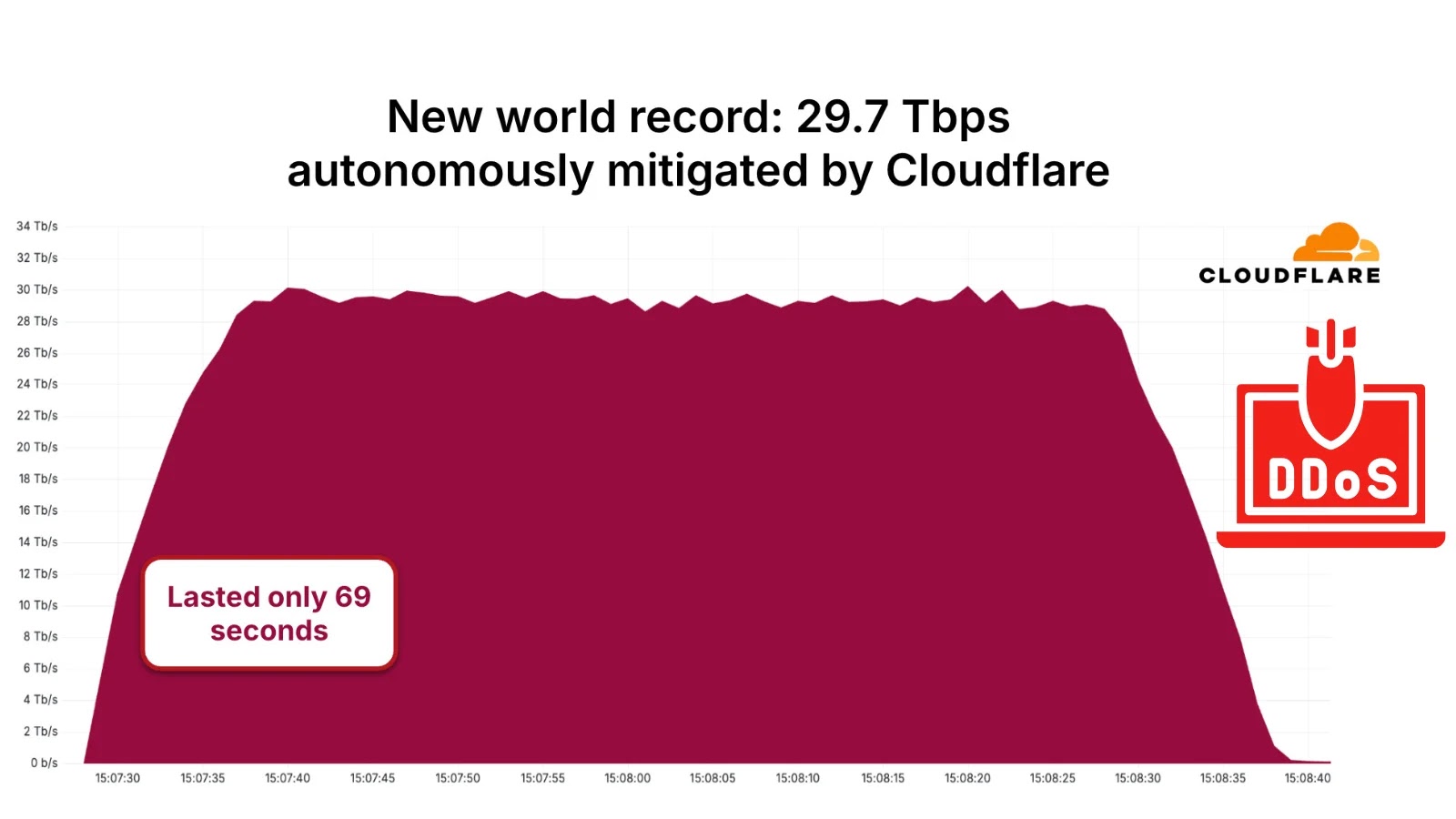
The internet, a foundational pillar of modern society, just experienced an unprecedented assault. A staggering 29.7 Terabits per second (Tbps) Distributed Denial-of-Service (DDoS) attack [...]
Yearn Finance yETH Pool Exploit: Unpacking the $9 Million Ethereum Heist The decentralized finance (DeFi) landscape was recently shaken by a sophisticated attack targeting Yearn [...]
Critical RCE Vulnerability Strikes Longwatch Surveillance Systems In a significant cybersecurity alert for industrial and critical infrastructure sectors, a severe Remote Code Execution (RCE) [...]
India’s New SIM-Binding Rule: What You Need to Know for Secure Messaging The landscape of digital communication in India is undergoing a significant shift. [...]
A disturbing new development in the cyber threat landscape has emerged, highlighting how advanced AI capabilities, specifically Anthropic’s Claude Skills, can be weaponized. Threat actors [...]
