Critical Apache Struts 2 Vulnerability: Protecting Your Data from XXE Attacks A severe security vulnerability has emerged in Apache Struts 2, placing countless applications [...]
In the relentless pursuit of robust malware detection, even the most sophisticated tools require continuous refinement. VirusTotal’s recent release of YARA-X version 1.11.0 marks a [...]
The landscape of digital communication is undergoing a significant transformation. With over 3 billion users relying on Gmail daily, any fundamental shift in its [...]
Unmasking the Threat: One-Click Telegram Flaw Exposes Real IP Addresses The digital landscape often promises anonymity, especially when users leverage tools like proxies to [...]
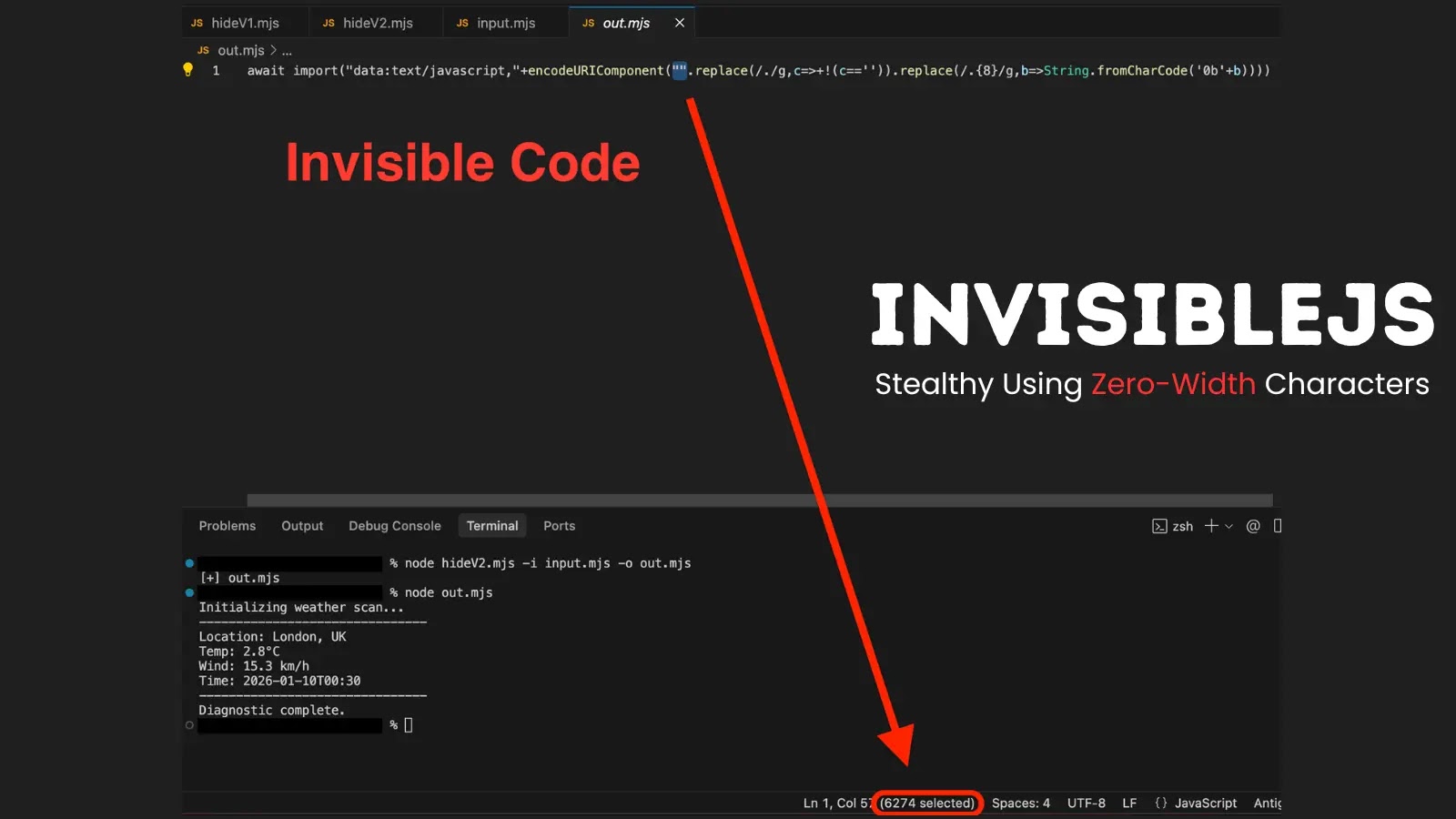
InvisibleJS: How Invisible Code Hides Dangerous Payloads in Plain Sight The digital landscape is constantly evolving, with new threats emerging that challenge conventional cybersecurity [...]
When Community Trust Turns Treacherous: The n8n npm Package Infiltration The digital supply chain, an increasingly interconnected web of software components and third-party integrations, [...]
India is facing an alarming surge in mobile cyberattacks, solidifying its position as the global epicenter for mobile threats. Recent findings from the Zscaler [...]
The integrity of modern software hinges on proactive security measures. As development cycles accelerate and applications grow in complexity, integrating robust code security tools [...]
As we advance deeper into 2026, the landscape of Linux system administration continues to evolve, demanding more sophisticated yet intuitive tools. Efficiently managing, monitoring, [...]
Navigating the Cyber Labyrinth: Top Cybersecurity Companies for 2026 The relentless drumbeat of cyber threats continues to escalate, pushing organizations to their breaking point. [...]