In a stark reminder of the persistent and evolving threat landscape, Russian state-sponsored hacking group APT28, also known as Fancy Bear or Strontium, has launched [...]
The digital landscape is a torrent of information, and the integrity of that information is paramount, especially when facing critical decisions like insurance claims. Tampered [...]
Cybercriminals are continually refining their tactics, and a significant shift has occurred towards sophisticated social engineering. This evolution aims to bypass traditional, often robust, perimeter [...]
A disturbing trend has emerged in the cybersecurity landscape: threat actors are actively compromising NGINX servers, not with traditional malware, but by subtly altering [...]
The Devious New Malvertising Chain Exploiting Facebook Ads A disturbing new trend is emerging within the digital advertising landscape, weaponizing the vast reach of [...]
Unmasking DesckVB RAT: A Sophisticated Takedown of an Evolving Threat The digital landscape is a constant battlefield, where new and more complex threats emerge [...]
A disturbing trend has emerged in the cybersecurity landscape: advanced persistent threat (APT) actors are increasingly camouflaging sophisticated malware within seemingly innocuous application installers. [...]
A Disturbing Compromise: Notepad++ Update Infrastructure Abused in Targeted Supply Chain Attack The ubiquity of software updates, designed to enhance features and patch vulnerabilities, [...]
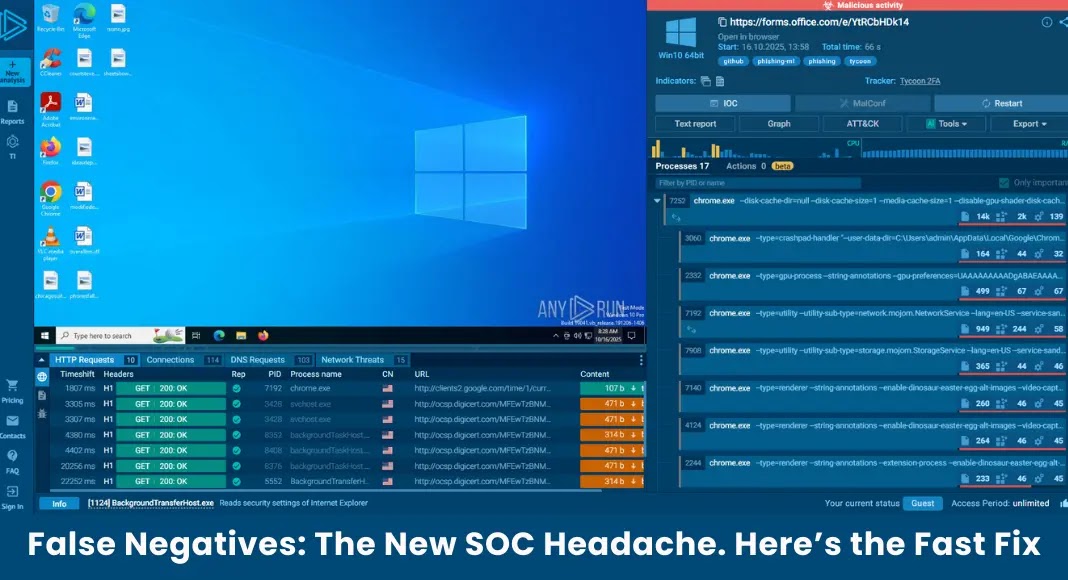
The Silent Killer: How False Negatives Are Costing Your SOC Dearly The cybersecurity landscape is a relentless battlefield, and while much attention focuses on [...]
The silent infiltrator. It’s a phrase that haunts the cybersecurity landscape, especially when discussing sophisticated malware loaders. Recently, a new and particularly cunning custom loader, [...]