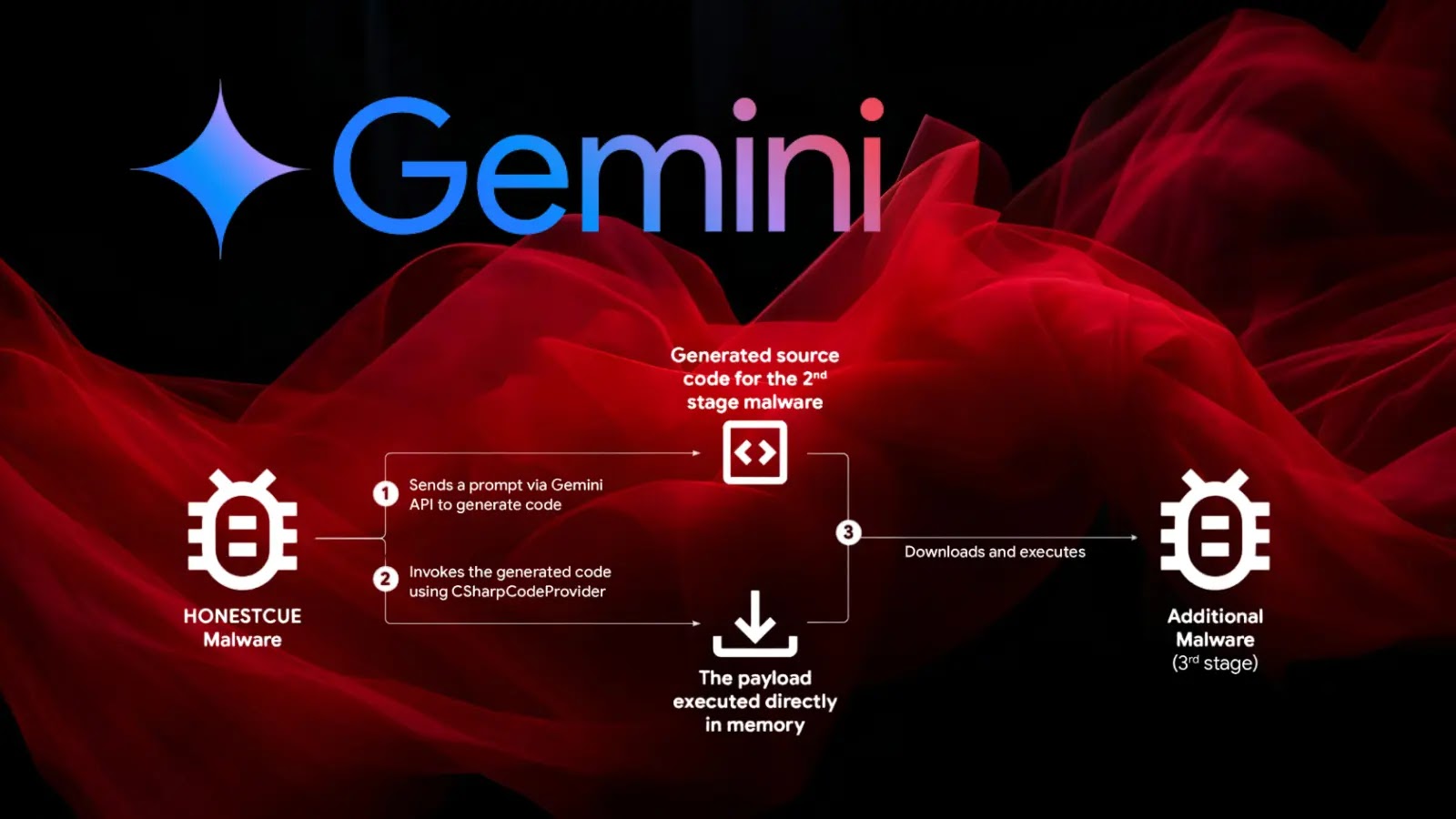
The AI Paradox: When Advanced Models Become a Cybercrime Enabler The landscape of cyber threats is in constant flux, but few developments are as [...]
A new and insidious threat has surfaced within the vast ecosystem of the Node Package Manager (NPM). Developers, typically reliant on NPM for seamless integration [...]
Urgent Chrome Security Update: Patching Critical Code Execution Vulnerabilities The digital landscape is a constant battleground, and staying ahead of threats is paramount for [...]
The digital landscape is a dynamic battleground, and for the nearly 800,000 websites relying on the WPvivid Backup & Migration WordPress plugin, a recently disclosed [...]
The digital battleground is constantly shifting, and advanced persistent threats (APTs) continually refine their tactics. A recent incident response engagement in September 2025 unveiled [...]
A disturbing new threat has emerged on the cybersecurity landscape: a self-propagating SSH worm capable of compromising Linux systems in mere seconds. Observed by [...]
Feiniu NAS Devices Under Siege: Unpatched Vulnerabilities Fueling Netdragon Botnet Campaign In a pressing development for data security, Feiniu (fnOS) Network Attached Storage devices [...]
Odido Telecom Cyberattack: 6.2 Million Customer Accounts Exposed The digital landscape consistently reminds us of the paramount importance of robust cybersecurity. A recent incident [...]
DragonForce Ransomware Group: A Cartel-Like Expansion Threatening Businesses Globally The digital threat landscape is in a constant state of flux, with new and increasingly sophisticated [...]
A disturbing alert has just been issued by the Cybersecurity and Infrastructure Security Agency (CISA), adding a critical code execution vulnerability in Notepad++ to [...]