Pushing the Limits of Wi-Fi 7 performance with Wi-Fi. Unleashing the Power of Wi-Fi 7: Boosting Performance to New Heights with this Cutting-Edge Technology Wi-Fi 7, [...]
What are the potential possibilities of Wi-Fi 7? Multi-Gigabit Speeds: Wi-Fi 7 could potentially offer even higher data rates and throughput compared to previous Wi-Fi [...]
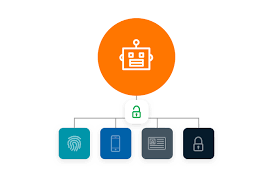
Five key principles of Resilience – PAM Privileged Access Management (PAM), there are several key principles that contribute to building resilience and enhancing security. While [...]
Protecting Backups with PAM Protecting backups with Privileged Access Management (PAM) involves securing and controlling access to privileged accounts and actions that can impact backup [...]
Are PAM (Privileged Access Management) and IAM (Identity And Access Management) the same? Let us explain the difference. PAM and IAM are same or not. [...]
How does Privileged Process Automation Work? Privileged Process Automation (PPA) refers to the automation of privileged tasks and processes within an organization’s IT infrastructure. It [...]
How is WIFI 7 different from WIFI 6/6E ? Wi-Fi 7, also known as Wi-Fi 7th generation or Wi-Fi 7x, is the upcoming wireless networking [...]
What’s the right choice for automating IT processes? The right choice for automating IT processes depends on the specific needs, goals, and resources of your [...]
What are the Ransomware attacks and preventing ransomware from being devasting What are Ransomware attacks? Ransomware attacks are a type of malicious cyber attack where [...]
Responding to the Unique needs of Managed Security Service Provider. Managed Security Service Providers (MSSPs) play a crucial role in helping organizations address their security [...]