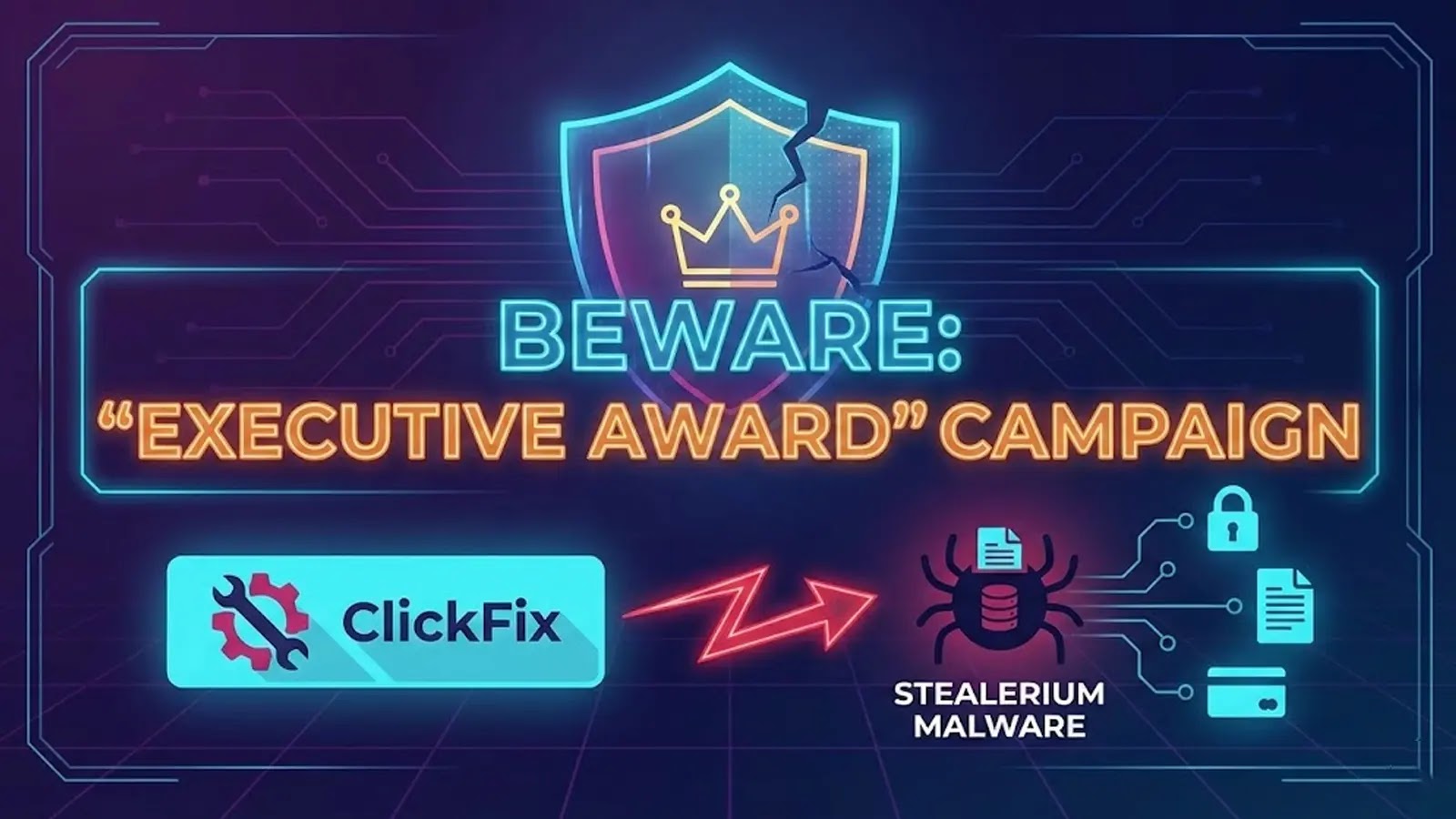
Unmasking the Executive Deception: A New Phishing Threat Delivering Stealerium Malware Organizations face an escalating threat from a sophisticated phishing campaign dubbed “Executive Award.” This [...]
A recent official confirmation from Microsoft has sent ripples through enterprise IT departments managing Windows 11 environments. A critical bug, initially triggered by July 2025 [...]
The security of critical infrastructure is paramount. A new warning from the Cybersecurity and Infrastructure Security Agency (CISA) highlights a severe authentication vulnerability impacting Iskra’s [...]
In the dynamic landscape of web development, frameworks like Angular are indispensable, powering countless applications with their robust features. However, even the most sophisticated systems [...]
A significant vulnerability within a widely used Elementor add-on has surfaced, presenting a critical threat to WordPress website security. Security researchers have sounded the alarm, [...]