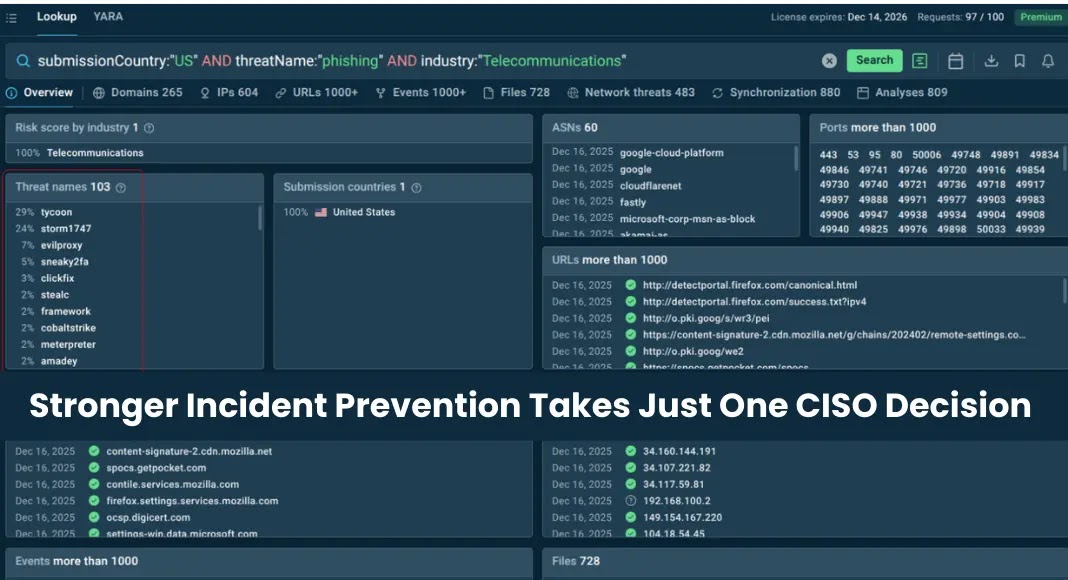
In the complex theater of cybersecurity, a persistent and often misleading narrative suggests that when the digital battleground gets noisy, the immediate solution is [...]
A disturbing trend has emerged in the cybersecurity landscape: threat actors are actively leveraging a critical remote code execution (RCE) vulnerability within React Native’s Metro [...]
The ubiquity of PDF documents in professional and personal workflows makes the tools we use to interact with them critical components of our digital security [...]
Mac Under Threat: Infostealers Leverage Python and Trusted Platforms The digital threat landscape is in constant flux, and a concerning trend has emerged: infostealer [...]
The Deceptive Lure of Fake Dropbox: Unpacking a Multi-Stage Phishing Attack The digital landscape is a constant battleground, and cybercriminals are relentlessly innovating. A [...]
The digital supply chain is a bedrock of modern software development, yet it remains a critical attack vector for malicious actors. A recent and [...]
The digital landscape is a constant battleground, and even the most innovative technologies can become targets. Just two months after its disclosure, a critical [...]
Mozilla Empowers Users: Firefox Introduces Comprehensive AI Kill Switch The integration of artificial intelligence into everyday software continues at an unprecedented pace, bringing both innovation [...]
Chollima APT Strikes: LNK File Weaponization in “Operation: ToyBox Story” In the high-stakes arena of state-sponsored cyber warfare, advanced persistent threat (APT) groups continually refine [...]
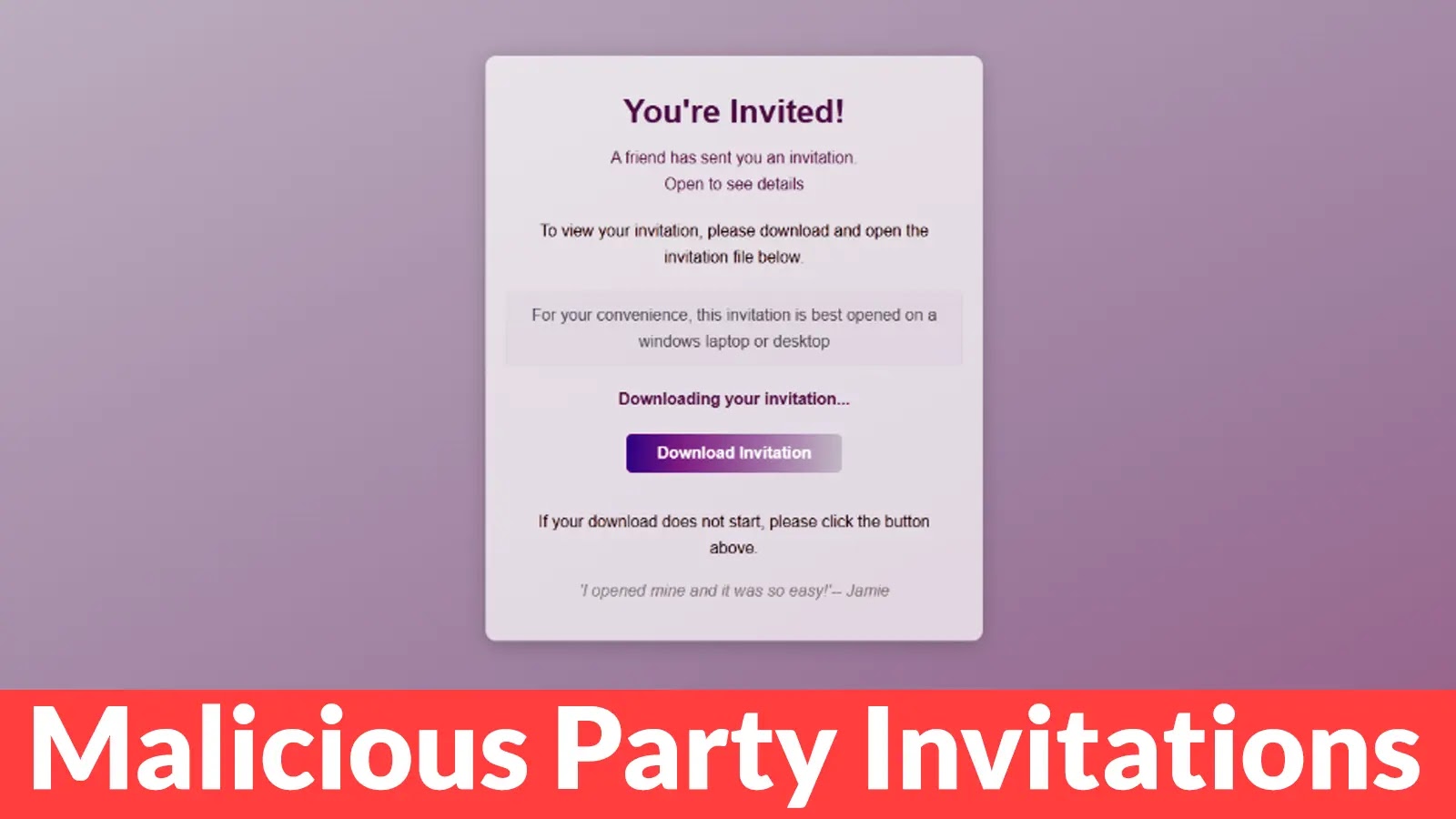
Imagine receiving a seemingly innocuous party invitation from a friend, only to find yourself unwittingly granting a cybercriminal full access to your computer. This isn’t [...]