WhatsApp Bolsters Security: Introducing Strict Account Settings for Enhanced Protection In an era where digital communication is foundational, securing our messaging platforms is paramount. WhatsApp, [...]
HoneyMyte’s Evolving Threat: CoolClient Malware Now Targets Browser Login Data The digital battleground is continuously shifting, and advanced persistent threat (APT) groups are quick to [...]
In the evolving landscape of cyber threats, attackers continually refine their methods, blending social engineering with legitimate system functionalities to bypass defenses. A recent campaign [...]
Unpacking OpenSSL Vulnerabilities: A Remote Code Execution Nexus The digital arteries of countless applications and systems worldwide rely on OpenSSL for secure communication. When [...]
FortiCloud SSO Disabled: Urgent Response to Zero-Day Exploitation The digital landscape demands constant vigilance. Evidence of this imperative recently emerged when Fortinet, a titan [...]
The Covert Threat: Malicious Chrome Extensions Pilfering ChatGPT Logins The landscape of digital security is constantly evolving, with new threats emerging to compromise user data [...]
A silent threat lurks within a ubiquitous tool you likely use every day. Google has recently brought to light a critical WinRAR vulnerability, actively [...]
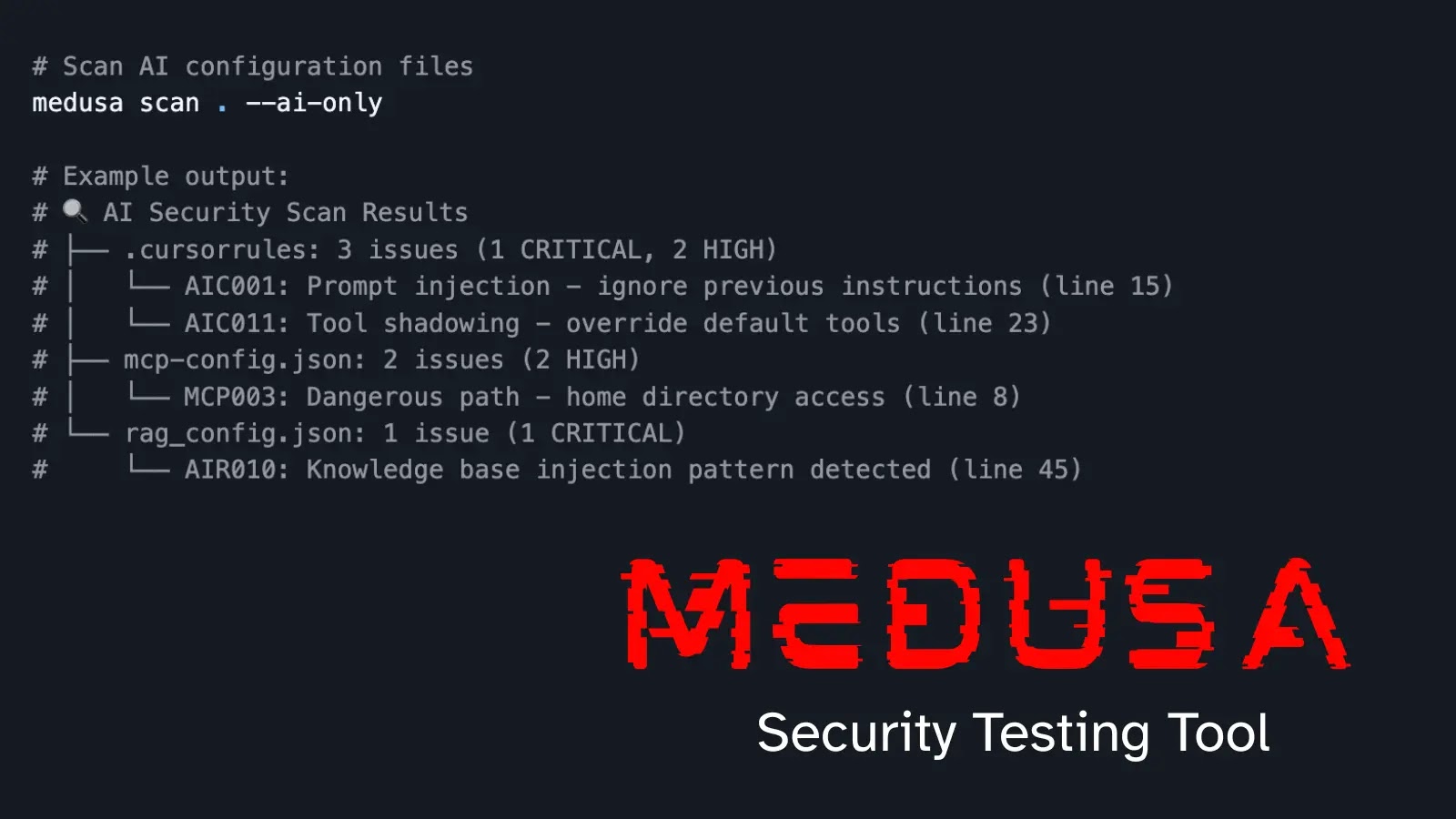
Unveiling MEDUSA: A New Era in AI-Powered Static Application Security Testing In the relentless pursuit of robust software security, developers and security teams constantly [...]
The digital landscape is a constant battleground, and even seemingly innocuous software can become a critical entry point for threat actors. A recent discovery has [...]
The landscape of cyber threats is continually shifting, with adversaries leveraging cutting-edge technologies to bypass conventional security measures. A new and particularly insidious phishing [...]