—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Remote Code Execution Vulnerability in Google Chrome for Desktop Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: HIGH [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Multiple Vulnerabilities in HPE Aruba Products Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: HIGH Systems Affected HPE [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Vulnerability in Cisco Identity Services Engine (ISE) Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: MEDIUM Systems Affected [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Cross-Site Scripting Vulnerability in CISCO Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: MEDIUM Systems Affected Cisco EPNM [...]
—–BEGIN PGP SIGNED MESSAGE—– Hash: SHA256 Cross-Site Scripting Vulnerability in CISCO Indian – Computer Emergency Response Team (https://www.cert-in.org.in) Severity Rating: MEDIUM Systems Affected Cisco ISE [...]
A new security update for Google Chrome addresses a critical vulnerability within the browser’s Background Fetch API. Users are strongly advised to update their [...]
Urgent Alert: Fortinet FortiCloud SSO Vulnerability (CVE-2026-24858) Under Active Exploitation The cybersecurity landscape has been rocked by news of a critical authentication bypass vulnerability [...]
In the high-stakes world of enterprise cybersecurity, even the most established brands are not immune to the relentless threat of data breaches. Sportswear giant [...]
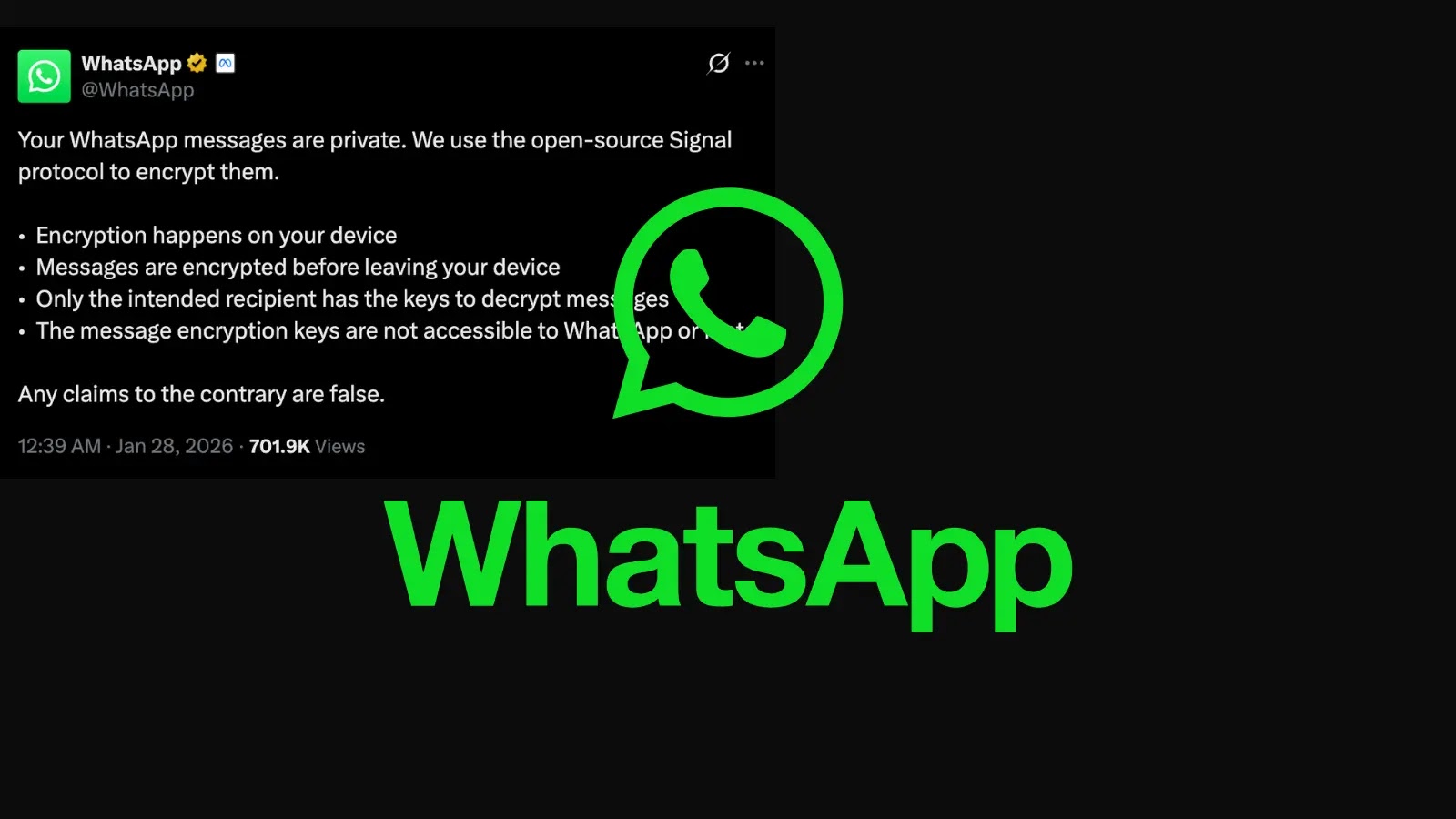
WhatsApp Confirms Message Privacy Amidst Lawsuit Claims: What You Need to Know In an era where digital privacy is paramount, a recent class-action lawsuit [...]
Chinese National Receives 46-Month Sentence for Multi-Million Dollar Crypto Laundering Scheme The digital frontier, while promising innovation and interconnectedness, also presents fertile ground for [...]