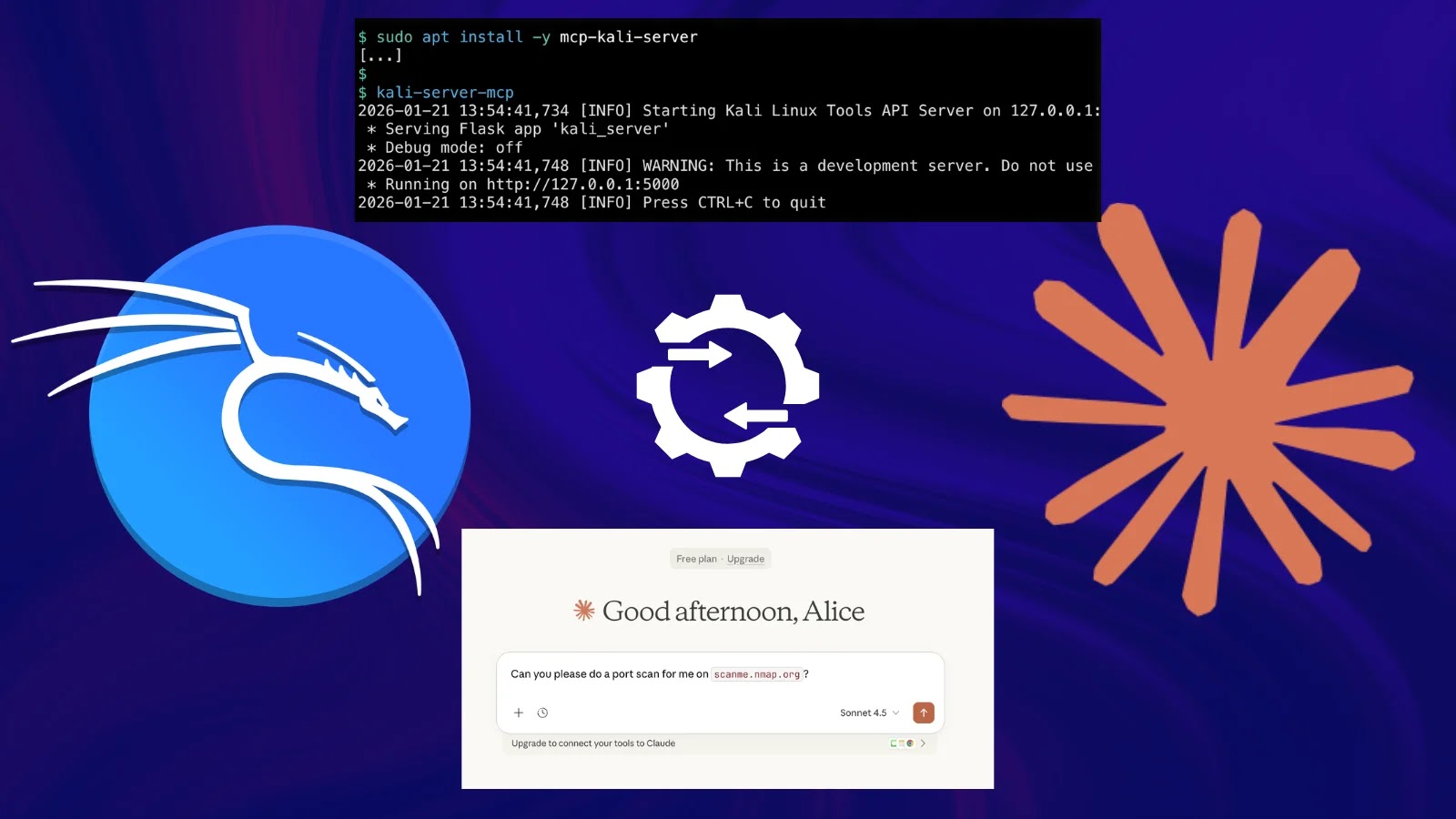
Unveiling the Future of Penetration Testing: Kali Linux Integrates Claude AI The landscape of cybersecurity is constantly reshaped by innovation. For penetration testers, the [...]
Unmasking SURXRAT: A New Android Threat Landscape The mobile threat landscape is undergoing a significant transformation. We’re observing a clear shift towards highly professionalized [...]
The digital landscape is a constant battleground, where cybercriminals relentlessly evolve their tactics to exploit the trust users place in legitimate brands. A particularly sophisticated [...]