—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Multiple Vulnerabilities in Microsoft Products Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: High Software Affected Microsoft Windows [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Remote Code Execution Vulnerability in Beyond Trust products Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: HIGH Software [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Multiple Vulnerabilities in Aruba Products Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: MEDIUM Software Affected HPE Aruba [...]
CISA Sounds the Alarm: Six Microsoft 0-Day Vulnerabilities Under Active Exploitation The cybersecurity landscape just became significantly more precarious. The U.S. Cybersecurity and Infrastructure Security [...]
The Coinbase Cartel: A New Era of Data-Theft Extortion The cybersecurity landscape is in constant flux, with threat actors continuously refining their methodologies. A [...]
Windows Remote Access Connection Manager 0-Day: A Critical DoS Threat Patched The digital landscape is a constant battleground, and even the most trusted system components [...]
Imagine meticulously planning the most important day of someone’s life, only to have your systems infiltrated by a sophisticated cyberattack. This isn’t a hypothetical scenario; [...]
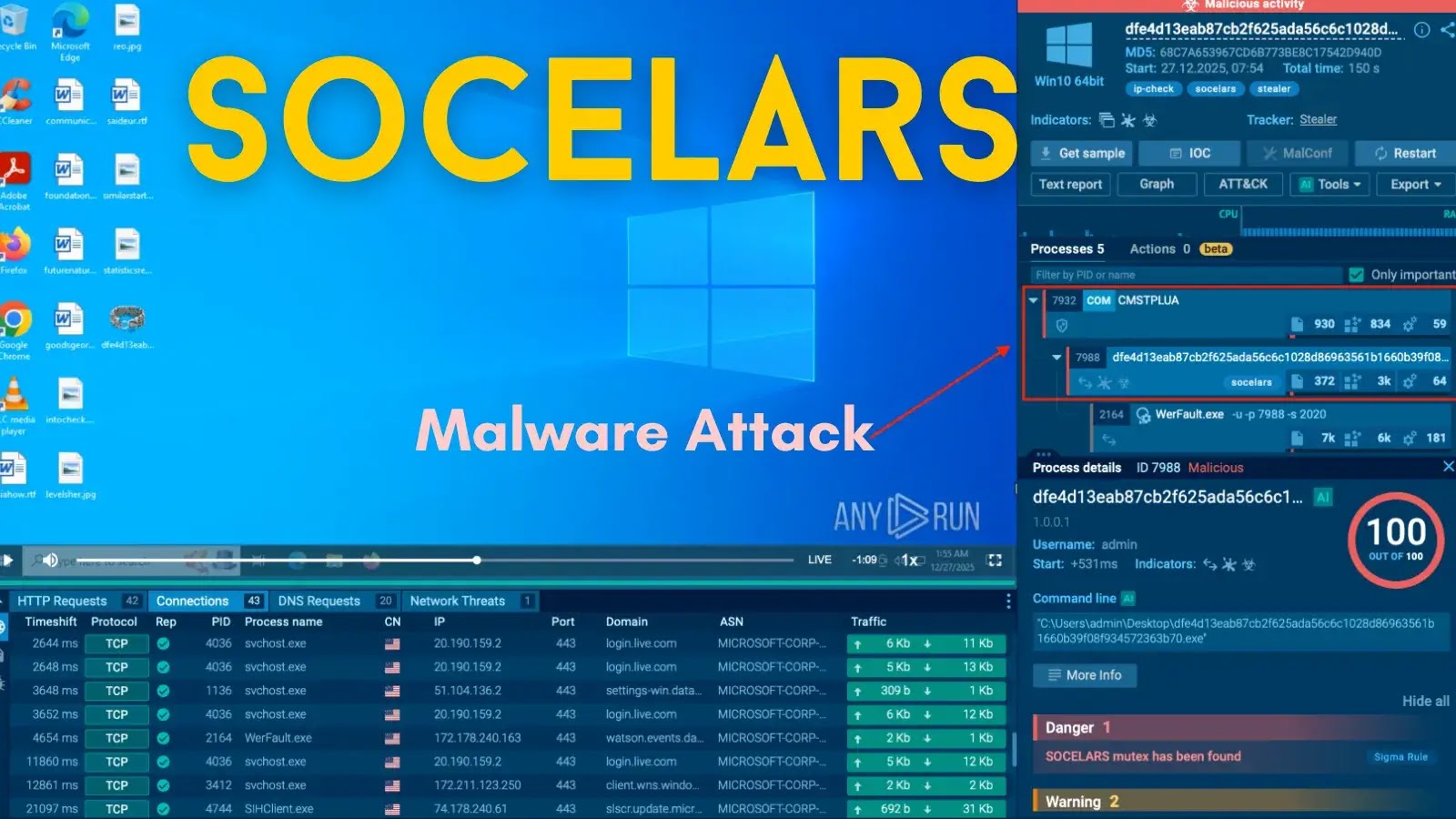
Unmasking Socelars: The Silent Threat to Your Business Data The digital landscape is under constant siege, and a new, insidious threat has emerged: Socelars. [...]
A silent alarm just sounded across the Windows ecosystem. Microsoft recently issued critical Patch Tuesday updates, addressing a zero-day vulnerability in the Windows Shell that [...]
Urgent GitLab Update: Patching Critical DoS and XSS Vulnerabilities GitLab, a cornerstone for millions of developers and IT teams worldwide, has issued a critical [...]