The speed at which cloud misconfigurations are exploited is alarming. Attackers aren’t just scanning for weaknesses; they’re industrializing the process, turning individual vulnerabilities into self-propagating [...]
Microsoft 365 Admin Center Outage Plagues North American Users Few things send a chill down an IT administrator’s spine quite like losing control of [...]
In the dynamic landscape of enterprise IT, endpoint management solutions are critical for maintaining control, security, and operational efficiency across a vast array of devices. [...]
FortiOS Authentication Bypass Vulnerability: A Deep Dive into CVE-2026-22153 The security landscape is a constant battleground, with new threats emerging regularly. A recent disclosure [...]
For over a decade, specific governmental and defense entities within India have navigated a persistent digital threat landscape. This pervasive espionage ecosystem, predominantly orchestrated by [...]
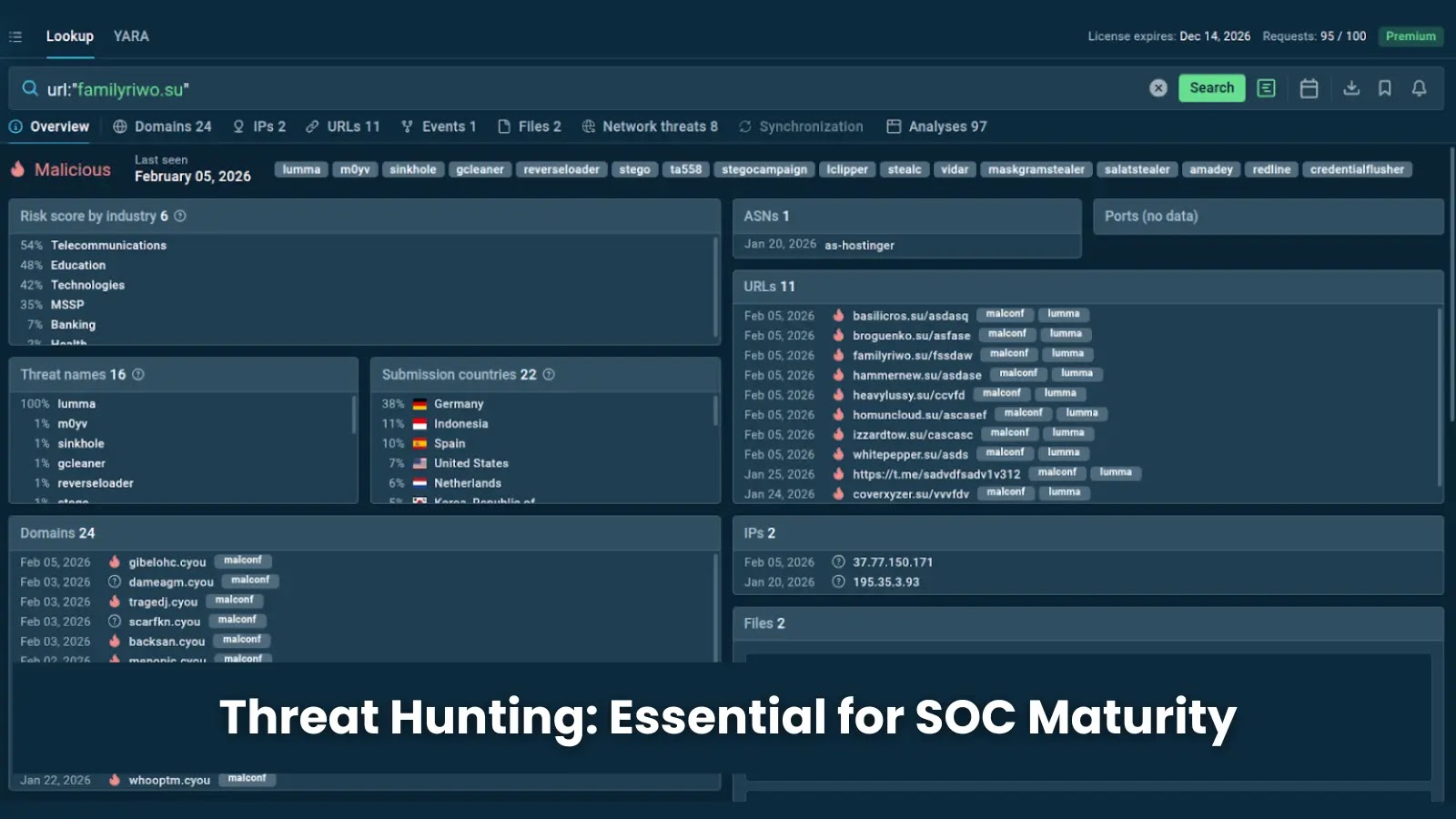
The Paradox of Threat Hunting: Critical for SOC Maturity Yet Often Missing Real Attacks Threat hunting is a foundational pillar of any robust Security [...]
Unpacking CVE-2025-52436: A Critical XSS Vulnerability in FortiSandbox The cybersecurity landscape has once again been rattled, this time by a high-severity cross-site scripting (XSS) [...]
Microsoft Patch Tuesday February 2026: A Critical Security Bulletin February 2026 brought a significant security update from Microsoft, as the company released its monthly [...]
The digital defense perimeter of organizations worldwide just experienced another critical breach. A recently disclosed zero-day vulnerability in Windows Remote Desktop Services (RDS), tracked as [...]
UNC1069: North Korea’s Evolving Threat to the Finance Sector with AI-Powered Attacks The financial services industry, a prime target for financially motivated cybercriminals, is currently [...]