Russia’s Digital Iron Curtain: The Attempted WhatsApp Block and Its Implications In a move stirring significant global concern, Russia has reportedly escalated its efforts [...]
Organizations worldwide are facing an unprecedented and alarming surge in cyberattacks. A critical zero-day vulnerability, tracked as CVE-2026-1281, plaguing Ivanti Endpoint Manager Mobile (EPMM) systems [...]
In an alarming escalation of cyber warfare, a sophisticated threat actor, dubbed RU-APT-ChainReaver-L, has launched one of the most intricate cross-platform supply chain campaigns observed [...]
The modern battlefield is no longer confined to physical landscapes; it has aggressively expanded into the digital infrastructure and intricate supply chains that underpin [...]
The landscape of cyber threats is in constant flux, with adversaries continually refining their tactics and tools. A recent development that has captured the [...]
The digital defenses of Apple users were recently put to the test, with a critical zero-day vulnerability in the core operating system component, dyld, [...]
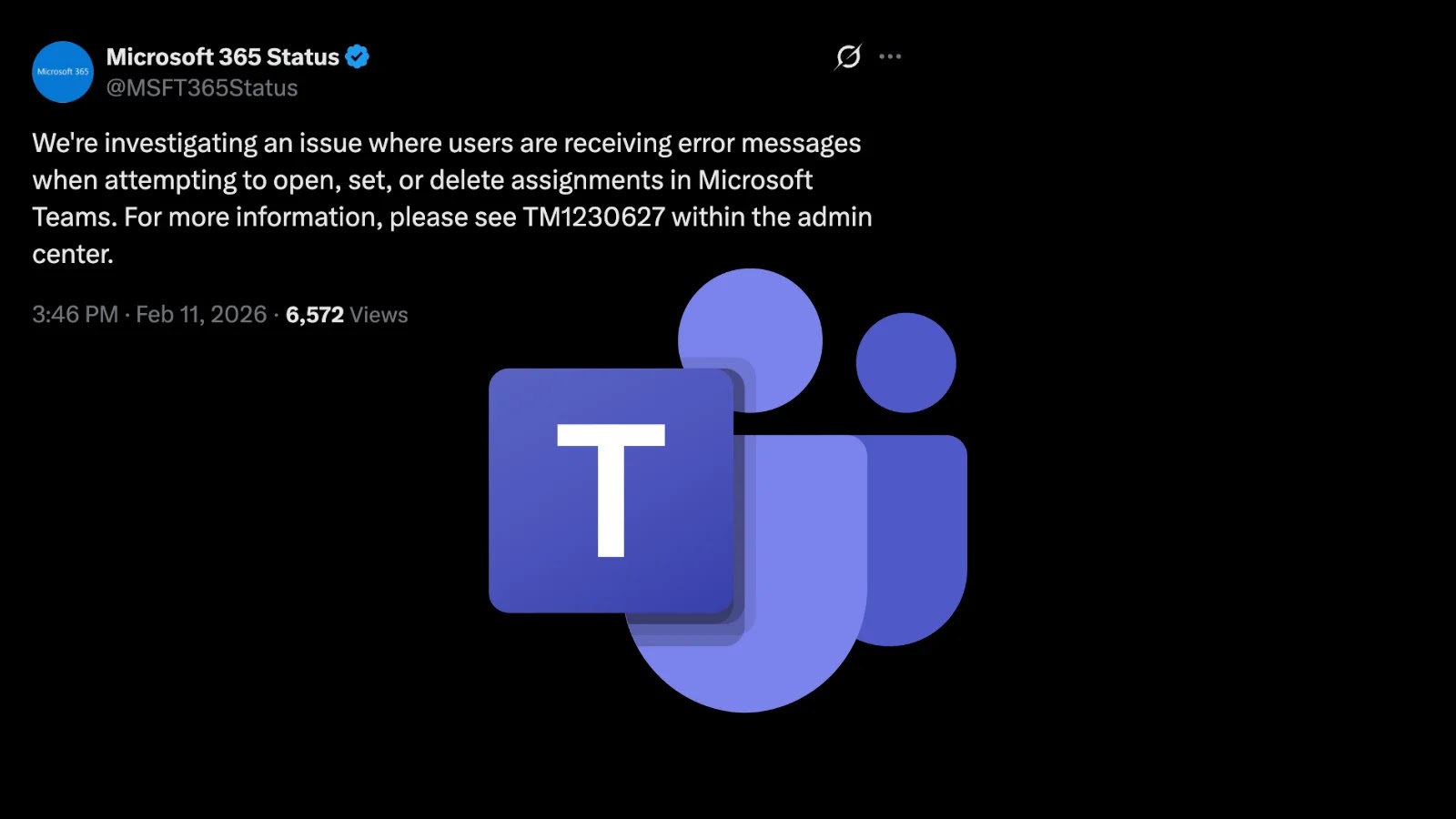
The digital classroom and collaborative workspace have become staples of modern productivity, with Microsoft Teams leading the charge. Yet, even the most robust platforms aren’t [...]
In the relentless pursuit of digital resilience, Microsoft has once again delivered foundational security enhancements. As cyber threats become increasingly sophisticated, the timely deployment of [...]
Cephalus Ransomware: A New Go-Based Double-Extortion Threat Targeting Exposed RDP The cybersecurity landscape continues to evolve at an alarming pace, with new threats surfacing regularly. [...]
Urgent Alert: Desktop Window Manager 0-Day Puts Windows Systems at Risk A critical zero-day vulnerability impacting the Windows Desktop Window Manager (DWM) is currently under [...]