Unmasking Your Digital Footprint: Why VPNs Are Non-Negotiable in 2026 The digital landscape of 2026 demands a heightened vigilance for online privacy and security. With [...]
Ransomware continues its relentless evolution, and a new threat has emerged on the scene, demanding immediate attention from security professionals. Dubbed ‘Osiris,’ this ransomware family [...]
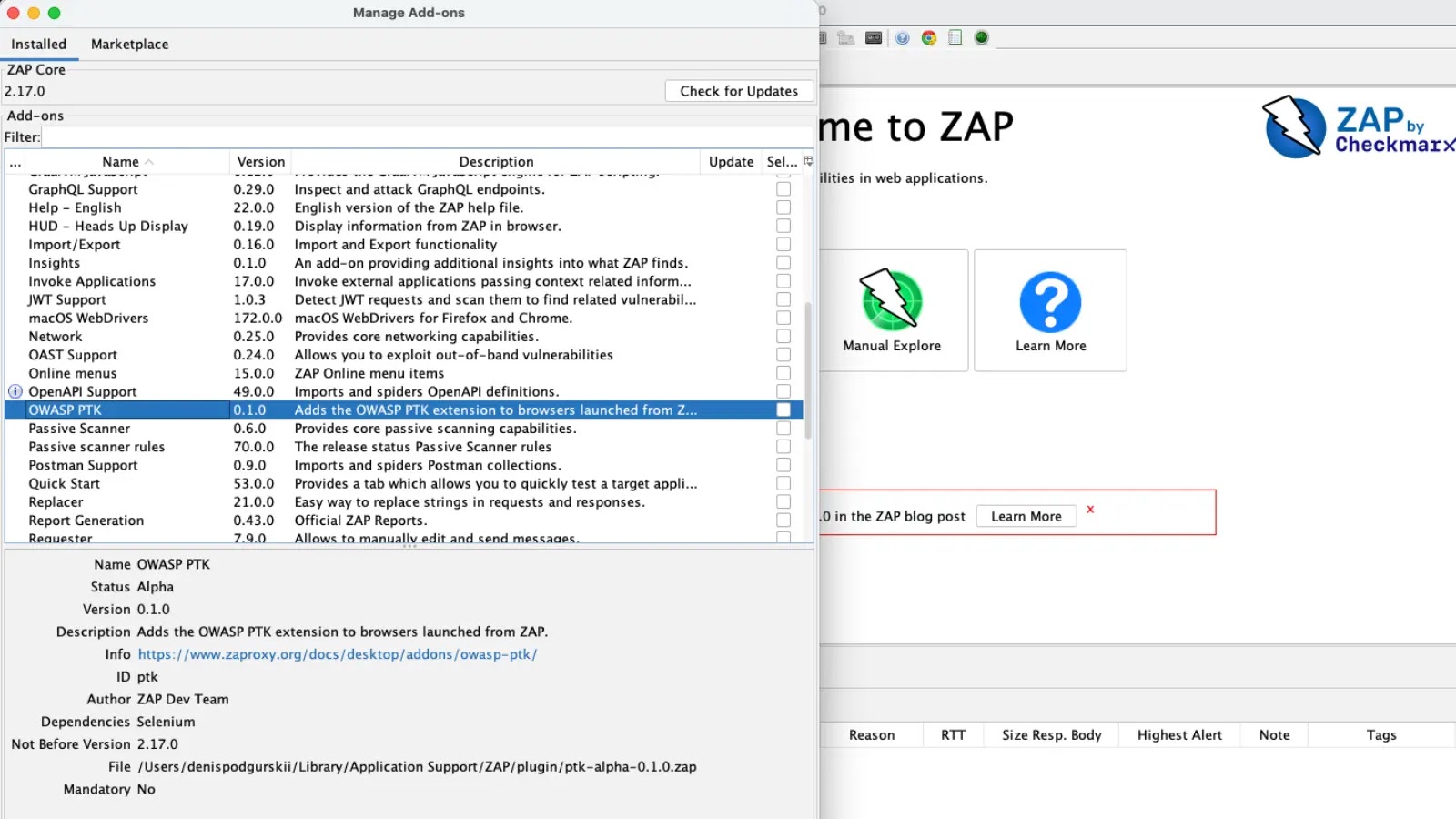
Application security testing can often feel like assembling a complex puzzle, with various tools and methodologies needing to be painstakingly integrated. The process of [...]
In a stark reminder that even global giants are not immune to sophisticated cyber threats, athletic apparel and footwear powerhouse Nike has reportedly fallen [...]
North Korean Hackers Leverage AI to Unleash Malware on Engineering Teams The landscape of cyber warfare has just taken a disturbing turn. North Korea-aligned [...]
The cybersecurity landscape just took a more insidious turn. A new generation of phishing kits is targeting enterprise users with unprecedented sophistication, leveraging voice-based [...]
Elevating Vulnerability Disclosure: Node.js Demands Higher Signal Scores on HackerOne The landscape of open-source software security relies heavily on the diligence of security researchers [...]
In the dynamic realm of software development, efficiency and accessibility are paramount. Microsoft has once again demonstrated its commitment to fostering innovation by unveiling the [...]
The Silent Compromise: AiTM Phishing Weaponizes SharePoint in Energy Sector Attacks In an alarming escalation of cyber threats, sophisticated adversary-in-the-middle (AiTM) phishing campaigns are [...]
Microsoft Teams to Pinpoint Your Work Location: A New Era for Workplace Monitoring? The lines between professional and personal life continue to blur, especially [...]