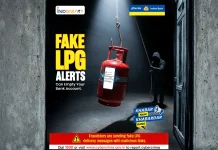
The digital landscape is a constant battleground, and cybercriminals are adept at leveraging current events and everyday necessities to ensnare unsuspecting victims. Indian Bank [...]
On April 7, 2026, the global cybersecurity landscape witnessed a significant victory against state-sponsored cyber espionage. The U.S. Justice Department and the FBI, in a [...]
Unpacking the Latest OpenSSL Vulnerabilities: RSA KEM Handling Exposes Sensitive Data The digital landscape is a constant battleground, and robust cryptographic libraries like OpenSSL are [...]
The landscape of artificial intelligence is rapidly evolving, with platforms like Flowise empowering developers to build sophisticated AI agents and custom large language model (LLM) [...]
In a stark reminder of the relentless pace of cyberattacks, a critical vulnerability dubbed React2Shell is being actively exploited, allowing attackers to compromise web [...]
The Stealthy Threat: Fake Gemini npm Package Targets AI Developers with Token Theft In the rapidly evolving landscape of artificial intelligence, developers are increasingly [...]
The Looming Threat: Kubernetes Misconfigurations as a Gateway to Cloud Accounts Kubernetes, the de facto standard for managing containerized applications, offers unparalleled scalability and [...]
The digital perimeter of critical infrastructure, particularly within global telecommunications, faces a constant barrage of sophisticated threats. Among these, Linux backdoors represent a particularly [...]
Unmasking the Critical CUPS Vulnerability Chain: Root Privileges at Risk The Common Unix Printing System (CUPS), a ubiquitous component in Unix-like operating systems, is [...]
In a development that underscores the evolving landscape of cybersecurity and the increasing prowess of artificial intelligence, a critical remote code execution (RCE) vulnerability within [...]